Agentless-First Cloud Security for Google Cloud
Get complete visibility and security for your entire Google Cloud environment, including databases, cloud storage, workloads, applications, and more–integrated across the full stack and application lifecycle.
Orca is Deeply Integrated with Google Cloud
Orca is a Google Cloud partner, and is integrated with 100+ Google Cloud services and products, including GCE, GKE, Cloud Run, Cloud Functions, VirusTotal, Chronicle SOAR, Security Command Center, Google Pub/Sub, Workspaces, Vertex AI, and more. Orca is available for purchase in the Google Cloud Marketplace.
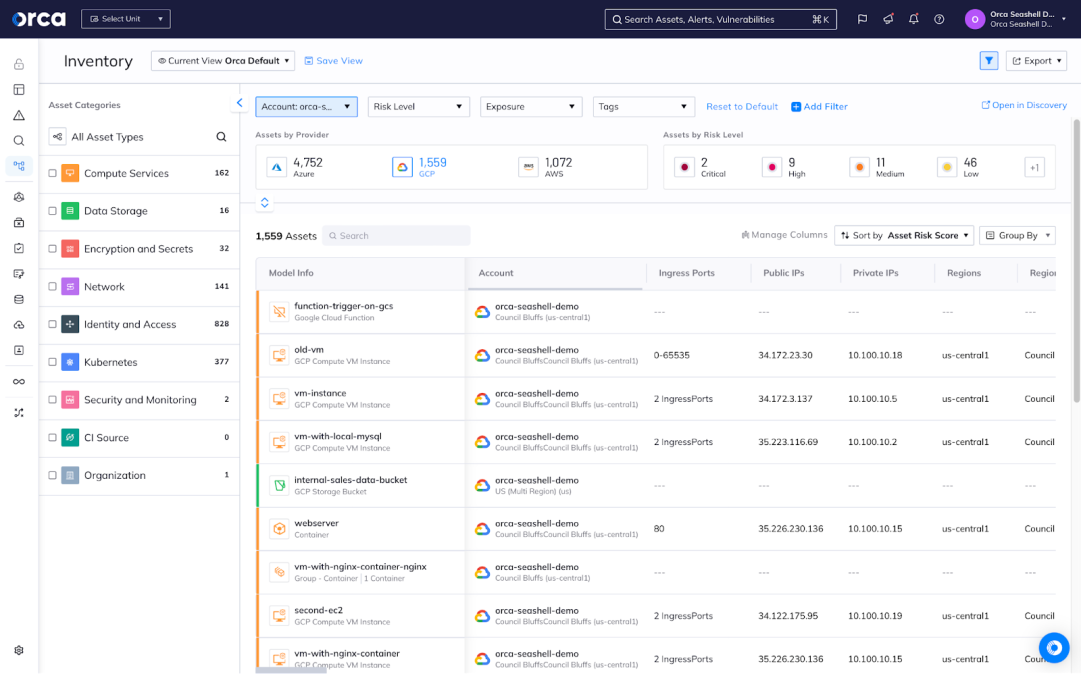
Detect critical security risks in your Google Cloud environment
Orca’s SideScanning™ technology reads your cloud configuration and workloads’ runtime block storage out-of-band to create a complete risk profile of your Google Cloud estate in minutes.
- Covers all your Google Cloud workloads – VMs, containers, and serverless, including GCE, GKE, Cloud Run, and Cloud Functions
- Detects vulnerabilities, malware, misconfigurations, IAM risk, lateral movement risk, API risk, unsecured sensitive data, and much more
- By integrating with Google Cloud services and delivering an agentless-first approach, Orca provides comprehensive security across your Google Cloud environment quickly
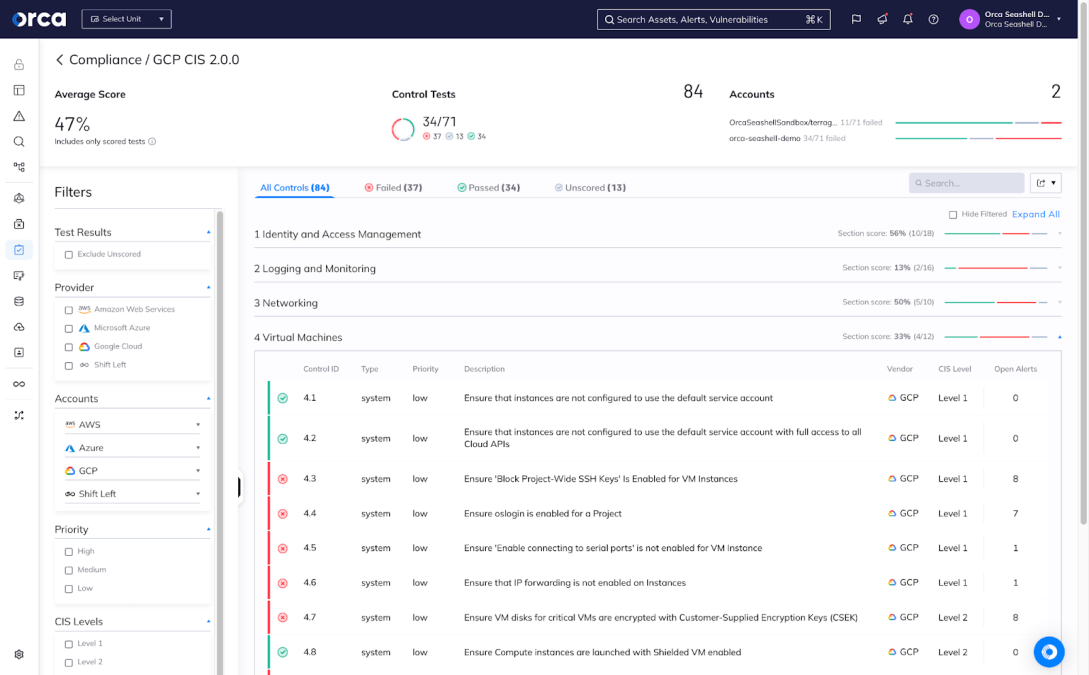
Simplify Google Cloud compliance with a single platform
Achieve continuous compliance more easily that ever before with a single cloud security platform that covers 100% of your Google Cloud environment, avoiding compliance gaps and failed audits:
- Meet over 100 compliance frameworks and key CIS benchmarks, including NIST 800-53, SOC 2, ISO 27001, Google Cloud CIS, Docker CIS, Apache CIS, and Windows CIS, to name a few.
- Demonstrate your ability to meet key data privacy mandates in your Google Cloud environment, including PCI-DSS, GDPR, HIPAA, and CCPA.
- Leverage Orca’s built-in compliance templates, or customize them to meet your specific needs.
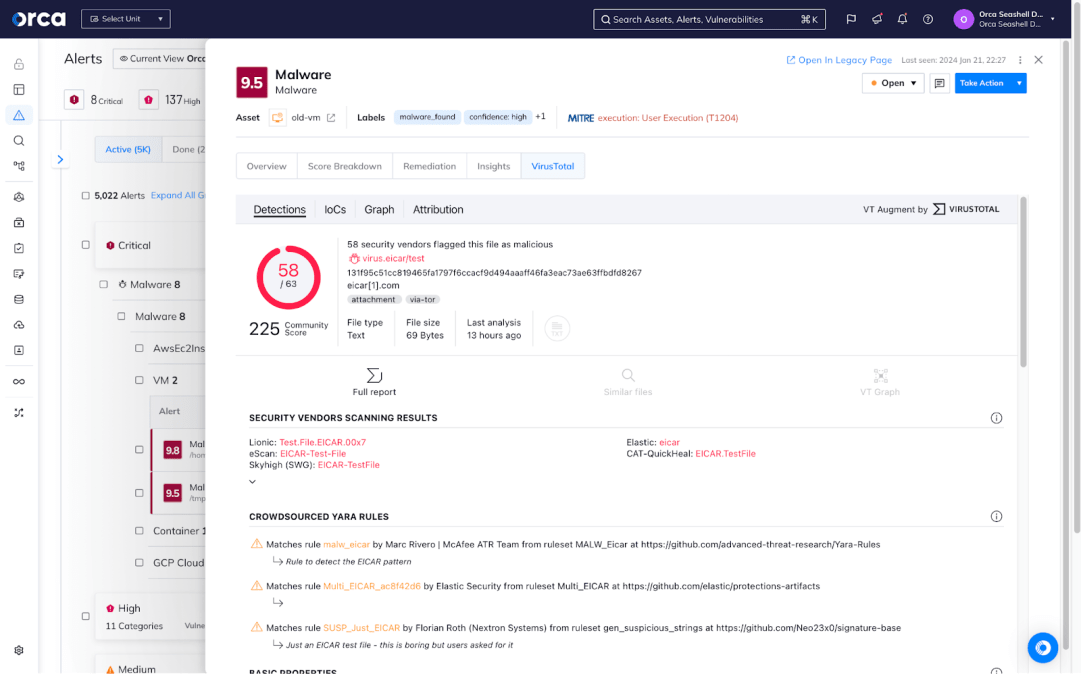
Integrated with Google Cloud security services like VirusTotal and Chronicle
Orca integrates with leading Google Cloud security services, like VirusTotal and Chronicle, to augment alerts and add contextual information to provide the basis for risk prioritization. Together, the platforms allow mutual customers to continuously monitor malicious activity and unauthorized behavior while empowering faster remediation.
- Better Visualization: See how this alert might play a role in a much larger attack path that could lead to the compromise of more sensitive data.
- More Context: Understand why an alert matters with a summary digest, along with recommended remediations.
- Accurate Classification: Group VirusTotal and other Google Cloud alerts together based on compliance, severity, asset or risk type.
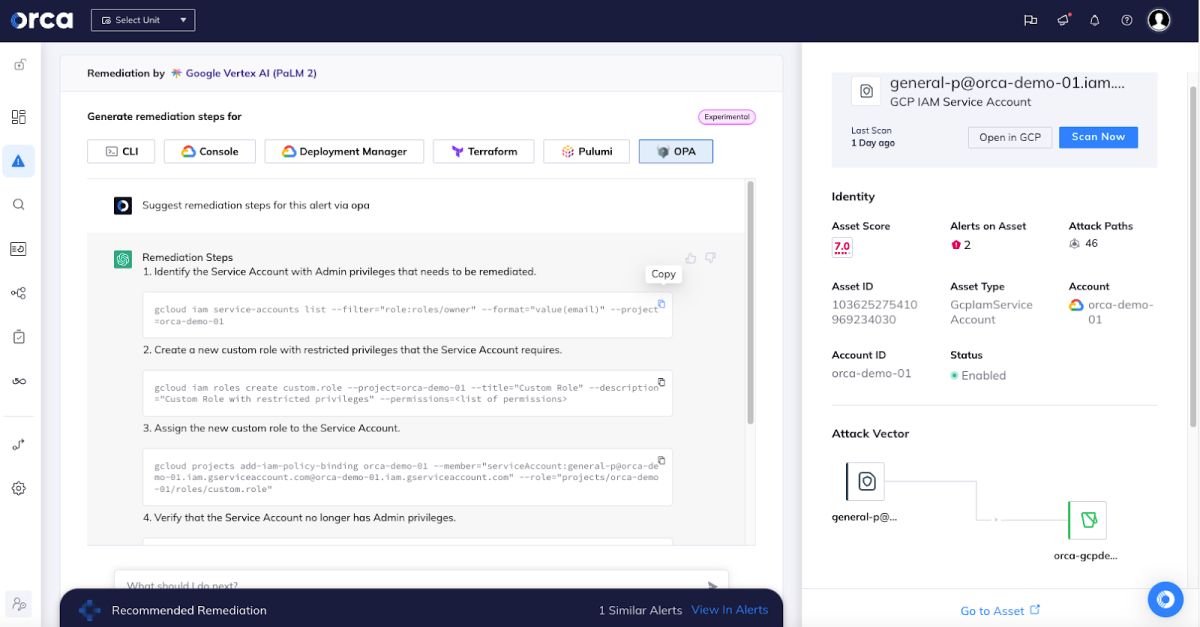
Accelerate remediation using AI-powered remediation with Google Vertex AI
Instantly generate high-quality remediation instructions for each alert straight from the Orca Platform, enabling your team to address cloud vulnerabilities and risks 2-3 times faster. Data privacy is ensured by anonymizing requests and masking any sensitive data.
- Copy and paste remediation code into a command line interface or Infrastructure as Code (IaC) provisioning tools, or follow steps in the console.
- Leverage Google Vertex AI as your AI engine to save teams’ time and effort.
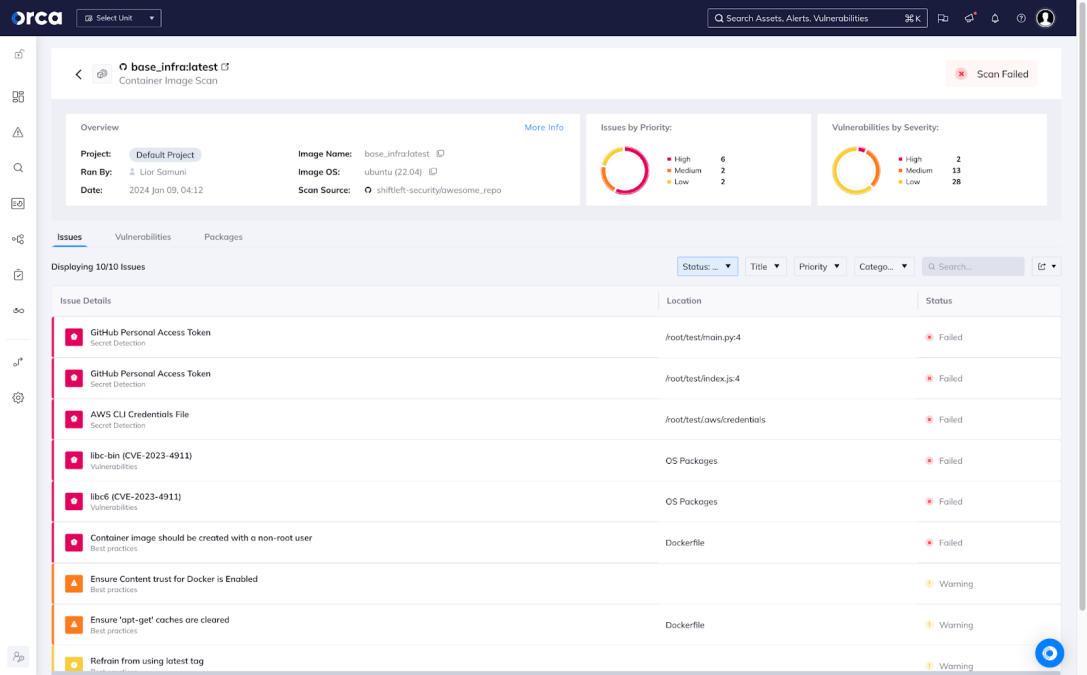
Integrate security into your CI/CD workflows
Orca integrates with all of the Google Cloud services and tools you use to build and deploy your applications. This ensures that critical risks are identified before they reach production environments, ensuring security is implemented by design.
- Integrated with Google Cloud tools: Orca integrates with Google Cloud Build, as well as third-party CI/CD tools, to automate IaC and container image scans as you build and deploy your applications.
- Support for IaC templates and container images: Orca supports CloudFormation, as well as HashiCorp Terraform of Kubernetes yaml, as well as modern container image formats.
- Simplified policy management: Easily manage and customize over 1000+ policies, or leverage Orca’s pre-built best practices to improve code quality pre-deployment.
About Orca and Google Cloud
Orca is a Google Advantage Partner. CapitalG Alphabet’s independent growth fund led Orca’s Series C Financing. Orca is integrated with multiple GCP services and products including G Suite SSO and Google Pub/Sub integrations. Orca is available for purchase on the Google Cloud Marketplace.
Featured Content for Orca Security for Google Cloud

Personalized Demo
See Orca Security in Action
Gain visibility, achieve compliance, and prioritize risks with the Orca Cloud Security Platform.

Chat with Us
See Orca Security in Action
Gain visibility, achieve compliance, and prioritize risks with the Orca Cloud Security Platform.
No Slack account required.