Table of contents
In the ever-evolving landscape of cloud security, security teams are constantly battling a deluge of alerts and operational friction. This often leads to a dispersed effort, with teams reacting to individual findings rather than collaborating on root causes and driving meaningful risk reduction. Consequently, this dispersed effort yields outcomes that are often unmeasurable, stalling progress toward meaningful risk reduction.
The Problem: Alert Fatigue and Disconnected Efforts
Today’s security teams face an uphill battle. The sheer volume of security alerts from various tools can be overwhelming, making it difficult to prioritize, understand the true impact, and effectively remediate risks. This “findings overload” often results in:
- Dispersed and Reactive Effort: Teams jumping from one alert to another without a cohesive strategy or ‘Done’ state
- Organizational Friction: Lack of clear ownership and collaboration on remediation.
- Contextless Risk Reduction: Difficulty in demonstrating tangible improvements in the security posture.
The Solution: Organized, Outcome-Driven Security with Orca Missions
Orca Security is proud to announce Orca Missions. Orca Missions are a transformative approach designed to shift security triage from a reactive, finding-by-finding task into an organized outcome-driven workflow.
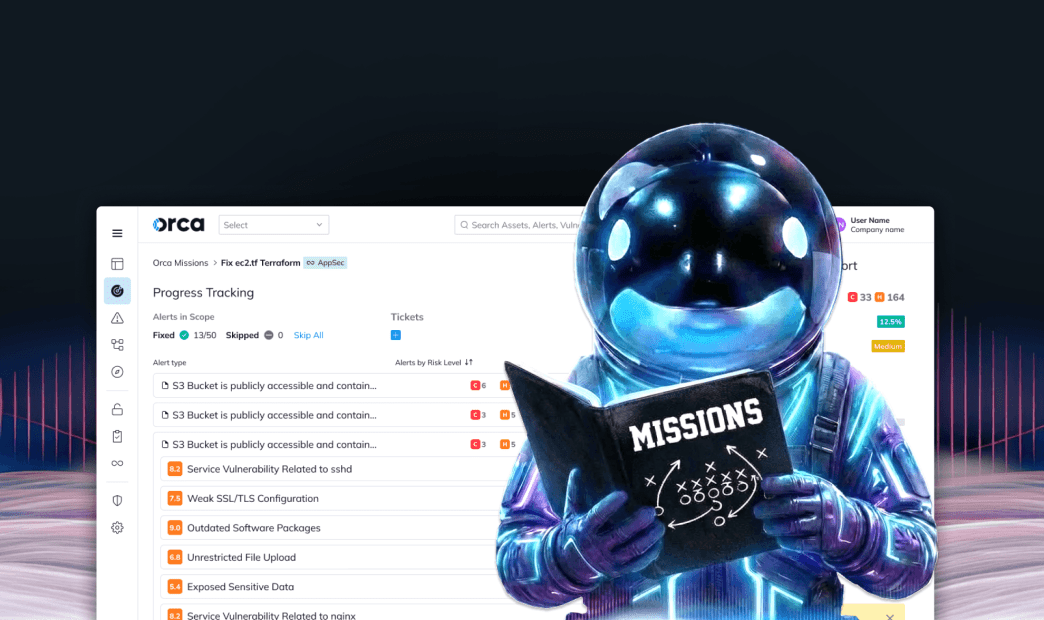
Each mission represents a specific, actionable, and achievable initiative that groups related findings into one clear, focused objective by providing unparalleled measurability from initial identification through remediation. Mission success empowers you to monitor security effectiveness with precision, guaranteeing your goals are met and validated at every step.
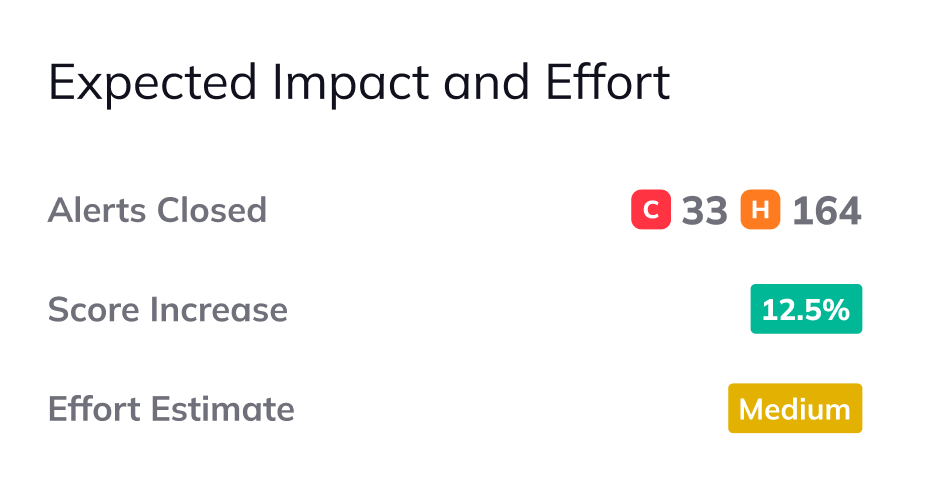
Orca Missions lead with predictable ROI: before a mission is even initiated, the mission hub clearly shows you the recommended actions, alerts that will be resolved, the estimated effort, and the expected Score Increase to your security posture. This crucial context allows you to calculate the exact return on investment for your team’s time.
How Orca Missions Work–A Closer Look
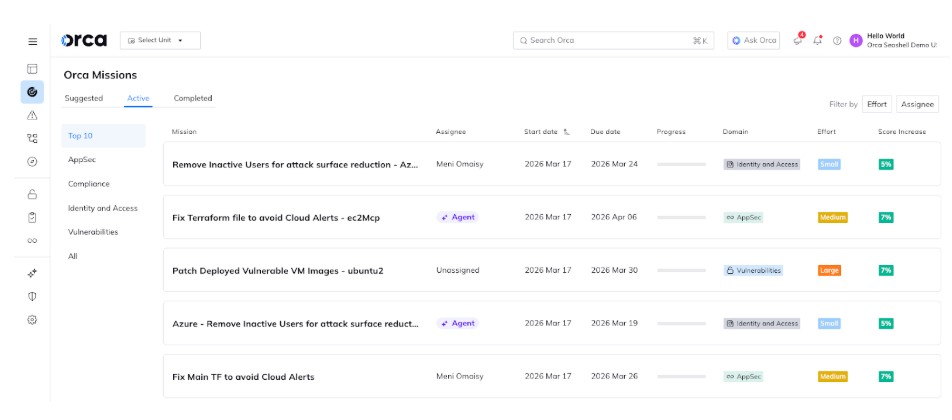
At its core, each mission is built from a Template, a high-level strategic blueprint. This blueprint contextually groups related items, such as alerts and vulnerabilities, based on factors like risk severity and remediation effort. This specialized logic is crucial as it cuts through the noise, ensuring your team’s efforts are concentrated on the most impactful opportunity areas.
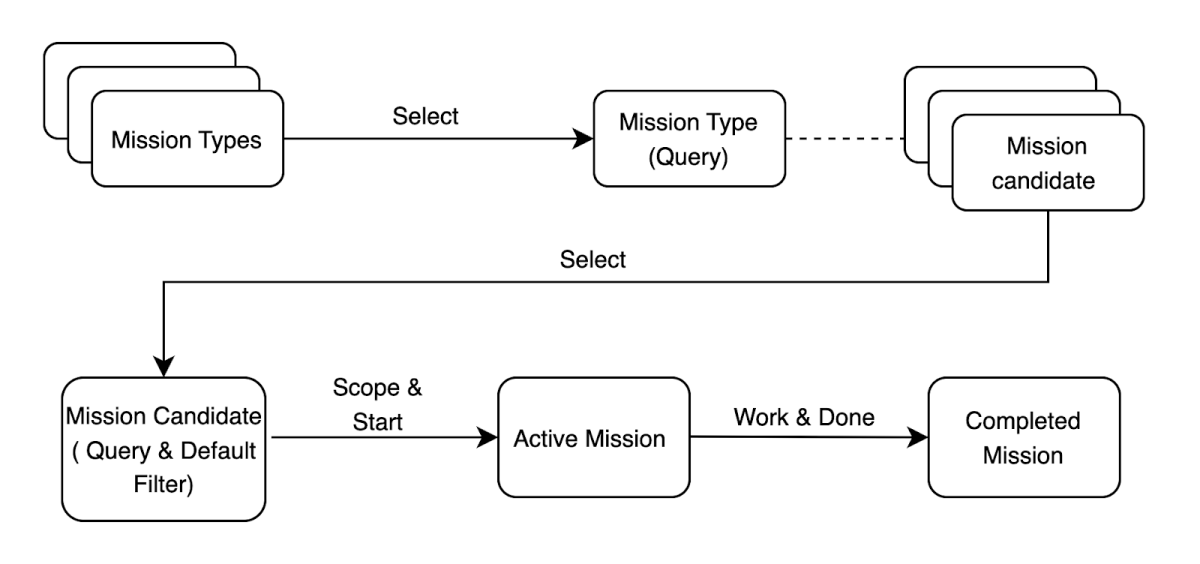
With this Template, you get a powerful birds-eye view of a single risk vector across your entire resource, ensuring you have the full context to treat the systemic risk rather than singular, reactive alerts.
Missions were designed from the ground up to be a reportable and efficient orchestration of your workflow, giving you back hours spent on manual alert triage. The journey begins with an initial query that populates a foundational alert scope. Security analysts can refine this scope, gaining granular control over underlying remediation items to ensure the mission aligns with your organization’s security strategy.
Mission progress is tracked from a centralized hub. From here, you get the full context on misconfigurations, impacted assets, and outstanding actions, allowing analysts to initiate and assign the appropriate tickets for remediation. This centralized, context-rich coordination ensures the sizing and delegation is validated upfront, rather than post-hoc.
Orca Missions are focused on a single, verifiable goal: the Definition of Done (DoD). This clear objective signals mission completion (e.g., all outstanding assets are resolved or skipped), transforming your remediation strategy into a “Mission Accomplished” rather than just “Alerts Cleared.” The result is a reportable source of truth for measuring your team’s impact, enabling the precise evaluation of effort and progress towards achieving your security goals.
Orchestrate Your Remediation Workflow
To illustrate Orca Missions in action, let’s jump in and review a few real-world scenarios to see how missions can organize and accelerate your remediation workflows.
1. Fix Terraform File to Avoid Cloud Alerts
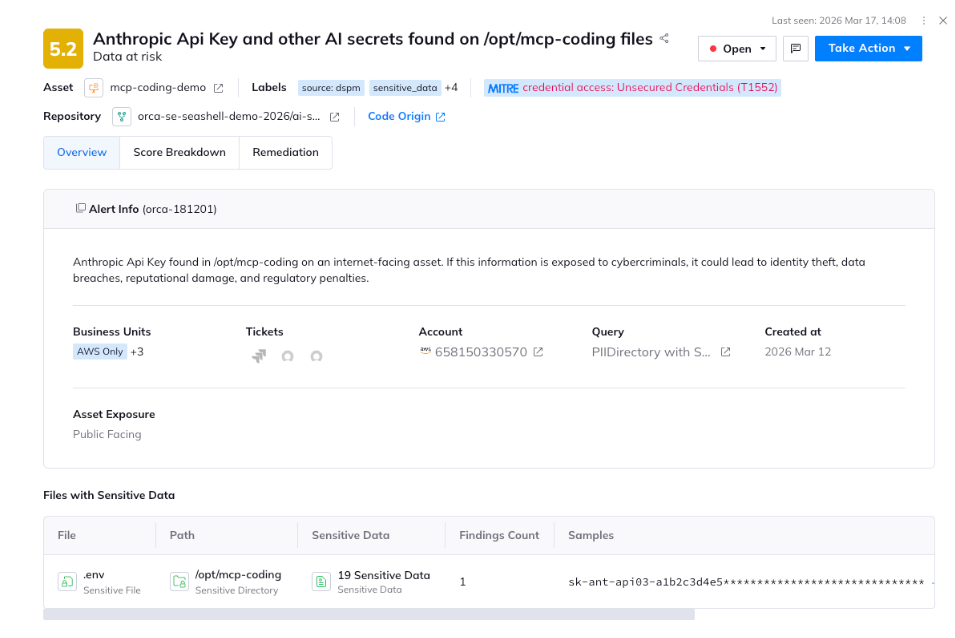
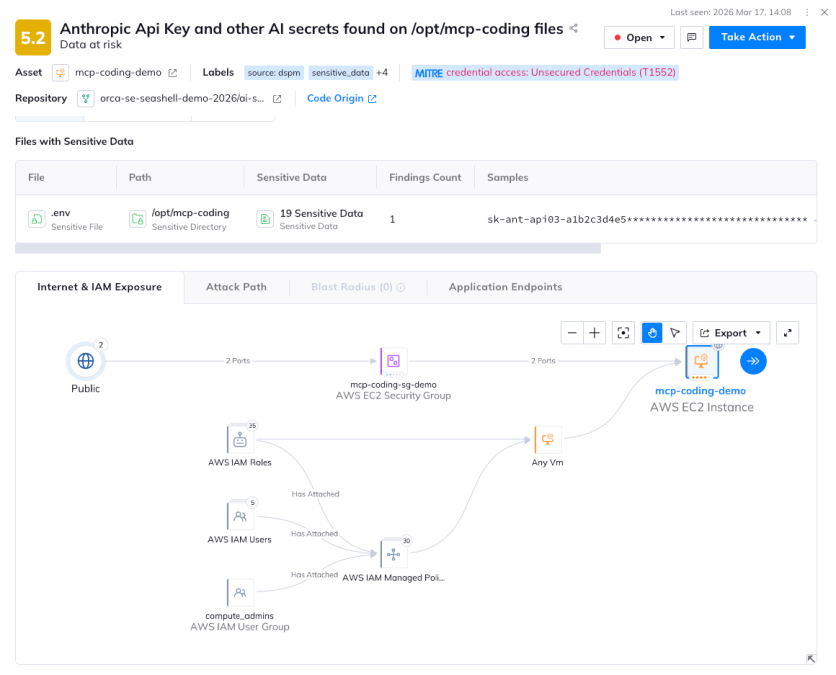
Imagine you are a security analyst and you have just received a critical alert: an Anthropic API Key and 18 other AI-related secrets have been found in a plain-text .env file on an internet-facing EC2 instance. You have to open a high-priority ticket, but then the “handoff shuffle” starts. You need to coordinate with the DevOps team to find the resource owner and the AI team to rotate the keys—all while trying to identify exactly which Terraform module originally deployed this insecure configuration.
This workflow exists as just one of many daily fires fighting for your team’s attention in a dashboard or creating noise in a Slack channel. Valuable analyst time that should be spent on critical issues is reappropriated to administration, negotiation, and discovery. While this may seem like routine vulnerability management, consider the following:
- The alert flagged the API keys, but do you have the time or mechanisms to investigate all relevant risk vectors?
- Is this a one off alert or does this represent a larger systemic issue in your IaC?
- Are you just “plugging a leak” on one file, or are you leading a campaign that actually hardens the organization’s entire AI infrastructure?
- Are you able to prove the organization is actually safer after fixing 1, 10, or even 100 similar alerts?
This is where Orca Missions can help. When you use the Orca Mission, all vulnerabilities tied to the resource are identified and logically aggregated. This frictionless orchestration moves your team beyond investigating one-dimensional alerts to addressing the entire hierarchy of risk implications across the resource.
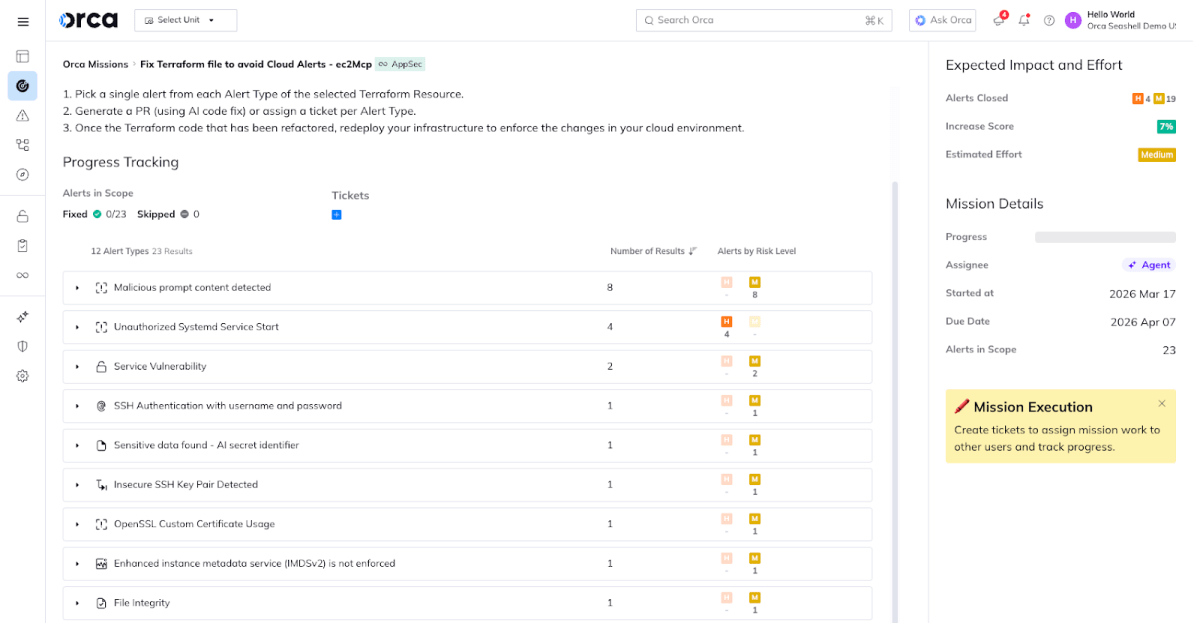
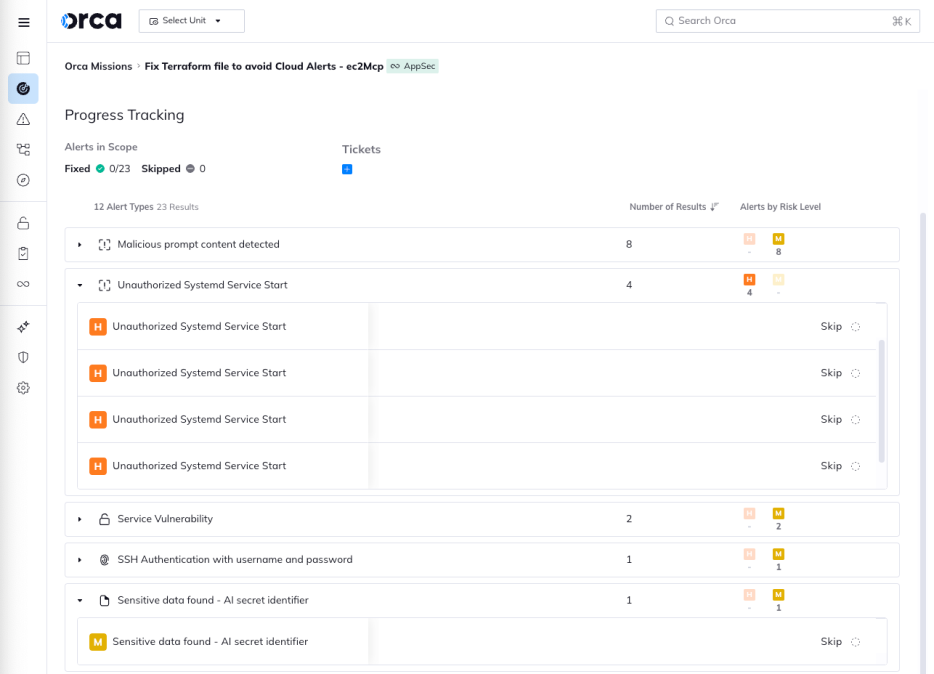
Instead of just seeing a notification for an exposed secret, analysts gain immediate visibility into the technical layers that weave a single alert into a heuristic threat investigation. In this mission, Orca looks at the broader exposure context, grouping 12 distinct alert types, allowing teams to investigate and assign owners across the full breadth of risk in a single dashboard.
Rather than directing a single engineer to spend hours hunting for the specific module responsible for each of the 23 unique alerts types, you can easily delegate alerts by group or by mission tasks to your team with a clear path to resolution.
2. Remove Inactive Users for Attack Surface Reduction
Let’s say your identity management system flagged an alert for an inactive user. After plugging the hole you realize it’s probably safest to go through and verify all inactive accounts. But as a multi-cloud organization, manually identifying and de-provisioning inactive users across multiple cloud accounts (AWS, Azure, GCP, etc.) is often a tedious, repetitive, and neglected task. Each account needs to be checked, usage logs analyzed creating a high level of operational friction at the expense of risk. This is especially prevalent if you don’t have a process or automation in place to enforce user lifecycle governance evenly across your organization. There are a few glaring questions that arise when you are tasked with user account review and de-provisioning.
- How often are you manually auditing every single account across your entire cloud estate for inactivity?
- Are you sure you’ve caught every user across every platform, or are unused accounts creating silent security blind spots?
- Do you know the privileges of each inactive user, and is your team prioritizing the highest-risk accounts for removal?
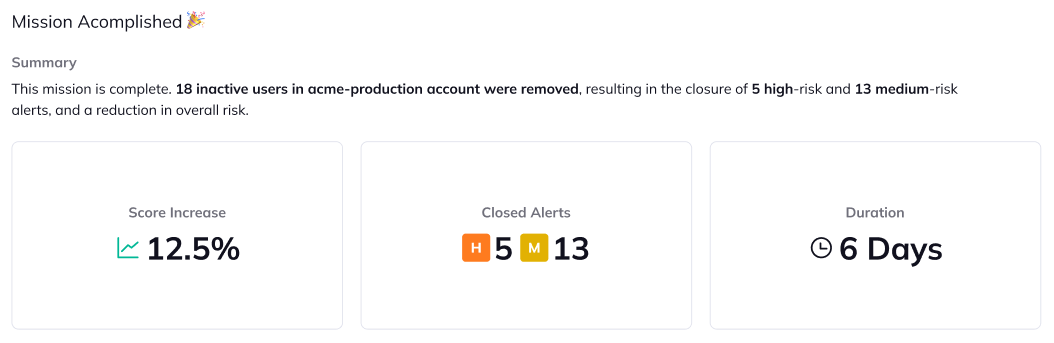
With Orca Missions, all users not active in the last 90 days are aggregated in a powerful, orchestrated sweep of your entire multi-cloud estate. It aggregates these identity risks into a single tracker, allowing you to see the collective risk these “ghost” users pose to your organization.
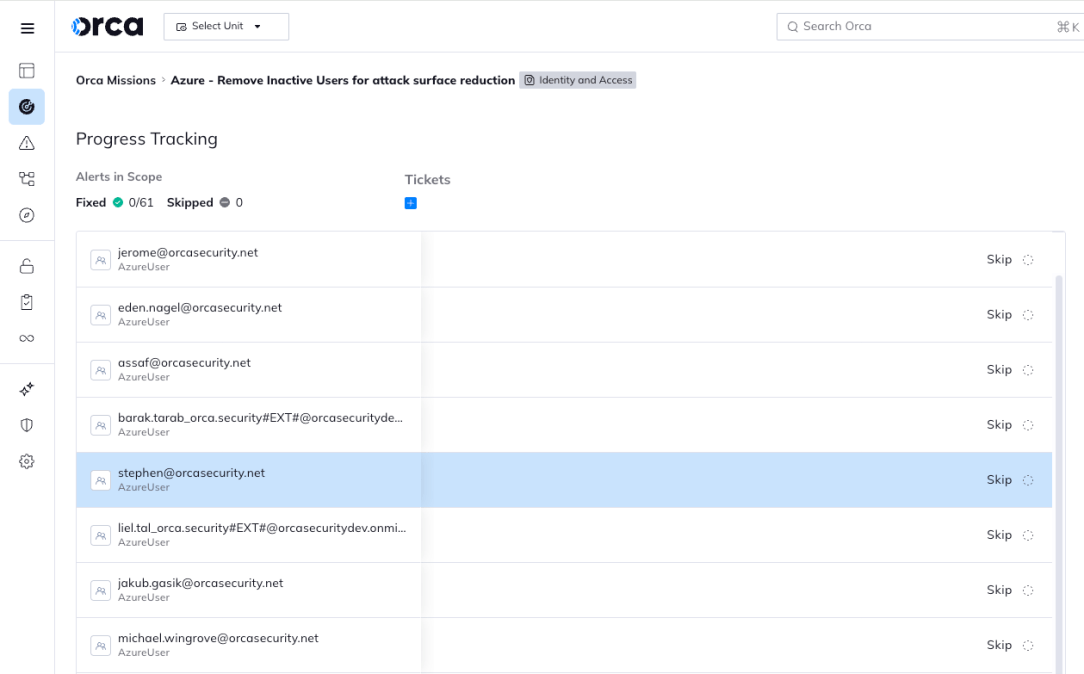
By centralizing the remediation, skips past questioning individual accounts and focuses on executing a bulk cleanup. Whether you choose to delete the users or rotate credentials to bring them back to “Active” status, the mission tracks the effort from start to finish. This creates a clear audit trail that shows exactly how much you’ve shrunk your organization’s attack surface in one coordinated effort.
3. Gain Compliance Score Lift for a Framework
You’re a Compliance Officer looking at a looming audit. Your dashboard shows you are at 82% compliance for SOC2 or NIST, but getting to 90% feels like an insurmountable climb. Under the traditional model, you’d have to dive into dozens of different control categories, each with its own set of disparate alerts. You might spend hours fixing a complex networking issue only to see your total score move by a fraction of a percent.
This “bottom-up” approach to compliance is exhausting and inefficient. Without a clear view of which actions yield the highest ROI, teams often:
- Fix high-effort, low-impact issues while easy “wins” remain buried.
- Lose track of which specific alerts are preventing a control from passing.
- Struggle to communicate progress to stakeholders because the “score” feels disconnected from daily tasks.
For GRC teams, Orca Missions provides a top-down strategy with tailored remediation actions across any of Orca’s 200+ included compliance frameworks. The Compliance Score Lift Mission identifies the “low-hanging fruit”—controls that are failing due to only one or two associated alerts. By focusing your energy here, you achieve the maximum possible score increase with the least amount of engineering effort.
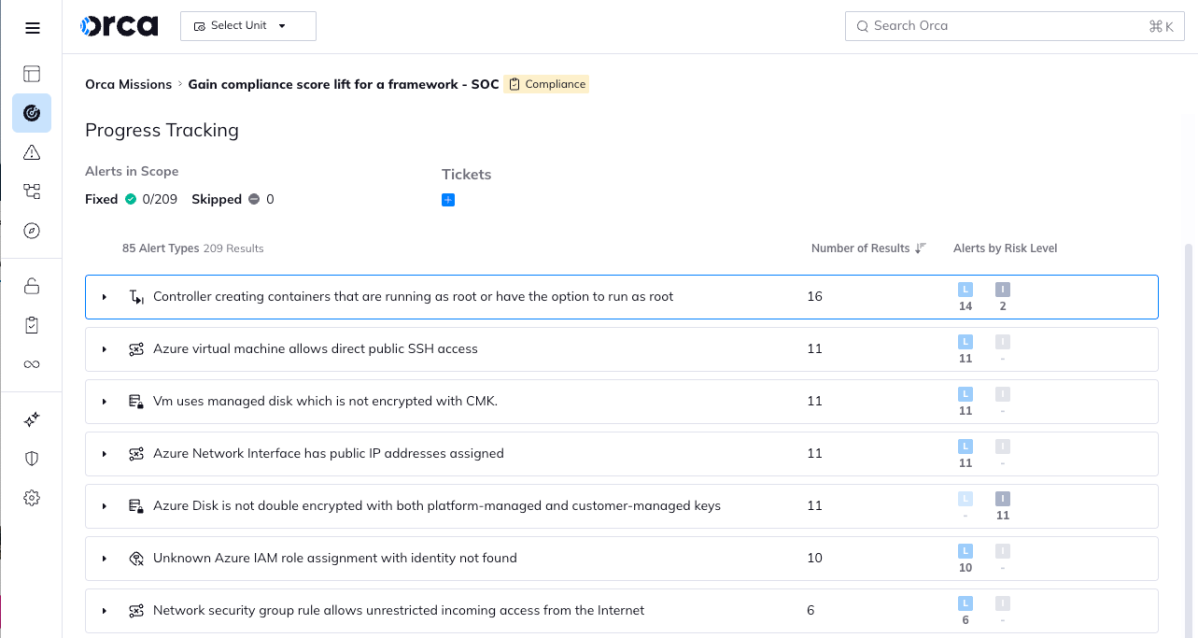
The mission guides you through the remediation of these specific blockers, offering direct suggestions to resolve or dismiss alerts. Instead of guessing which task will satisfy an auditor, you are given a clear path to “Done.” This turns compliance from a static checklist into a dynamic, achievable goal, allowing you to report a significantly improved security posture to leadership in a fraction of the time.
4. Patch Deployed Vulnerable VM Images
As a Cloud Engineer, you’re drowning in vulnerability reports. Your scanner shows hundreds of instances of a high-risk vulnerability across your fleet. Traditionally, you might try to patch these live, instance by instance—a “band-aid” approach that is both time-consuming and prone to configuration drift. Even worse, the next time your auto-scaling group fires up a new instance, it uses the same flawed base image, and the vulnerability reappears like a ghost.
This manual, reactive cycle highlights a few compounding effects from this operational friction:
- Patching the same bug 50 times across 50 VMs instead of fixing it once at the source.
- New workloads inherit risks because the parent image is outdated.
- Coordinating reboots and redeployments without a centralized plan often leads to downtime or missed assets.
Orca Missions stop the cycle and refocus your team on the cure rather than the symptoms. In this mission example, vulnerable VMs are identified and tied back to the specific source images (AMIs, Golden Images, etc.) responsible for the majority of your high-risk alerts. Impacted assets and their associated downstream risks are organized and investigated.
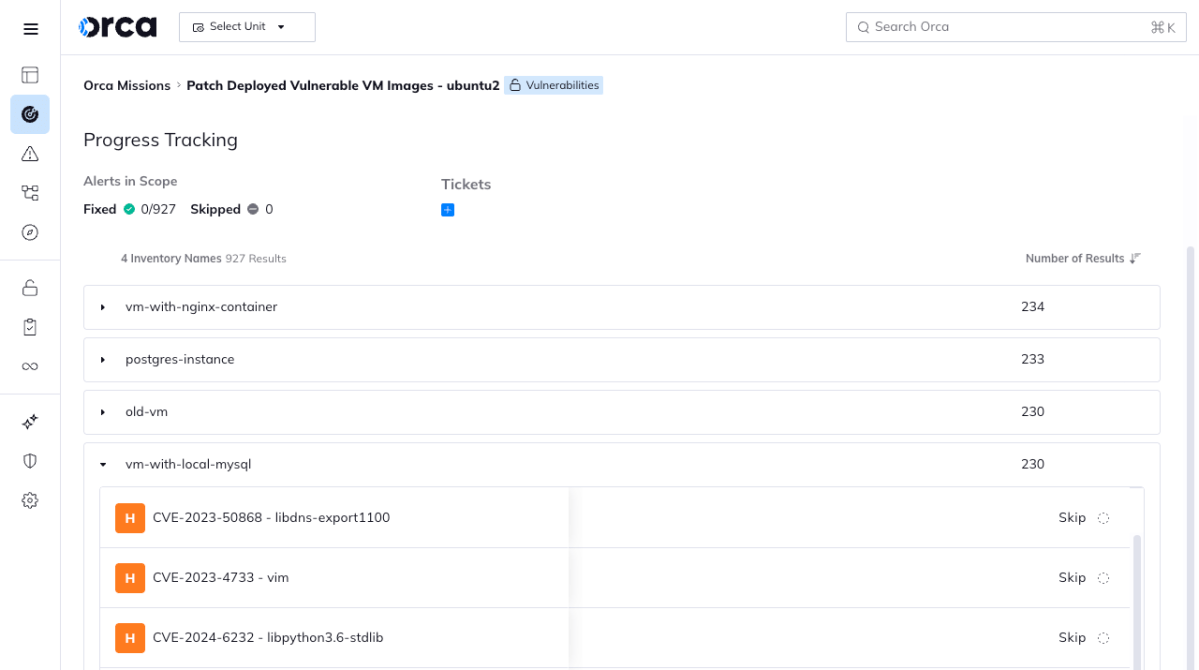
Instead of manually sifting through 500+ separate tickets, the mission gives you the evidence and plan to address the underlying packages in a single orchestrated workflow. By patching the source image and triggering a coordinated rebuild/redeploy, every dependent asset inherits the fix automatically. In a few steps, you can achieve a massive reduction in your vulnerability backlog through a singular, scalable action.
One Mission, One Intelligent Plan
By using Orca Missions, we handle the signals and create a tailored remediation plan based upon Orca’s intelligence and findings. Rather than addressing one alert, one asset, one vulnerability at a time, Missions allows you to get a birds-eye view of the entire risk vector and create a context-rich execution strategy. Now you can focus your attention on the right resources with a direct explanation of the effort required and impact to your organization; giving you back hours spent triaging alerts and remediating risks in siloes. With Orca, you equip your organization with a clear, measurable throughline all the way from identification to remediation.
Command Your Cloud With Orca
Orca offers a unified and comprehensive cloud security platform that identifies, prioritizes, and remediates security risks and compliance issues across AWS, Azure, Google Cloud, Oracle Cloud, Alibaba Cloud, and Kubernetes. The Orca Cloud Security Platform leverages Orca’s patented SideScanning™ technology to provide complete coverage and comprehensive risk detection.
Learn more
Interested in seeing how the Orca Platform can help you command your cloud? Schedule a personalized 1:1 demo.