Queries are a necessity to all great SaaS platforms. Since most software platforms either consume or produce large amounts of data, queries enable users of the platform the ability to search and sort data quickly. This allows the data that they ultimately consume or produce to have more value and meaning, allowing it to be viewed and understood.
The Orca Unified Data Model
With the Orca Cloud Security Platform, we want to make it easy and effective for cloud security engineers, compliance auditors, or DevOps engineers to gain visibility into and query their entire cloud environment.
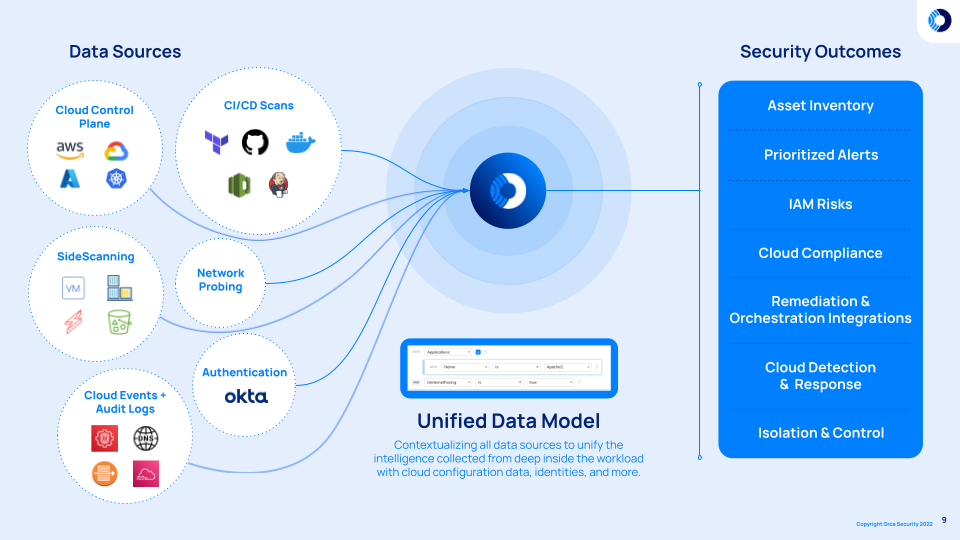
The Unified Data Model brings together all of the important information about your public cloud environment, including:
- The Cloud Control Plane
- SideScanning™ results for Linux and Windows workloads and application
- Flow and Audit log data
- CI/CD scans
- And more
With all of this vital information located in a centralized location–a differentiator compared to many competitive solutions that have been built by fragmented acquisitions–users have unlimited potential to query the data model.
Enabling the Data to Work for You
The Sonar advanced search query is very powerful, and for pros – can unlock anything from your data graph. While Sonar advanced search remains highly valuable within the platform today, Orca recognized the need to offer a more user-friendly option to query the data graph, that did not require a steep learning curve to produce the correct combination of SQL query strings that would deliver the right data and results that users desired.
With this in mind, we are announcing today an entirely new way to query your security data within the Orca Platform. The new Orca Discovery Query Builder applies a new approach for guiding users to their desired datasets without requiring a bachelor’s degree in creating custom SQL query strings.
The new graph-based query builder groups the unified data model into color coordinated and branded folder systems – with the categories and subcategories – to produce the correct combination of SQL query strings that would deliver the right data and results that users desired. Enabling easy visual navigation and use resulting in quicker filtration of the expansive cloud security data, making the data more valuable and consumable for those users who prefer to avoid writing their own custom SQL queries.
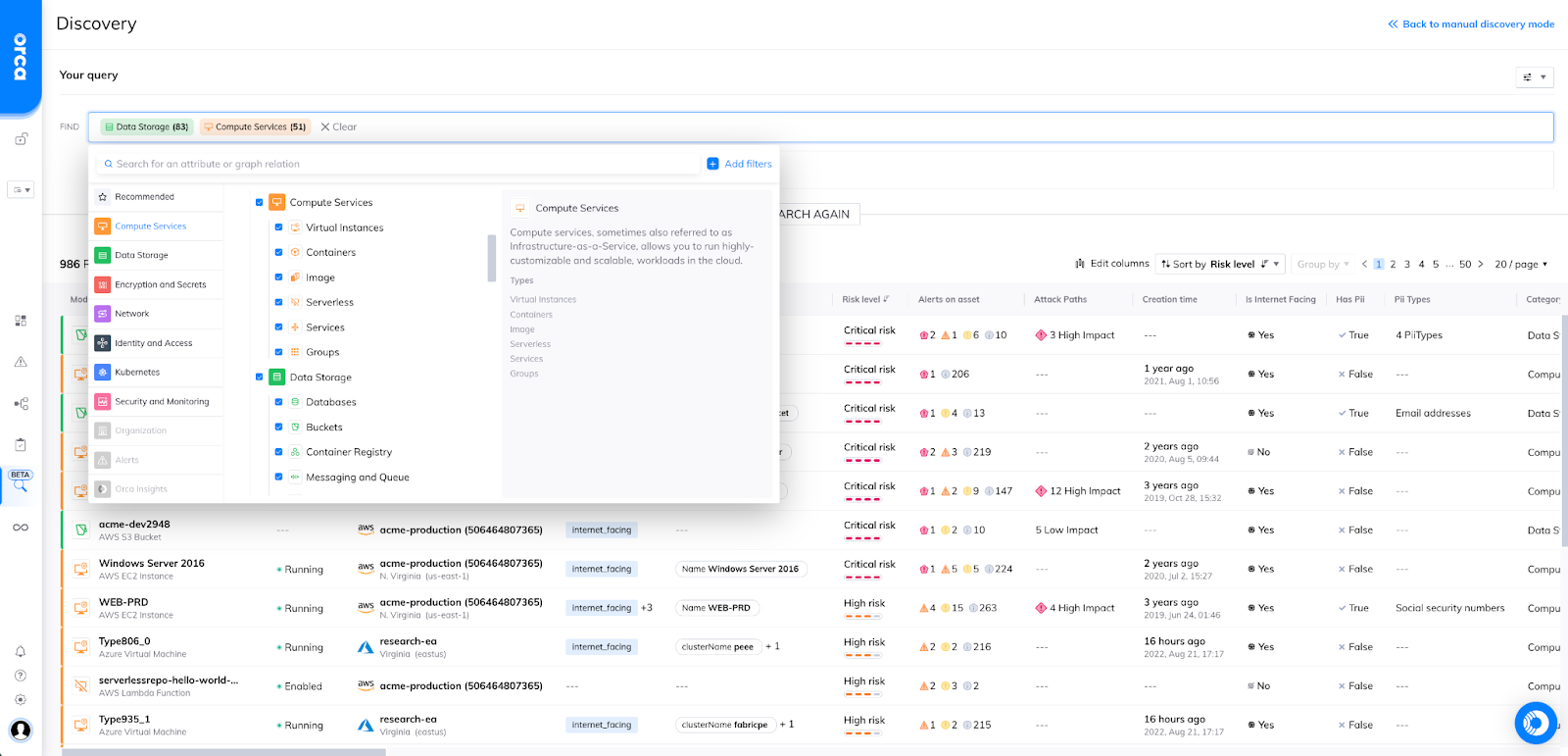
Orca Discovery – Query Builder UI
In one or two clicks, Orca users will be able to select assets, infrastructure, applications and more from our new query builder UI, which can then be further filtered down using an intelligent filtration component. The new discovery query builder no longer requires customers to know how to write lengthy custom SQL queries to locate the data pertinent to them. Now customers have the option to simply have custom queries built for them for faster and easier data filtration – delivering the value of your data to the user quicker and easier than before.
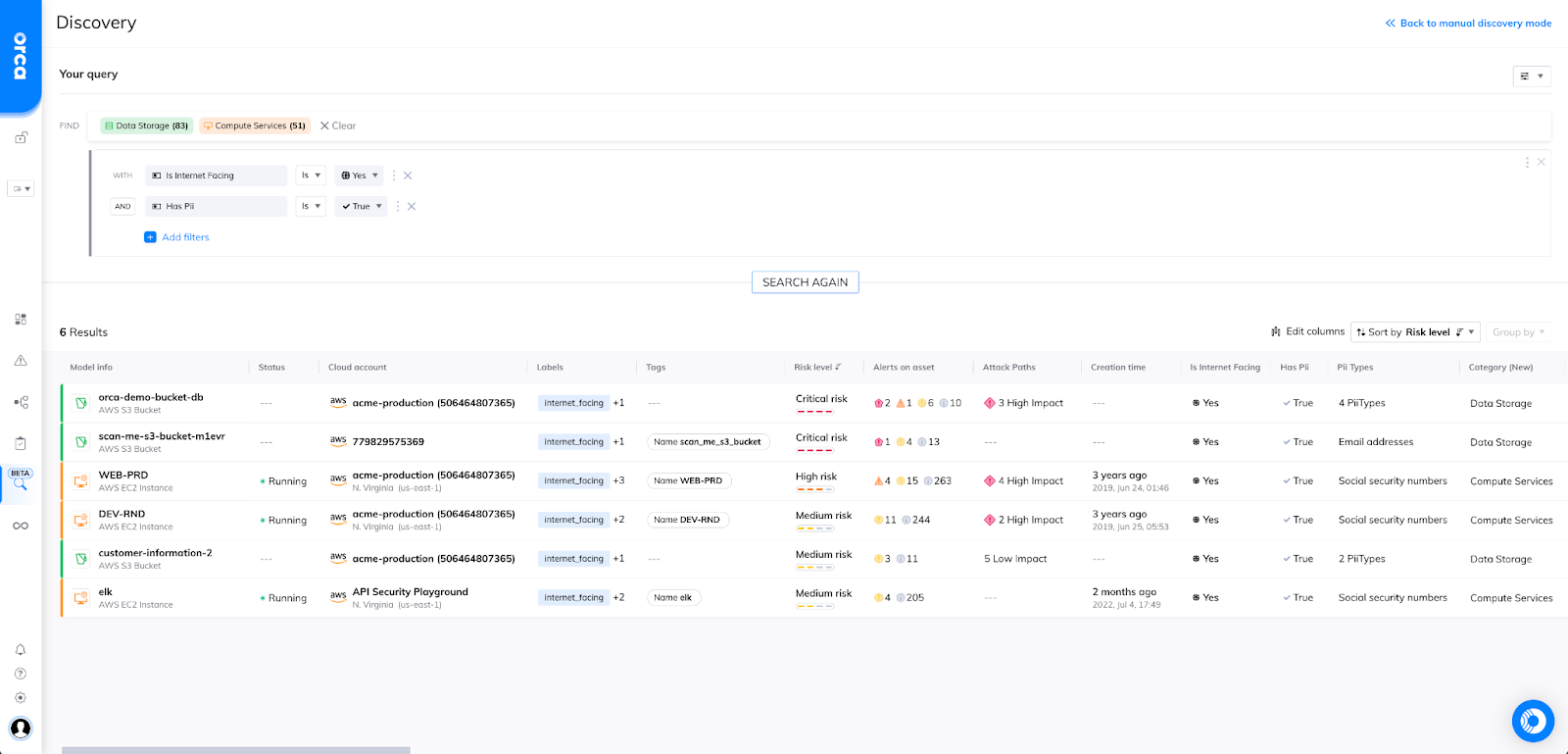
Orca query results with additional filters
Orca customers can casually discover and peruse (“window shop”) asset and inventory information across their entire cloud estate, or select options in a guided query builder for quicker and more accurate advanced searching (“find me X”). The new discovery query builder enables users to obtain the data they need, exactly when they need it.
Further improvements to come:
- Improved data modeling: for clearer filtering and graph-based query building. Quickly sort discovered alert types, asset information, inventory, user data and more.
- Reusable: Save views, create folders and share viewing and editing permissions to custom queries.
- Customizable: Edit columns and data sets that result from the query
- Consumable: Create shareable URLs or schedule exportable CSVs, JSON, etc.
Applying a Practical Use Case: Quickly Filtering the 1% of Data
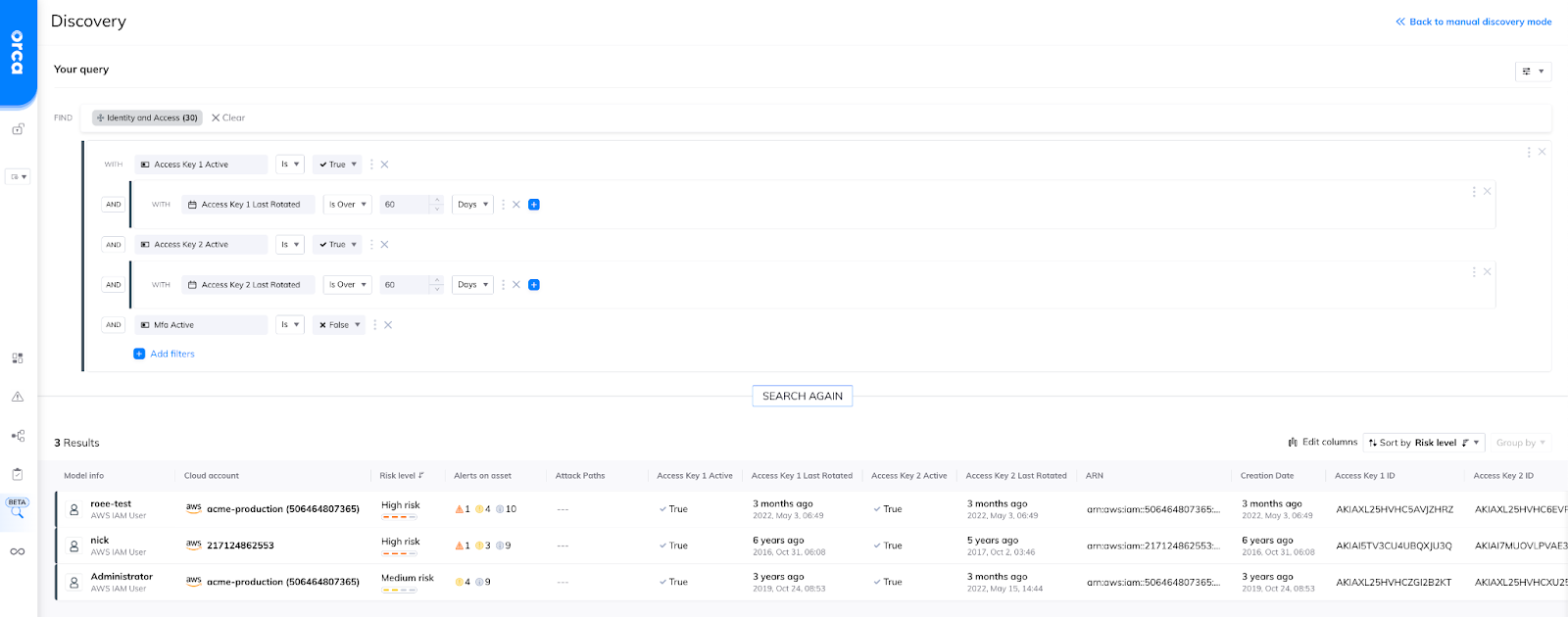
Similar to the example provided above regarding a simple query to find an S3 bucket that is housing PII or sensitive data, we can also quickly build queries that can discover our IAM hygiene.
Let’s say a security practitioner wants to discover all AWS users that do not have MFA enabled, and have not had their keys rotated in the last 60 days like best practices tells us they should. Traditionally in most data query tools, to find such a detailed combination of filters across a robust multi-cloud estate would have taken many varying attempts, and return unreliable results.
However, with Orca’s newly renovated discovery capability, user’s are able to find these results in minutes, and take investigative action directly from the data presented.
Another use case example would be to examine our virtual instances and reference those who does not have their SSH keys already encrypted. Furthermore, we can examine if any of these instances is running an outdated version of their operating system.
To get even more granular, we could further our search by showing instances that already have malware alerts associated with them, or still has Log4j installed. In the example, we have taken – in some cases – several hundreds or even thousands of VMs and quickly narrowed them down to two primary virtual instances that might pose the greatest risk to our cloud environment.
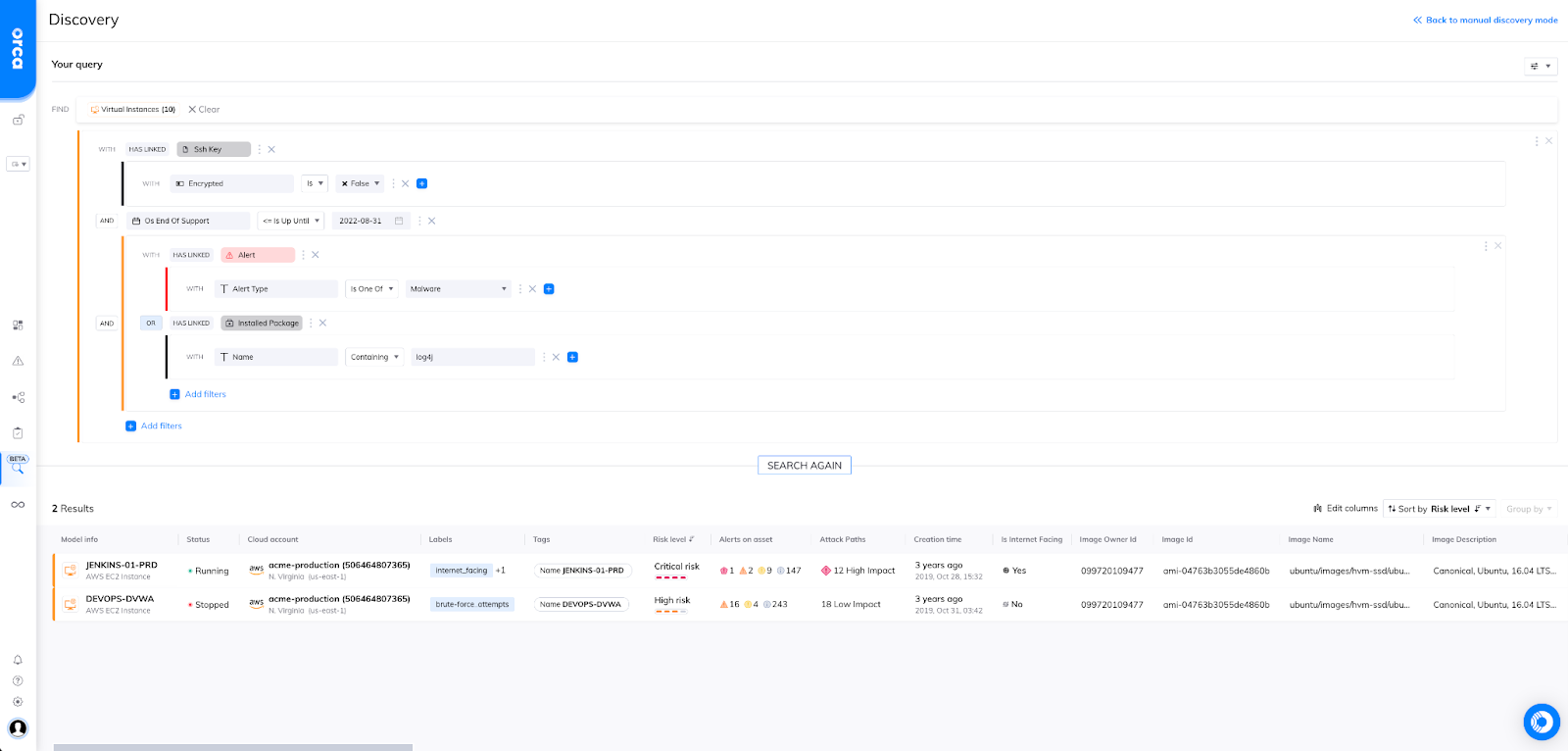
Within just a few minutes, customers of Orca have been able to locate any instances that have already seen evidence of compromise (malware) or any instances that could potentially still be vulnerable to attacks by having Log4j.
This becomes a VERY powerful tool once queries are built and saved so users are able to quickly dive very specifically into what they want to see, when they want to see it.
To see more, watch this video:
Give It a Try Today!
If you are an Orca customer, locate the discovery icon on the left navigation bar and begin building and saving some of your most valuable and frequent queries. Export results in a variety of formats and share them with team members.
If you are not an Orca customer today, give us a try! Schedule your 30-day free trial and experience the centralized management of your entire cloud estate and the security simplicity only found in the Orca Security Platform.