Seeing is believing.
See Orca Security in action.
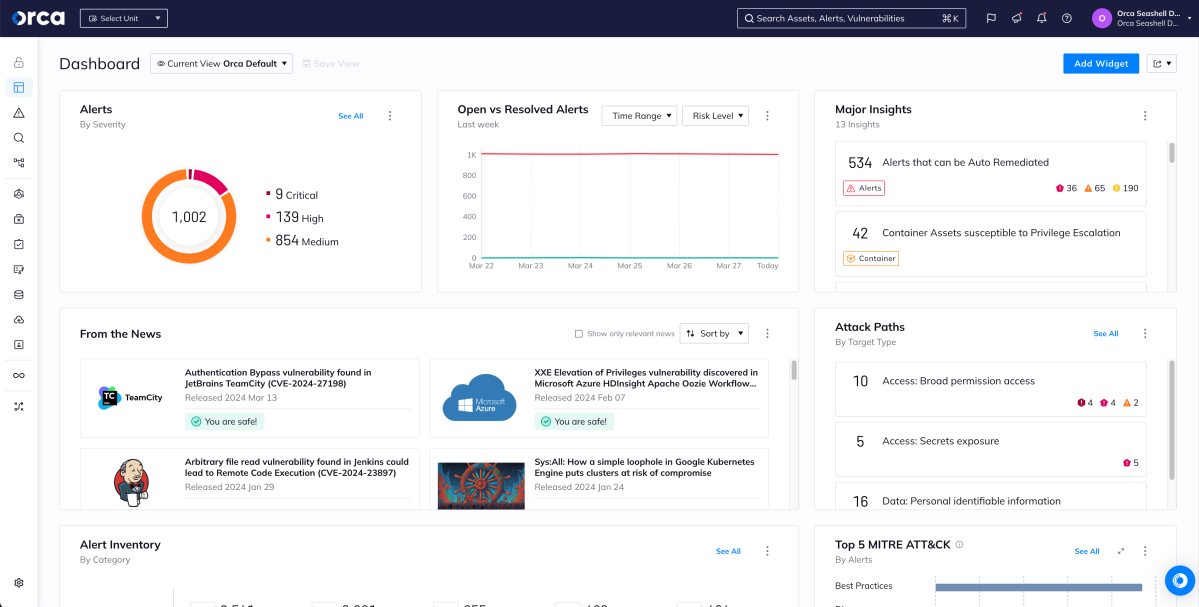
Gain visibility, achieve compliance, and prioritize risks with the Orca Cloud Security Platform.
“Orca adds value practically from the first day of use. With other tools, we wait months to see value coming from them.”
Vivek Menon, VP and CISO, Digital Turbine
4.8
on
4.6
on
4.6
on
Sign up for a demo today
Our cloud security experts will walk you through a personalized demo curated for your business.