How Orca Security Compares to Qualys TotalCloud
Orca Leads with a Purpose-Built Platform
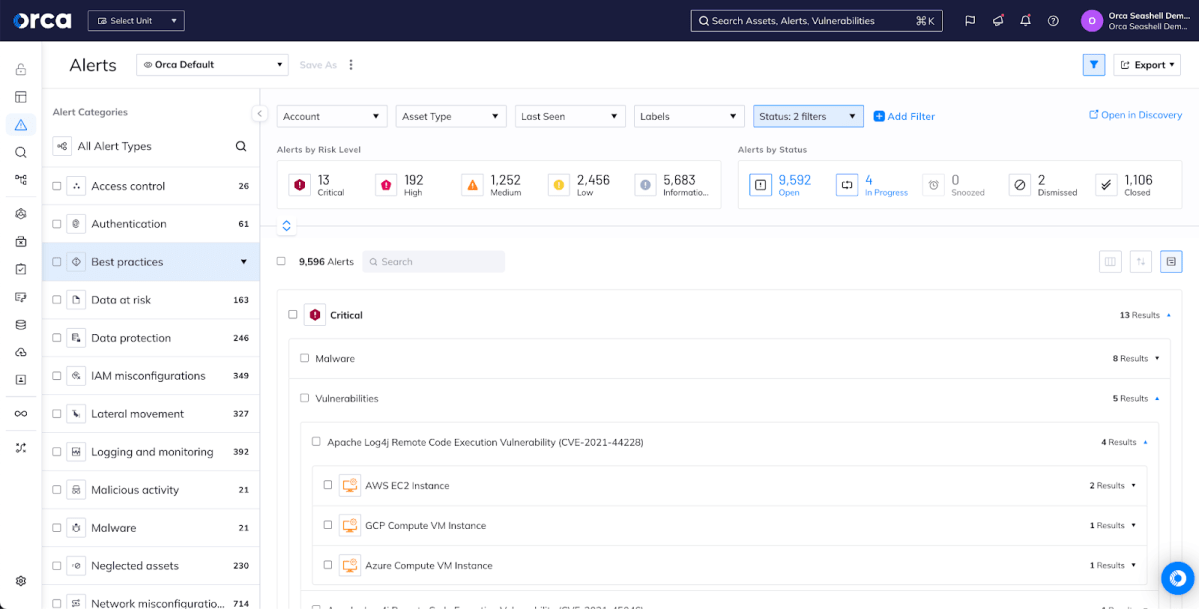
Qualys has built on a core competency in vulnerability assessment, adding basic cloud discovery & configuration assessments and SOAR capabilities into Qualys TotalCloud. While this approach provides basic functionality, TotalCloud requires a complex mix of agentless configuration and several different agents to get there. Even with all of this configured & deployed, TotalCloud doesn’t match Orca’s abilityto provide assessment & protection across VMs, workloads, control planes, data, API endpoints, and more.
Features
Deployment
Easy Onboarding
Simple 3-step activation model scans your cloud accounts, assets, workloads, data, and identities across multiple clouds without having to deploy agents
Complex Deployment
Mix of agentless and multiple agents means that you spend far longer deploying TotalCloud and more energy worrying about what you’ve missed.
Asset Inventory
Unified
Continuously monitor public cloud services and configurations, entitlements and identities, workloads and applications, all from a single dashboard
Limited
No coverage for identities, entitlements, API endpoints. Data classification limited to only data stored in S3 buckets.
Compliance
Centralized
125+ compliance frameworks with all data and policies shown in a single dashboard for seamless reporting
Basic Coverage
Only covers CIS, cloud provider, and Qualys frameworks, leaving you to do all the work for the compliance frameworks that matter to you.
Attack Path Analysis
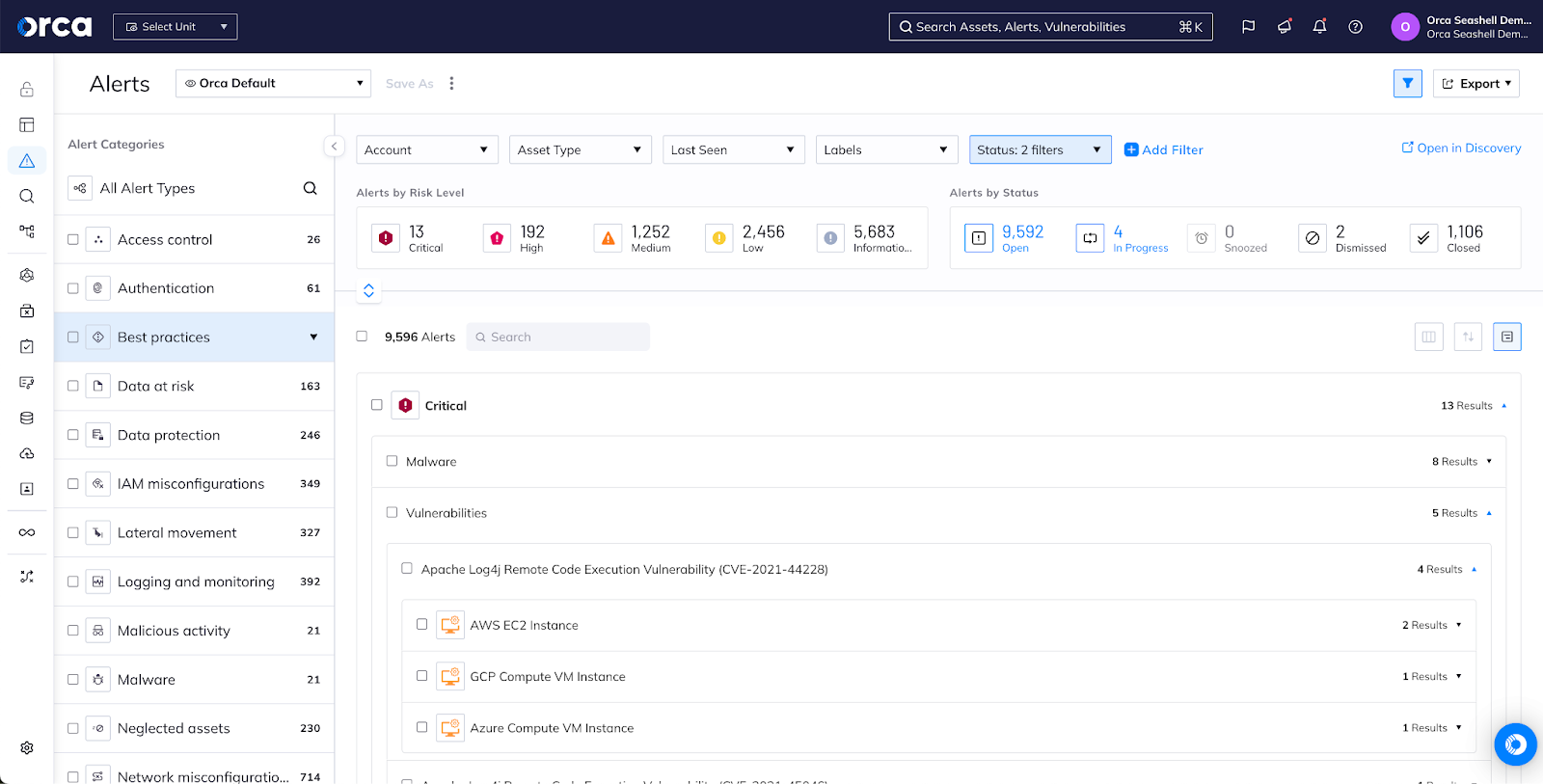
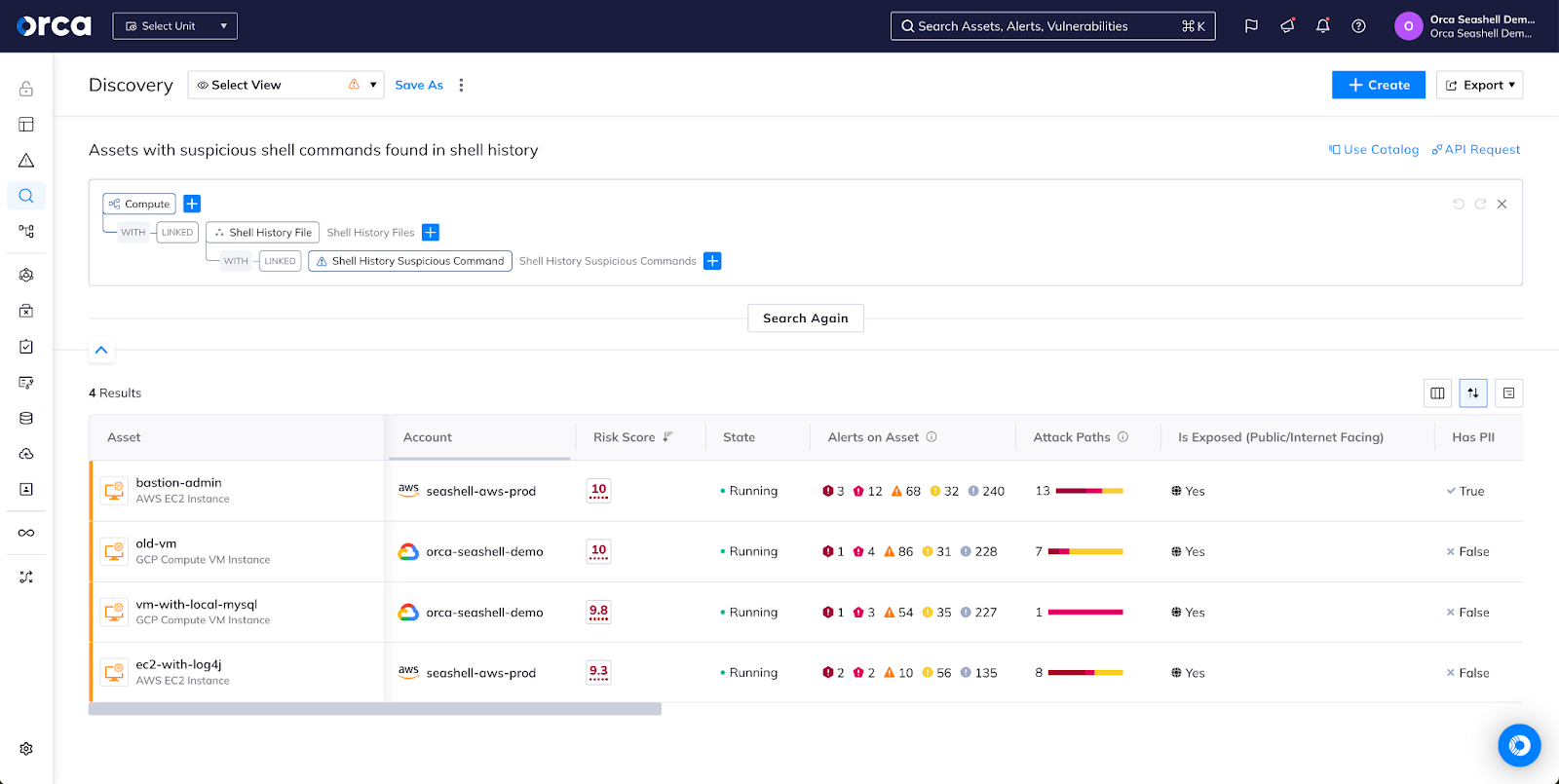
Automated and Interactive
Interactive dashboard, with automated impact score, surfaces toxic combinations of risks so teams can prioritize and fix the top 1% of issues. All risks mapped to the MITRE ATT&CK framework
Very Limited
TotalCloud can’t show you how an attacker would exploit multiple steps to get to critical data; instead, it just shows which endpoints are exposed externally.
PII Detection
Seamless and Comprehensive
Automatic detection of PII across all cloud resources
Limited Detection
No detection outside of storage buckets.
Shift Left Security
Comprehensive with Context
One CLI and dedicated Shift Left Dashboard for viewing all of your container image and IaC scans. IaC coverage for a wide range of IaC platforms from Terraform, Cloud Formation, and Azure Resource Manager to Ansible to Kubernetes.
Limited Coverage
Limited IaC scanning (Terraform, Cloud Formation, and ARM only) No centralized policies means that pass/fail criteria are set for every job.
API Security
Simple and Comprehensive
Automated inventory of all interconnected APIs and web domains. Capabilities integrated with agentless SideScanning technology, nothing new to activate. Prioritize risks, including external exposure, mapped to OWASP API Security Top 10 and contextualized with all other risks
No API Security
TotalCloud doesn’t assess exposed API endpoints or provide meaningful views of what is deployed & running.
A purpose-built platform to simplify cloud security
With Orca Security, you benefit from a purpose-built Cloud Security Platform that addresses all of your cloud risks and features our patented SideScanning technology that covers your entire cloud estate without agents. Orca continues to innovate and provide visibility into wherever threats may live in your cloud environment, including everything from IAM to API endpoints.
TotalCloud is built from a number of different components, resulting in a complex deployment with a mix of agentless & agent-based approaches. Once fully deployed, TotalCloud provides a less holistic view of risks to the cloud.
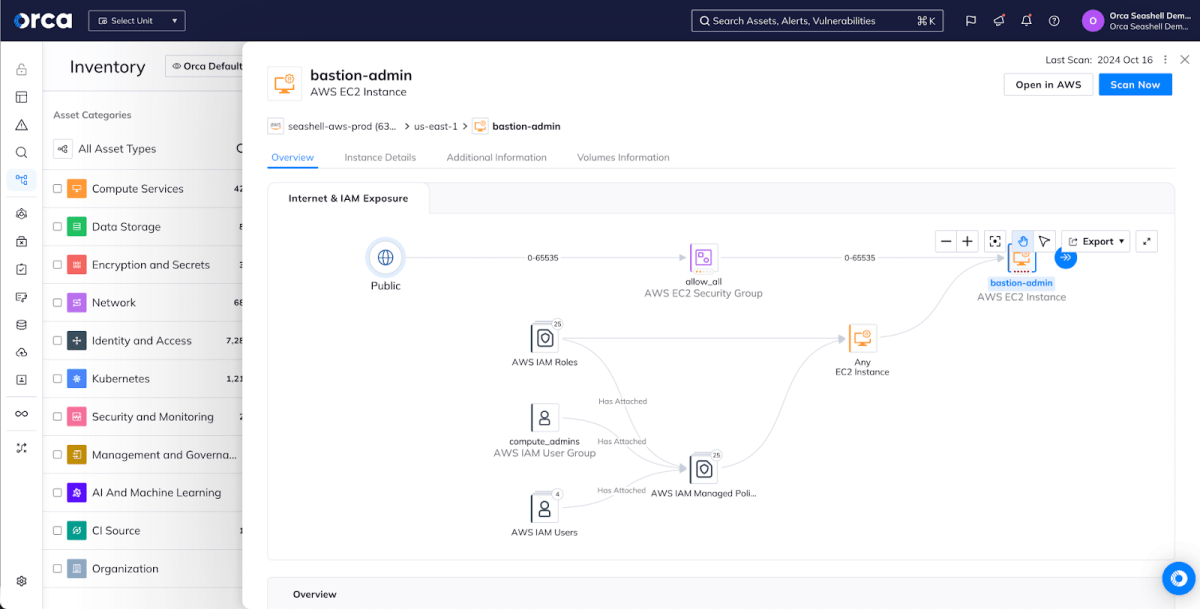
The agentless security pioneer
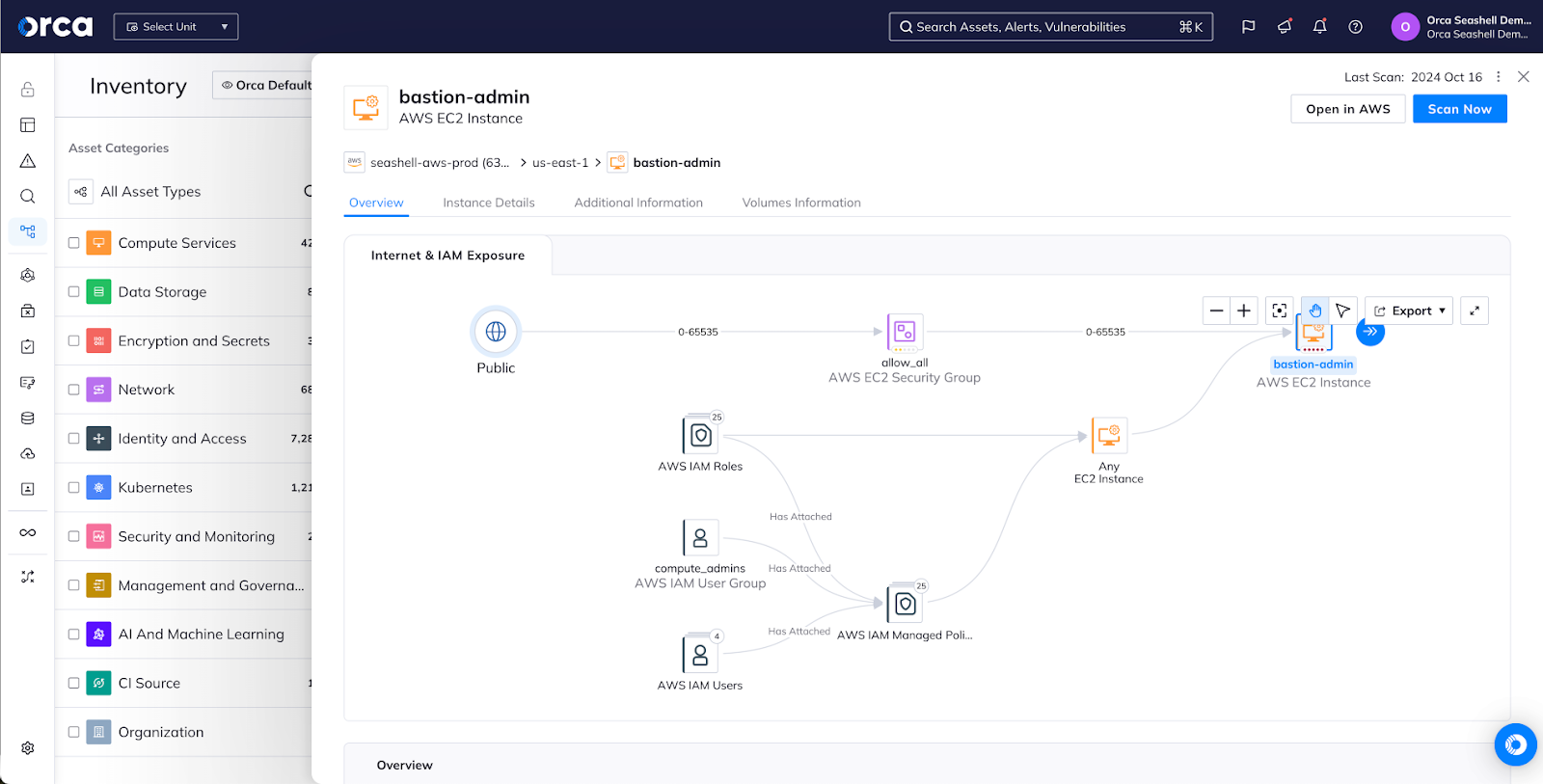
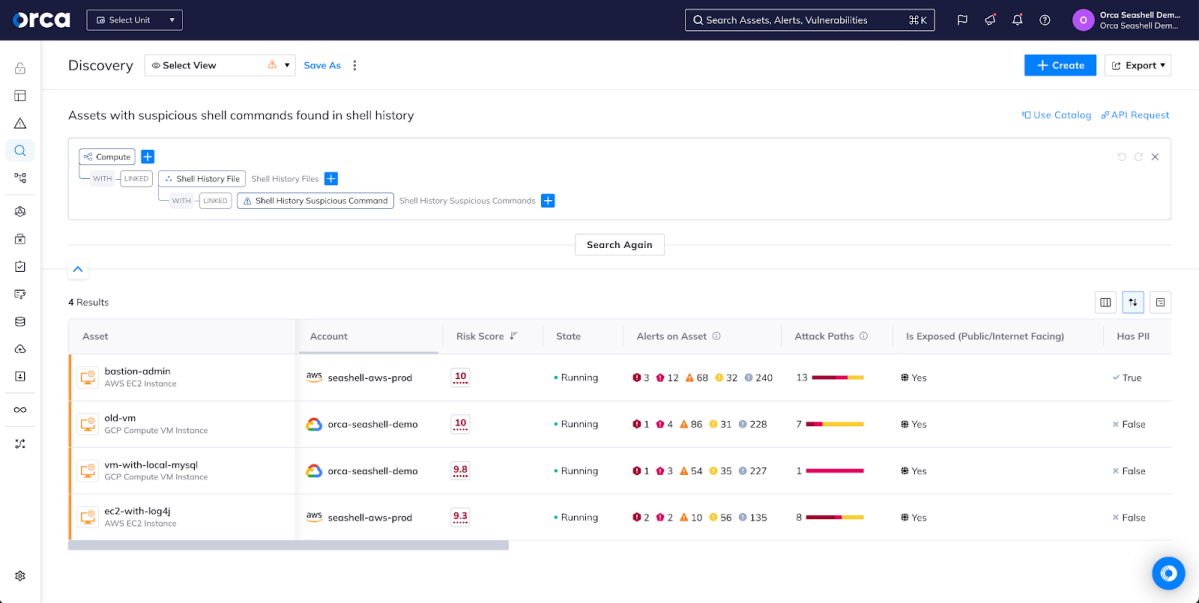
Orca’s agentless-first SideScanning technology quickly and easily scans all of your Linux and Windows workloads, including cloud VMs, containers and Kubernetes applications, and serverless functions. TotalCloud provides a partial agentless approach to vulnerability scanning but requires several agents to be deployed to get full functionality, complicating deployment and maintenance. Orca provides you with instant-on security and complete coverage for all your workloads and applications that TotalCloud can’t match. Within the Orca UI, you can view detailed risk prioritization information about all of your assets with context to understand your greatest risks and the impact to your business.
A unified data model
The Orca Platform brings all your data into a unified, easily queryable location. With Orca’s Unified Data Model, you can view assets, compliance status, risks, and security incidents from one dashboard.
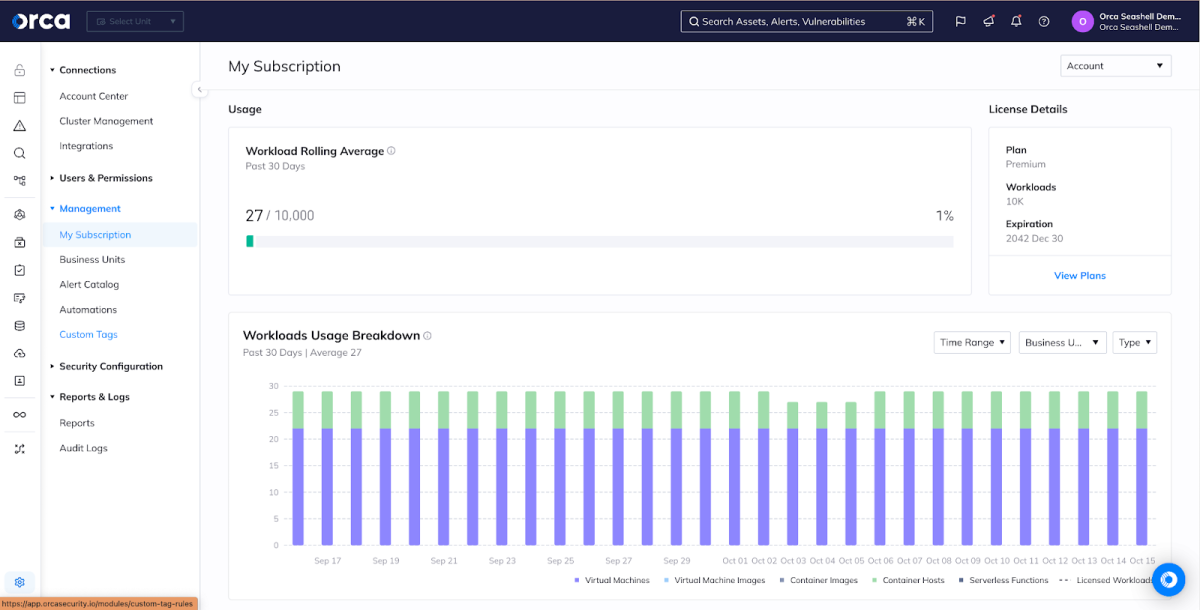
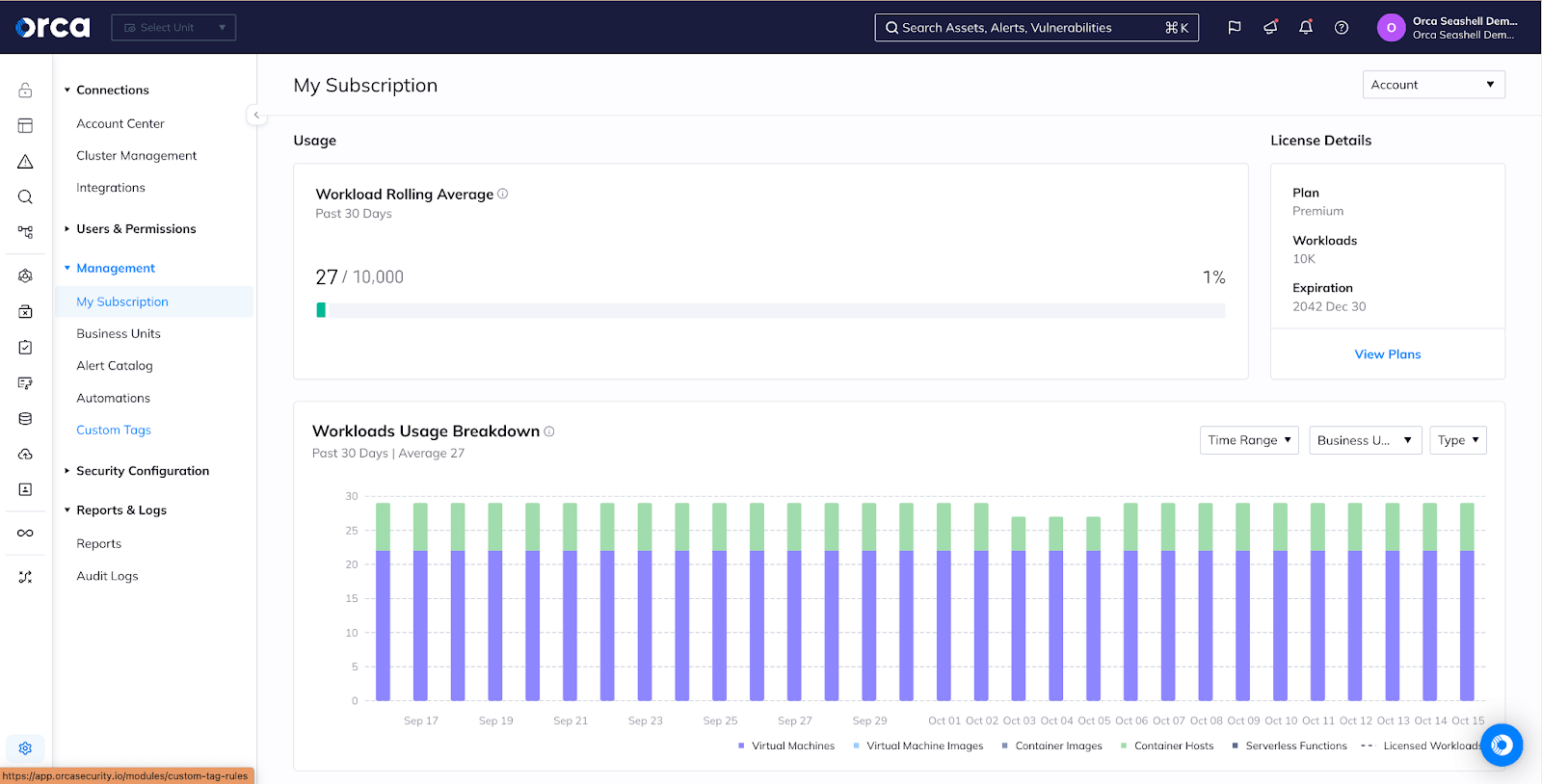
Simple, predictable pricing and best-in-class support
Orca takes a simple pricing approach that allows you to focus on securing your cloud environments and applications rather than worrying about a complicated mix of multiple different licenses. We’re also available when you need us to help you scale your business with confidence.

Personalized Demo
See Orca Security in Action
Gain visibility, achieve compliance, and prioritize risks with the Orca Cloud Security Platform.

Chat with Us
See Orca Security in Action
Gain visibility, achieve compliance, and prioritize risks with the Orca Cloud Security Platform.
No Slack account required.