How Orca Security Compares to Check Point CloudGuard
Customers choose Orca’s comprehensive, holistic platform over Check Point’s CloudGuard
SideScanning enables deeper insight
Orca’s patented SideScanning technology quickly and easily scans all of your Linux and Windows workloads, including cloud VMs, containers and Kubernetes applications, and serverless functions without having to deploy additional agents or configurations within a single license. Check Point CloudGuard has limited, agentless scanning in some clouds while, for others, you have to deploy and maintain complex agents; additionally, some functionality may require purchasing additional licenses.
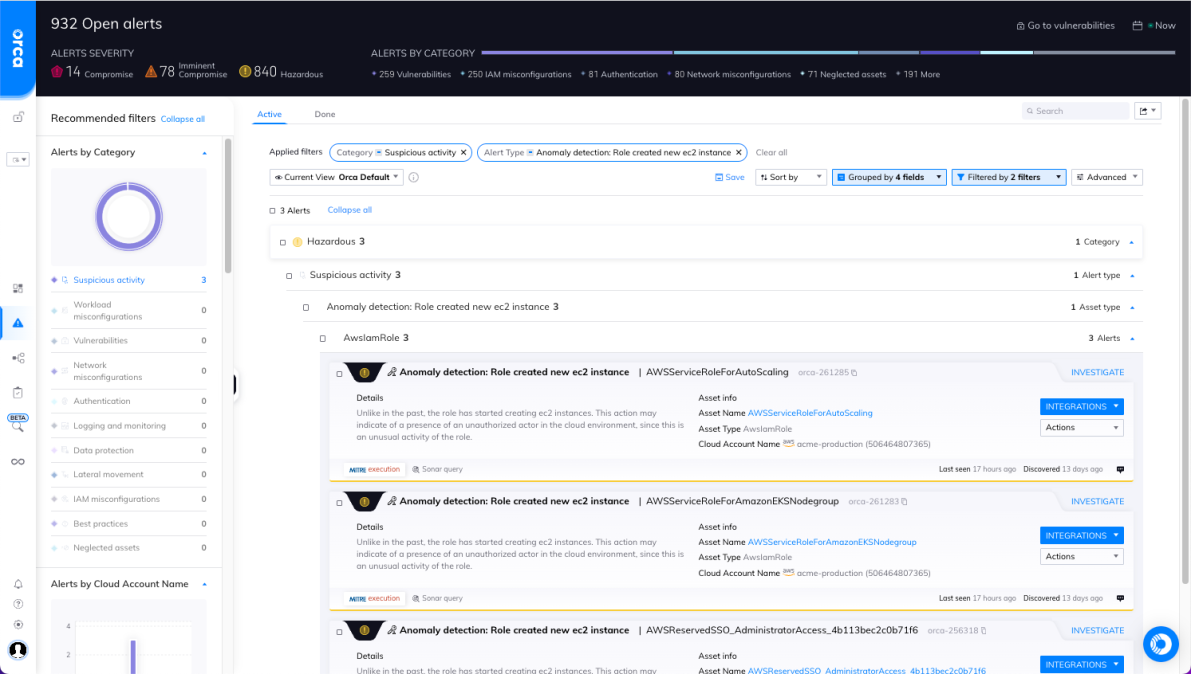
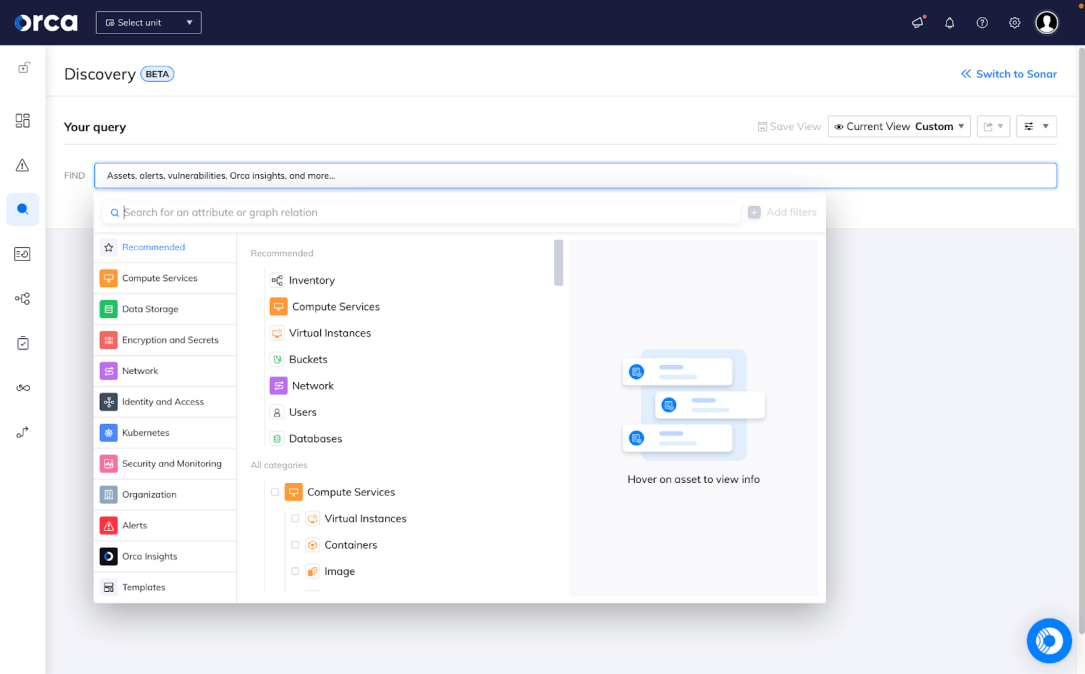
Unified data for risk prioritization
The Orca Platform brings all of your data into a unified, easily-queryable location. With Orca’s Unified Data Model, you can view assets, compliance status, risks, and security incidents from one dashboard across cloud infrastructure and workloads. Check Point CloudGuard was built from different acquisitions and products so, instead of a unified platform, information is spread across multiple silos. Orca can show you the whole picture.
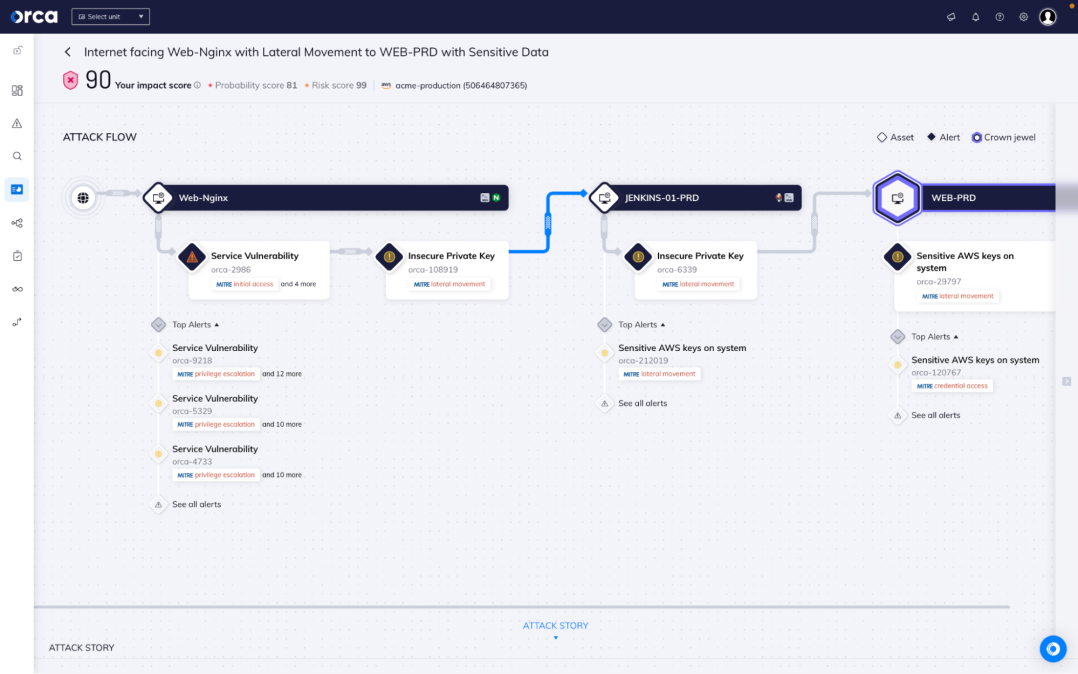
Identify sensitive data in your cloud
Orca Security automatically identifies and classifies data such as PII(Personally identifiable Information), credit card numbers, and PHI(Protected Health Information) in storage buckets, VMs, and databases. When you combine this with automated attack path analysis, Orca shows you where critical information is at risk even if it would take an attacker multiple steps to get to it. Check Point CloudGuard doesn’t know what data is critical or where it lives, leaving you dealing with too many false alarms.
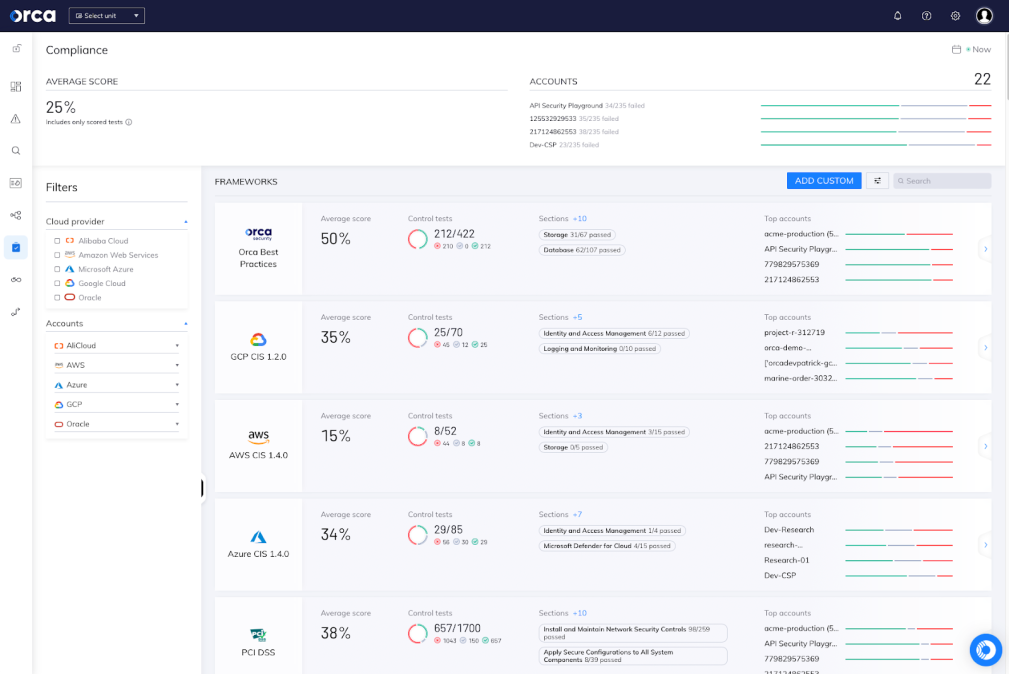
Comprehensive compliance for your entire cloud
Orca supports over 100 compliance frameworks, as well as our own Orca Best Practices and custom frameworks. This ensures that you can view compliance in a single dashboard and report covering your cloud infrastructure, data, identities, workloads, and more.
Features
Vulnerability Management
Simple & Complete
With a single, agentless deployment, assess vulnerabilities across all VMs and containers in your cloud environment
Complex
Vulnerability scanning requires different approaches in different clouds or integration with 3rd party services like AWS Inspector
Asset Inventory
Unified
Continuously monitor public cloud services and configurations, entitlements and identities, workloads and applications, all from a single dashboard
Fragmented
Infrastructure and workload information is fragmented across multiple silos
Compliance
Comprehensive
100+ compliance frameworks with all data and policies shown in a single dashboard for seamless reporting
Basic Coverage
Fewer compliance frameworks, covering only cloud infrastructure, leaves your auditors doing far more work
Attack Path Analysis
Automated and Interactive
Interactive dashboard, with automated impact score, surfaces toxic combinations of risks so teams can prioritize and fix the top 1% of issues. All risks mapped to the MITRE ATT&CK framework
Very Limited
Check Point CloudGuard has no concept of risk across assets – no attack paths, no toxic combinations. Each asset is scored on its own, making it harder to find the multi-step approaches that attackers use
PII Detection
Seamless and Comprehensive
Automatic detection of PII across all cloud resources
No Sensitive Data Detection
With no data classification at all, Check Point CloudGuard leaves you guessing on critical assets
API Security
Simple and Comprehensive
Automated inventory of all interconnected APIs and web domains. Capabilities integrated with agentless SideScanning technology, nothing new to activate. Prioritize risks, including external exposure, mapped to OWASP API Security Top 10 and contextualized with all other risks
No API Security
Check Point CloudGuard doesn’t assess exposed API endpoints or provide meaningful views of what is deployed & running

Personalized Demo
See Orca Security in Action
Gain visibility, achieve compliance, and prioritize risks with the Orca Cloud Security Platform.

Chat with Us
See Orca Security in Action
Gain visibility, achieve compliance, and prioritize risks with the Orca Cloud Security Platform.
No Slack account required.