Table of contents
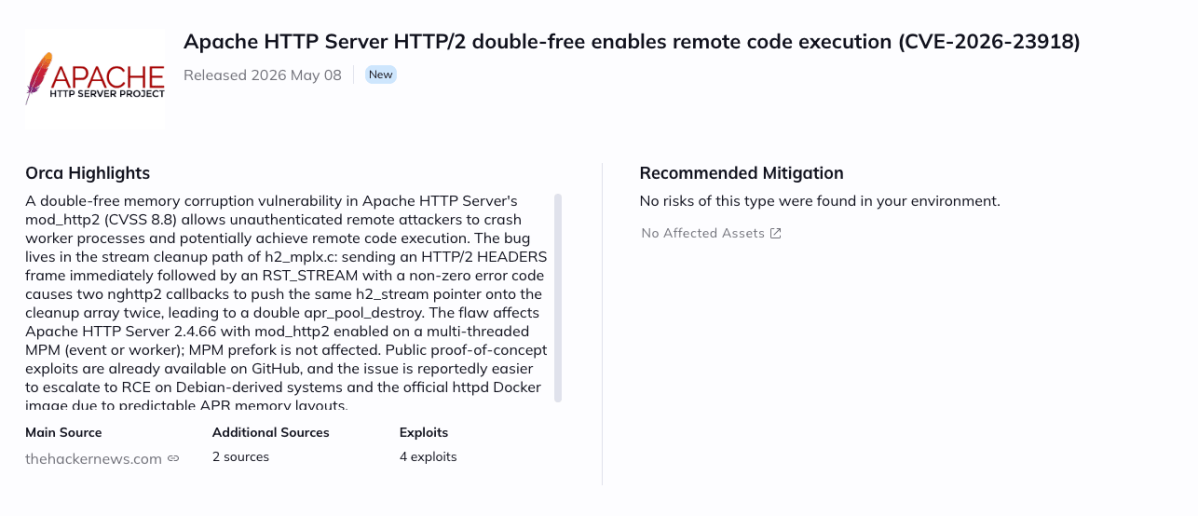
A high-severity vulnerability (CVE-2026-23918, CVSS 8.8) was disclosed affecting Apache HTTP Server, allowing attackers to potentially achieve remote code execution via specially crafted HTTP/2 requests. Due to the potential for server compromise and denial-of-service conditions, immediate patching is strongly recommended.
About the Vulnerability: CVE-2026-23918
The issue originates from Apache’s HTTP/2 protocol handling in mod_http2, where a double-free memory corruption flaw in the stream cleanup logic can lead to heap corruption and possible remote code execution. By sending specially crafted HTTP/2 HEADERS frames followed by an early RST_STREAM request with a non-zero error code, attackers can trigger the vulnerable code path, potentially causing service crashes or gaining arbitrary code execution on affected servers. No authentication is required to exploit this issue.
The following component is affected: Apache HTTP Server mod_http2 in version 2.4.66. The vulnerability was addressed in Apache HTTP Server version 2.4.67.
Apache HTTP Server remains one of the most widely deployed web servers globally and is commonly used across Linux distributions, cloud-hosted applications, enterprise reverse proxies, containerized workloads, and internet-facing environments. Deployments with HTTP/2 enabled are particularly exposed. Other services or products embedding vulnerable Apache HTTP Server versions may also be impacted.
Risk Impact
At the time of writing, public proof-of-concept technical details discussing exploitation conditions are already available, although no confirmed in-the-wild exploitation has been publicly reported. Regardless, the severity and low complexity of exploitation make this vulnerability high risk, especially for internet-facing deployments.
Successful exploitation could allow attackers to crash vulnerable web servers, execute arbitrary code, bypass availability protections, and potentially pivot deeper into internal infrastructure, leading to service disruption, sensitive data exposure, or full server compromise.
Mitigation Recommendations
Users should immediately upgrade to Apache HTTP Server 2.4.67, which addresses the underlying memory handling flaw. Organizations unable to patch immediately should consider temporarily disabling HTTP/2 support until upgrades can be completed.
How can Orca help?
Orca enables customers to quickly identify assets running vulnerable Apache HTTP Server versions, understand their exposure in context, including internet accessibility, runtime reachability, and asset criticality, and prioritize remediation based on real risk rather than CVSS alone. Orca’s platform highlights affected assets directly in the alert view, helping security teams focus on the most critical remediation paths first.