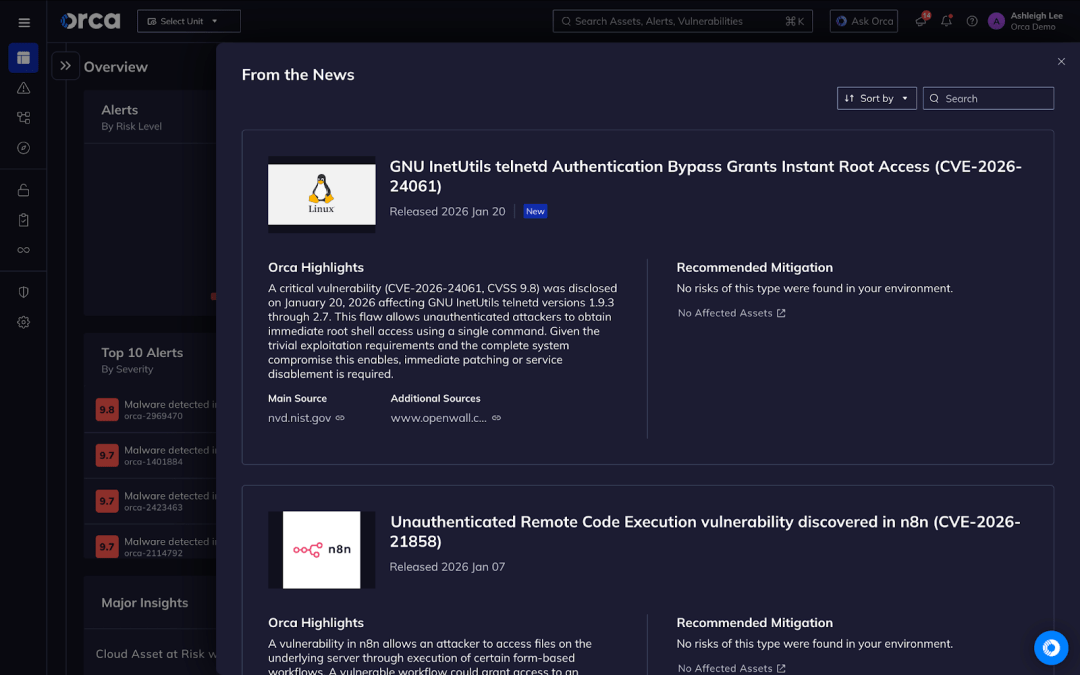
A critical vulnerability (CVE-2026-24061, CVSS 9.8) was disclosed on January 20, 2026 affecting GNU InetUtils telnetd versions 1.9.3 through 2.7. This flaw allows unauthenticated attackers to obtain immediate root shell access using a single command. Given the trivial exploitation requirements and the complete system compromise this enables, immediate patching or service disablement is required.
Vulnerability Summary
CVE ID: CVE-2026-24061
CVSS Score: 9.8 (Critical)
CWE Classification: CWE-88 (Argument Injection)
Affected Product: GNU InetUtils telnetd
Affected Versions: 1.9.3 through 2.7
Attack Vector: Network (TCP port 23)
Authentication Required: None
Exploitation Complexity: Low
Active Exploitation: Yes
Technical Analysis
The vulnerability resides in the telnetd/utility.c file within the _var_short_name() function. The root cause is insufficient validation of the USER environment variable before it is passed to /usr/bin/login.
During connection establishment, telnetd supports the NEW_ENVIRON telnet option as defined in RFC 1572. This feature permits clients to transmit environment variables during session negotiation. The login binary accepts a -f flag which instructs it to bypass password verification for users presumed to be pre-authenticated.
The flaw exists because telnetd fails to validate whether the USER variable begins with a dash character. An attacker can supply USER=-f root and connect using telnet with the -a or --login flag. This results in telnetd invoking login -f root, which bypasses all authentication checks and immediately grants a root shell.
The attack requires no credentials, no prior system access, and no user interaction.
Affected Components
GNU InetUtils telnetd versions 1.9.3 through 2.7 are vulnerable. The flawed code was introduced in a March 2015 commit and went undetected for nearly 11 years.
According to Shodan, approximately 221,000 devices expose telnet services on port 23 to the internet. Not all of these run GNU InetUtils telnetd, but organizations should verify their exposure.
Known affected distributions include Debian, Ubuntu, Kali Linux, Trisquel, and SUSE.
Red Hat Product Security has confirmed that this vulnerability does not affect any currently supported Red Hat product.
Note: Ubuntu security patches for this vulnerability are still pending at the time of writing. Ubuntu users should monitor for updates or remove telnetd entirely.
Remediation
| Distribution | Vulnerable Versions | Fixed Version | Action |
|---|---|---|---|
| GNU InetUtils | 1.9.3 – 2.7 | 2.8+ | Upgrade |
| Debian bullseye | < 2:2.0-1+deb11u3 | 2:2.0-1+deb11u3 | Apply DSA-6106-1 |
| Debian bookworm | < 2:2.4-2+deb12u2 | 2:2.4-2+deb12u2 | Apply DSA-6106-1 |
| Debian trixie | < 2:2.6-3+deb13u1 | 2:2.6-3+deb13u1 | Apply DSA-6106-1 |
| Ubuntu | All versions | Pending | Monitor for updates or remove telnetd |
| SUSE | Through 2.7 | Available | Apply security update |
The upstream fix is contained in commits fd702c02 and ccba9f74. The patch introduces validation that rejects USER values beginning with a dash character.
Immediate Actions
- Disable telnetd service:
sudo systemctl stop telnetd && sudo systemctl disable telnetd- Block port 23:
sudo iptables -A INPUT -p tcp --dport 23 -j DROP- Apply patches or upgrade to 2.8+
- Remove telnetd entirely:
sudo apt remove inetutils-telnetd- Replace with SSH for remote access
Exploitation Status
Multiple public proof-of-concept exploits are available on GitHub from independent security researchers.
According to GreyNoise, active exploitation has been observed in the wild. Their telemetry shows approximately 18-21 unique IP addresses conducting automated exploitation scans within 24 hours of disclosure. Attack traffic originated from Hong Kong, the United States, Japan, the Netherlands, China, Germany, Singapore, and Thailand.
GreyNoise reporting indicates that 83% of observed exploitation attempts targeted root access specifically. A combination of automated scanning tools and manual operator activity has been observed, suggesting this vulnerability is being incorporated into broader attack operations.
Impact
Successful exploitation results in immediate root-level access to the target system. This allows attackers to steal credentials (including contents of /etc/shadow), install persistent backdoors, move laterally to other systems on the network, and execute arbitrary commands.
The fact that this vulnerability existed undetected for 11 years raises concerns that organizations may wish to consider when determining whether forensic analysis of affected systems is warranted.
Official Advisories
Government cybersecurity agencies have published advisories regarding this vulnerability:
- Canadian Centre for Cyber Security: AL26-002, AV26-047
- Belgian CCB: Critical warning
- Dutch NCSC: Security advisory
- Spain INCIBE: Active exploitation warning
Simon Josefsson, the GNU InetUtils maintainer, has stated that users should avoid running telnetd entirely and should restrict network access to the telnet port to trusted clients only.
Detection and Hunting Guidance
Organizations can detect exploitation attempts using the following methods:
- At the network level, monitor telnet connections on TCP port 23 for NEW_ENVIRON option negotiation containing USER values that begin with -f.
- At the host level, examine authentication logs for root login events via telnetd that lack corresponding password authentication prompts.
Review /var/log/auth.log or /var/log/secure for telnetd entries containing patterns matching USER.*-f.
Additionally, audit for unexpected root shell processes spawned by the telnetd daemon.
How can Orca help?
The Orca Cloud Security Platform enables security teams to respond to threats like CVE-2026-24061 within minutes.
- Instant Discovery: Identify all assets running vulnerable inetutils-telnetd packages across AWS, Azure, and GCP – without deploying agents
- Context-Aware Prioritization: See which vulnerable assets are internet-facing, in production, or contain sensitive data – focus on what matters first
- Attack Path Analysis: Understand if this vulnerability creates a path to critical assets or can be chained with other risks
- Real-Time Alerts: Get notified immediately when new critical vulnerabilities are detected in your environment
With Orca, customers affected by CVE-2026-24061 were able to identify their exposure and begin remediation the same day – turning a critical threat into a closed ticket.