Lateral Movement Risk Detection
Orca detects risks and vulnerabilities that could enable lateral movement in your cloud estate and recommends remediation steps to strengthen your security posture.
The Challenge
Exposed keys enable lateral movement
Attackers often exploit multiple assets to reach their end goal. They use their initial foothold to scan connected assets for unencrypted keys and other information that might allow them to move to the next target.
- 90% of organizations have at least one asset that enables lateral movement.
- 72% of organizations have public-facing assets at risk for lateral movement.
- Many solutions detect lateral movement only after it has occurred or are blind to crucial contextual information, such as access to the public internet, that would otherwise trigger an alert.
Our Approach
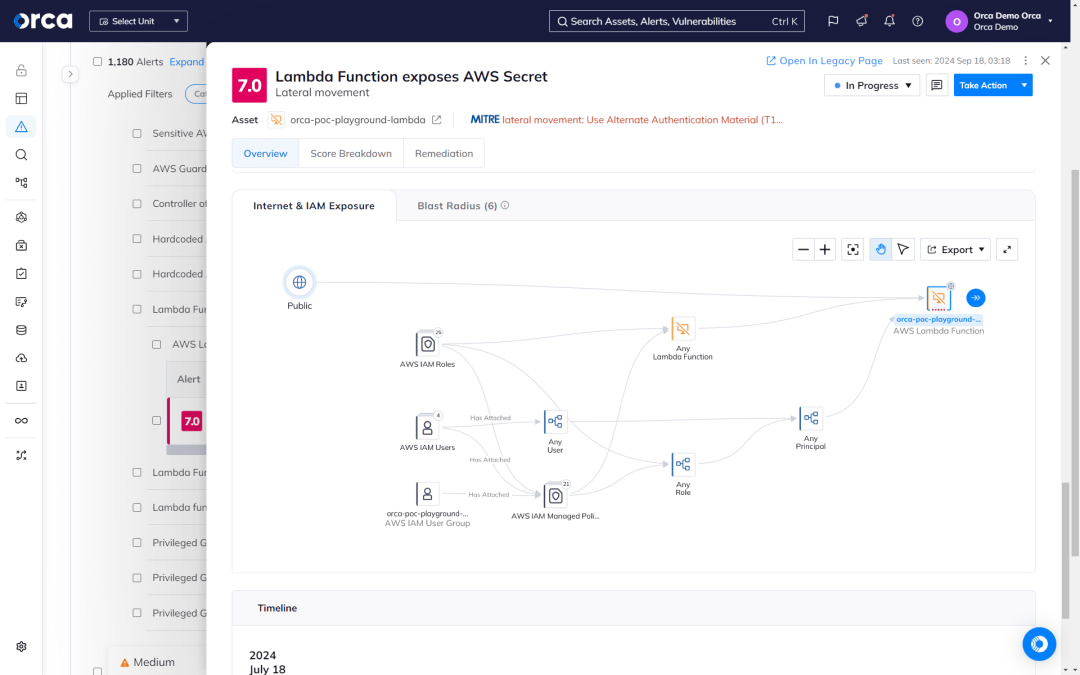
Discover and remediate lateral movement risk
The Orca Platform combines full cloud coverage and deep insights to discover the unprotected keys, passwords, and other information that an attacker could use to move laterally in your environment. Orca also surfaces the interconnected risks between cloud assets that attackers can exploit to endanger your crown jewels.
Detect insecure private keys
Orca scans each machine’s filesystem for private keys, creates hashes, and then scans all other assets for authorized public key configurations with matching hashes. In addition to keys, Orca provides key-related information such as:
- Paths to insecurely stored keys
- Identities of assets that can be accessed with exposed keys
- Exposed secrets on serverless function compute resources

Prevent lateral movement attacks
Virtual Machine A has an unpatched operating system and permissive service account that can access Virtual Machine B, which exposes sensitive keys. Most tools would fail to recognize the risk of lateral movement, requiring deep insight into the relationship between cloud assets and risks. Orca would not only detect and effectively prioritize this risk, but continually assess its criticality as conditions in your environment change.

Find exposed credentials before your adversaries
Attackers often search for credentials that have been exposed inadvertently during the software development process. Orca detects these risks by scanning the following:
- Shell histories for inadvertently stored passwords
- Git repositories for keys and access credentials
- Development-related systems that might be storing public cloud keys

Complete coverage and visibility

Personalized Demo
See Orca Security in Action
Gain visibility, achieve compliance, and prioritize risks with the Orca Cloud Security Platform.

Chat with Us
See Orca Security in Action
Gain visibility, achieve compliance, and prioritize risks with the Orca Cloud Security Platform.
No Slack account required.

