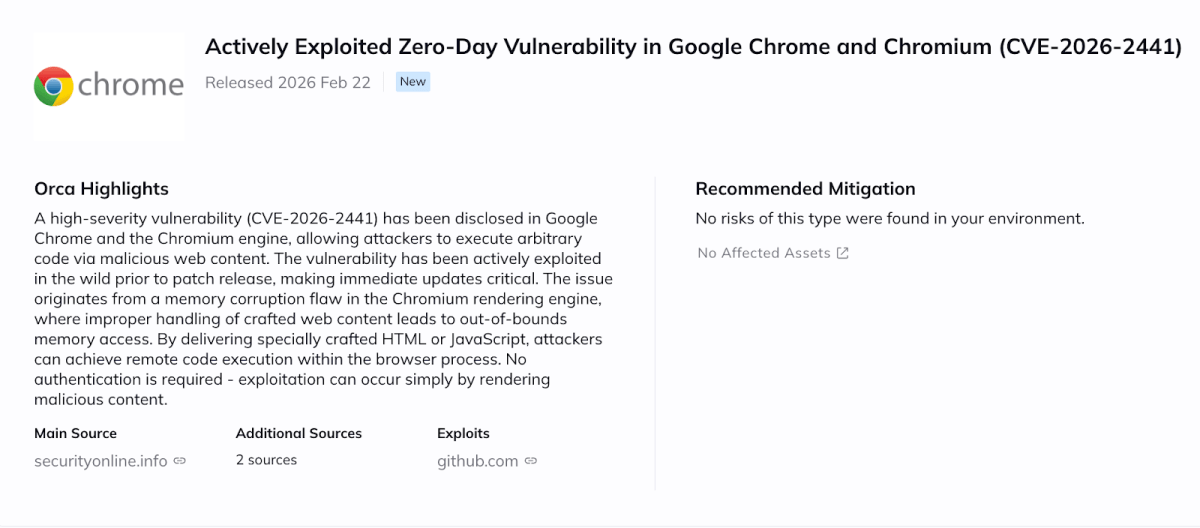
A high-severity vulnerability (CVE-2026-2441, CVSS pending vendor confirmation) has been disclosed in Google Chrome and the Chromium engine, allowing attackers to execute arbitrary code via malicious web content. The vulnerability has been actively exploited in the wild prior to patch release, making immediate updates critical.
Technical Details
The issue originates from a memory corruption flaw in the Chromium rendering engine, where improper handling of crafted web content leads to out-of-bounds memory access. By delivering specially crafted HTML or JavaScript, attackers can achieve remote code execution within the browser process. No authentication is required, and exploitation can occur simply by rendering malicious content.
Why This Matters
While traditionally viewed as an endpoint issue, this vulnerability is particularly relevant to cloud environments due to the widespread use of Chromium in non-interactive contexts, including:
- Headless Chrome used for PDF generation or web previews
- CI/CD pipelines running automated browser tests
- Web scraping services
- Puppeteer/Selenium-based automation
- Containers rendering user-submitted URLs
- Developer jump hosts and bastion servers
Any workload that programmatically renders untrusted or external content may be exposed.
Affected Components and Versions
The following components are affected: Google Chrome and Chromium-based browsers, including Microsoft Edge, Brave, Opera, and embedded Chromium runtimes. Affected versions include builds prior to Google’s patched release issued this week. Organizations running older versions in cloud images, containers, or automation pipelines should verify their environments immediately.
Mitigation and Patching Guidance
Users should upgrade to the latest stable Chrome/Chromium release, which addresses the vulnerability. Even non-interactive or headless deployments must be updated, as rendering malicious content is sufficient to trigger exploitation.
Risk and Impact
At the time of writing, public exploit details are available and active exploitation has been confirmed. Given Chromium’s prevalence in cloud workloads and automation frameworks, the risk extends beyond traditional user browsing scenarios.
Successful exploitation could allow attackers to execute code on affected systems, steal authentication tokens, access CI secrets, pivot into internal infrastructure, or deploy secondary malware. In automation-heavy environments, a compromised rendering service or CI runner could provide a direct path to sensitive credentials or production systems.
How can Orca help?
Orca enables customers to quickly identify assets running vulnerable Chromium or Chrome versions, including headless deployments inside containers and CI/CD workloads. Orca provides context on internet exposure, runtime reachability, and asset criticality, helping teams prioritize remediation based on real risk rather than CVSS alone. Affected assets are highlighted directly in the newItem view to streamline response and patch validation.