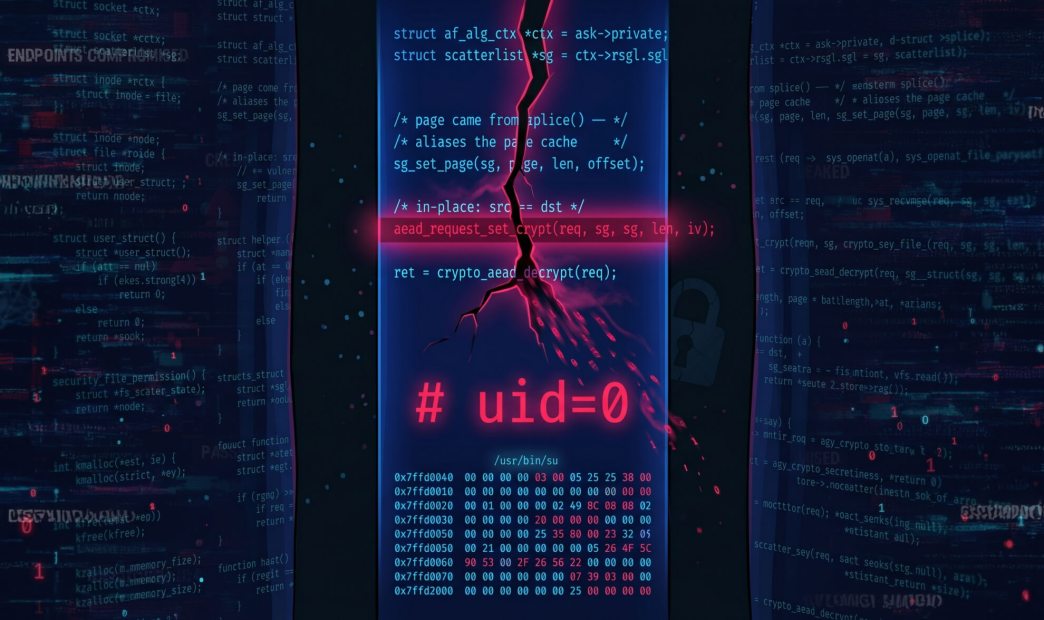
A Linux kernel vulnerability, CVE-2026-31431 dubbed Copy Fail, allows an unprivileged local user to gain root by corrupting the page cache of readable files such as /usr/bin/su. The disk file is not modified, so normal file-integrity checks may not detect exploitation.
Affected systems include Linux distributions shipping vulnerable kernels with the AF_ALG AEAD in-place path. The researchers tested exploitation on Ubuntu 24.04 LTS, Amazon Linux 2023, RHEL 14.3, and SUSE 16, across kernel lines 6.12–6.18. Containers and other Linux distributions may also be impacted because page cache is shared.
Users should update to a patched kernel version. Temporary mitigations include blocking AF_ALG AEAD usage, such as blacklisting algif_aead or restricting AF_ALG sockets with seccomp.
About the Vulnerability: CVE-2026-31431
The issue originates from the interaction between three Linux kernel features: AF_ALG, which exposes kernel cryptographic algorithms to userspace; splice(), which can pass page-cache-backed file pages by reference without copying; and the authencesn AEAD crypto template. In the vulnerable path, AF_ALG AEAD decryption operated “in place,” causing page-cache pages supplied through splice() to become part of a writable destination scatterlist.
How can Orca help?
Orca enables customers to quickly identify assets running vulnerable Linux systems, understand their exposure in context including internet accessibility, runtime reachability, and asset criticality, and prioritize remediation based on real risk rather than CVSS alone. Orca’s platform highlights affected assets directly in the alert view, helping security teams focus on the most critical remediation paths first.