Table of contents
Over the past decade, protecting cloud-native applications has evolved. At first, security was reactive, driven by the traditional agent approach. Then came full cloud estate observability enabled by agentless technology. Now, cloud protection strategies return to a healthy balance of agentless visibility and real-time detection and response.
Orca is focused on securing the entire lifecycle of cloud-native applications. This isn’t confined to covering code, cloud, and runtime. This includes the entire lifecycle of how security work gets done. The Orca Platform is here to command your cloud, from observation to action. From seeing issues to resolving them.
Resolution happens through code fixes, console changes, policy-driven enforcement, and now, agentic AI.
In this blog, we cover the major product announcements we’ll be showing at RSAC 2026. Visit booth #1035 in the South Hall of Moscone to get a demo of these new capabilities.
- Meet Orca’s Newest Agents, powered by Orca AI
- Detect Real-time AI Usage with Orca Sensor
- Efficiently Group Remediation Effort with Missions
- Orca Adds Code Reachability Analysis to the Platform
#1 | Meet Orca’s Newest Agents, powered by Orca AI
In the jump from generative AI to AI agents that make conclusions and take action, two things are painstakingly clear:
- context is king
- transparency builds trust
At Orca, we know that context drives clear prioritization, action, and security outcomes. That’s why we’ve built our Unified Data Model to ingest and normalize data from data sources across the security ecosystem. This foundation powers many core capabilities like dynamic risk scoring and attack paths. And now, it powers the context for our agentic AI future.
Introducing the Threat Investigation Agent
Orca’s Threat Investigation Agent simplifies the process of turning data into actionable insight by telling you the what, why, and how of an attack. As a result, teams can spend less time hunting for context and focus on the most impactful work—stopping threats. With the Threat Investigation Agent, you get:
- Actionable security outcomes faster than any human could research and summarize for you
- The whole investigation lifecycle correlating signals and validating facts before proposing precise containment actions
- Transparent decision logic through an investigation report that explains the “why” behind every verdict
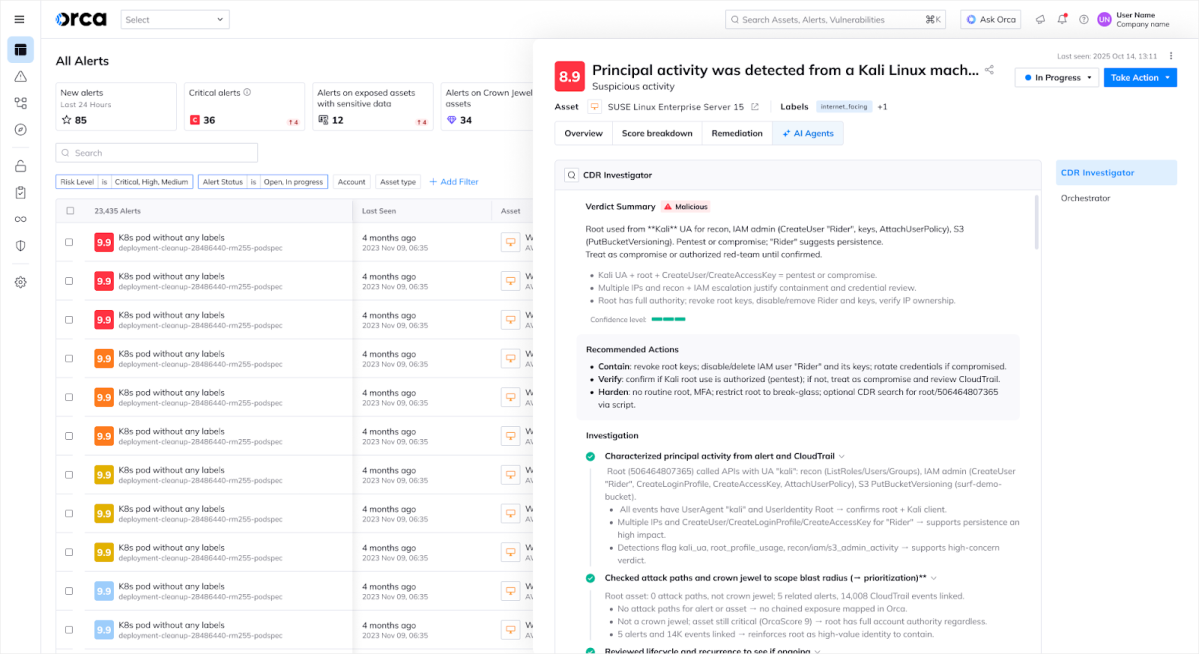
Customer trust means everything to us at Orca. As we expand our AI capabilities, we build on that trust by staying transparent with the reasoning behind AI decisions.
Introducing the AppSec Triage Agent
Most code scanners that deliver SAST produce an overwhelming number of false positives. These false positives waste developer time, erode trust between security and developers, and bury real risk. To ease this burden and help teams focus on true positive vulnerabilities, Orca is introducing the AppSec Triage Agent for SAST findings.
Instead of using rigid rules, the AppSec Triage Agent analyzes the code context of SAST findings and determines if the alert is a false positive. If identified as a false positive, Orca reduces the risk score of the issue. This automatically deprioritizes alerts and reduces noise. To ensure we are building trust in these AI-driven conclusions, customers can review the reasoning and rollback any false positive designations if they disagree with the conclusion.
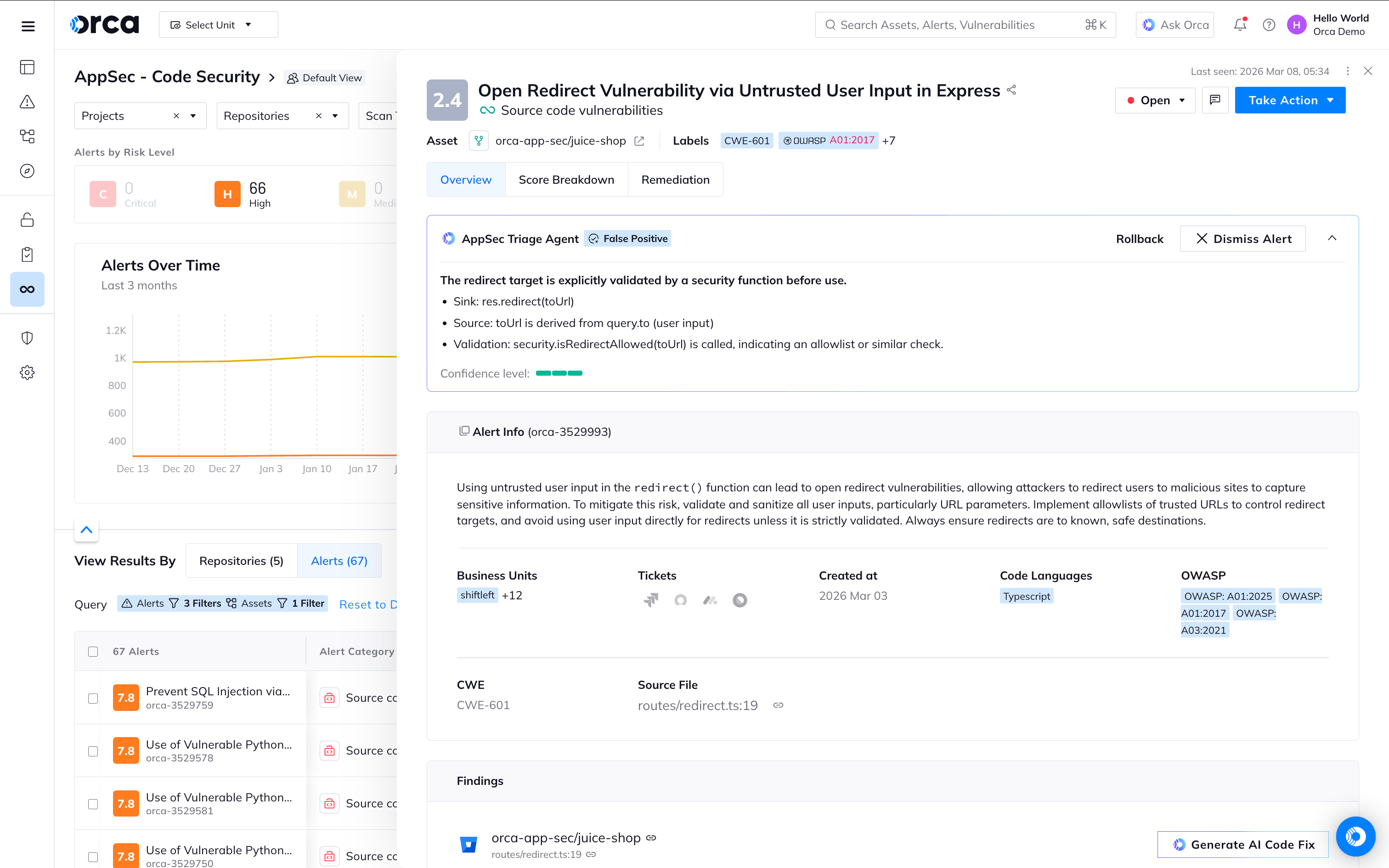
Customers have the option to automatically dismiss alerts that the AppSec Triage Agent identifies as false positives based on confidence level. For true positives, customers can lean on our AI-driven code remediation and create a PR with AI-generated code fixes.
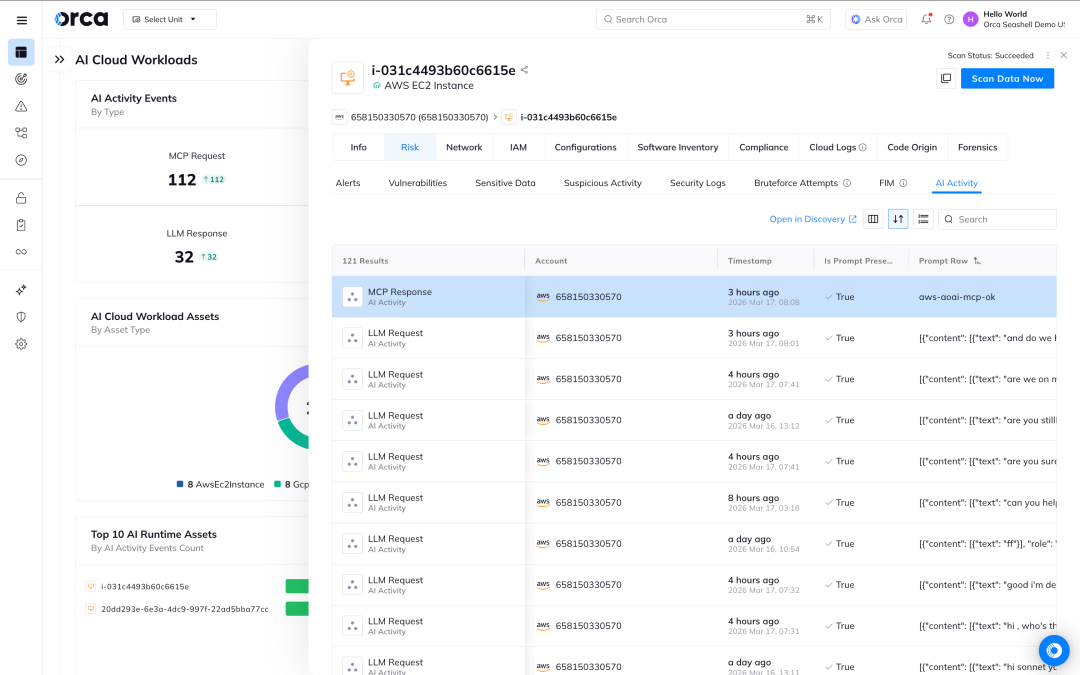
#2 | Detect Runtime AI with Orca Sensor
AI is accelerating the rate of change exponentially. Being the department of “no” isn’t actually going to stop people from using AI. Blocking AI usage just increases shadow AI.
As CEO Gil Geron said in a recent blog, “CISOs and security teams need to understand how AI is being used, not just how it can be attacked.”
To help CISOs and security teams achieve this, Orca Sensor now identifies actual runtime usage of AI, regardless of provider or programming language.
These detections aren’t done in isolation like other AI security tools that over-index on prompt-level controls. The Orca Platform correlates this activity to workloads, processes, MCP servers, exposure details, and even identity context. This enables customers to understand:
- Which workloads are invoking LLMs
- Whether sensitive data is being sent to AI models
- Whether external actors or internal tools are using MCP
- Which AI providers and models are in use
- Whether applications are vulnerable to prompt injection
- Where MCP servers exist inside their environment
- Which identities/processes are interacting with AI
- Which 3rd party LLMs and MCPs are being used
With Orca Sensor, customers gain line of sight into how AI is being used. This gives security teams the information to connect business context with risk management when implementing AI governance at scale. As one of our customers says, “Let Orca turn your ‘no’ into ‘know’.”
#3 | Efficiently Group Remediation Effort with Orca Missions
Data alone does not drive action. Gathering all the context, while helpful, cannot drive action alone. To be truly impactful, teams need to act on insights that create measurable impact. Today, security teams are manually organizing remediation projects to strategically burn down their alerts. This exercise requires a lot of time to investigate issues and justify the effort, which delays the real work—implementing fixes. In a time when engineering velocity is increasing, security teams need an easy way to batch work together for high impact in risk reduction with low effort.
This is why we’ve created Orca Missions.
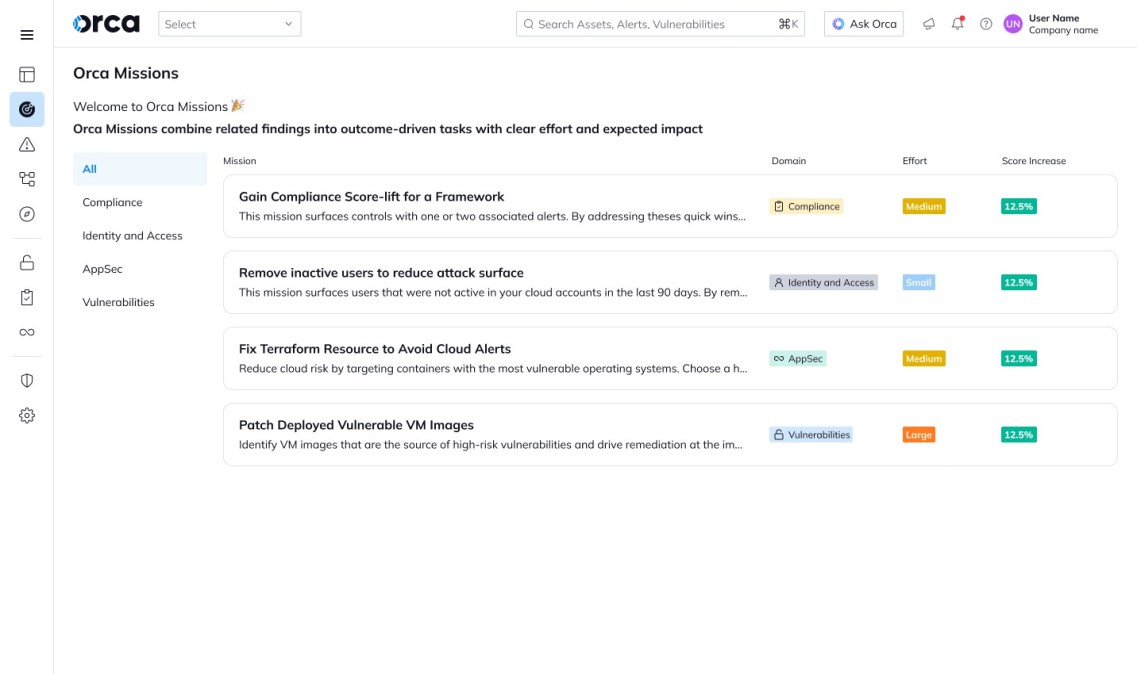
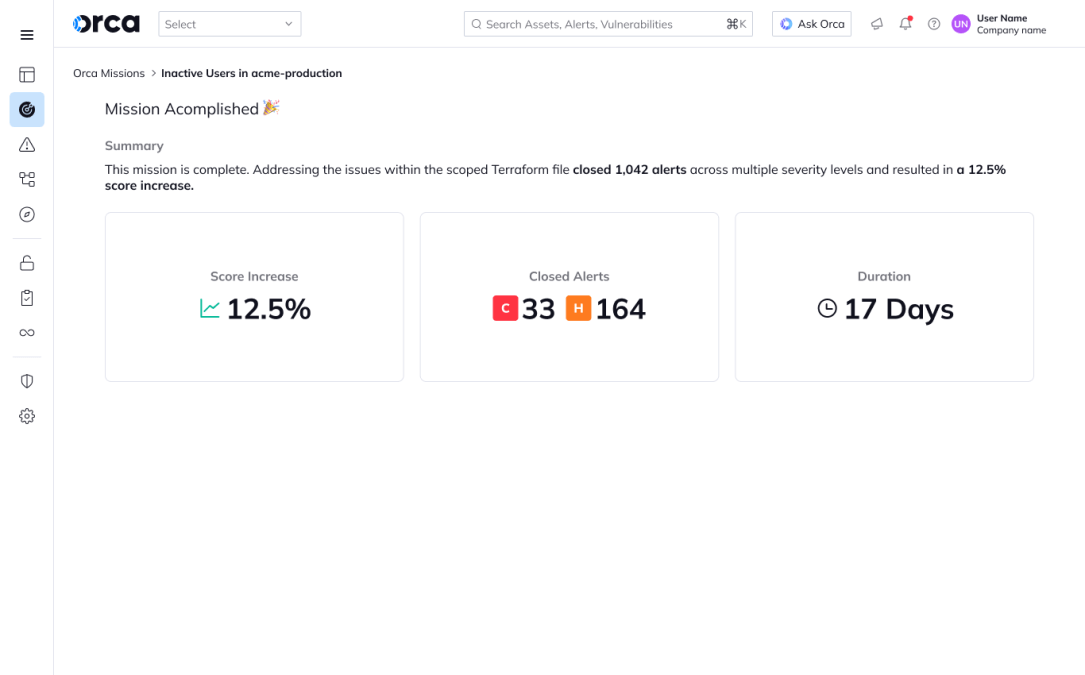
Orca automatically groups findings into a Mission—a specific, actionable, and achievable initiative with a clear finish line. With Orca Missions, teams can drive ownership and deadlines for remediation projects, providing a focused workflow where success is reached only when the predefined objective is technically verified as complete.
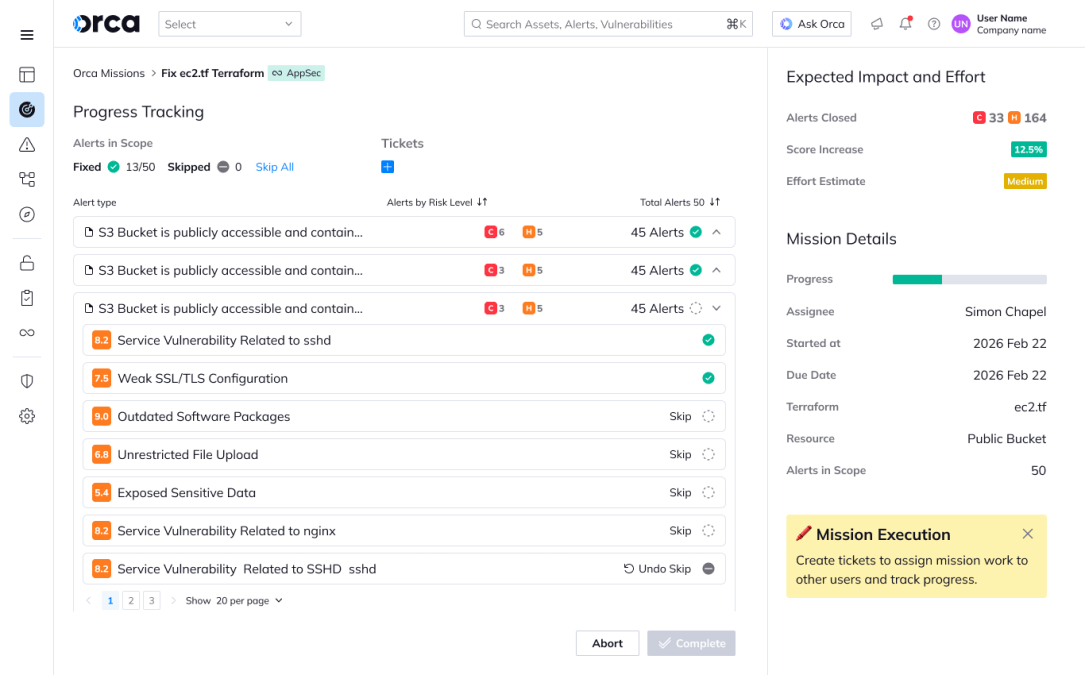
As the team makes progress in the Mission, the expected impact on security posture remains in view. When a mission is complete, your organization’s security score improves, reflecting clear, measurable impact to risk reduction.
#4 | Orca Adds Code Reachability Analysis to the Platform
Most software composition analysis (SCA) vendors that deliver reachability analysis only determine if a vulnerable package is being used. Orca’s Code Reachability Analysis goes one step further to determine if the vulnerable package’s code, like a specific function, is actually being used in the source code. If the specific code that invokes the vulnerable method isn’t found, then the actual vulnerability isn’t as high a priority to be remediated.
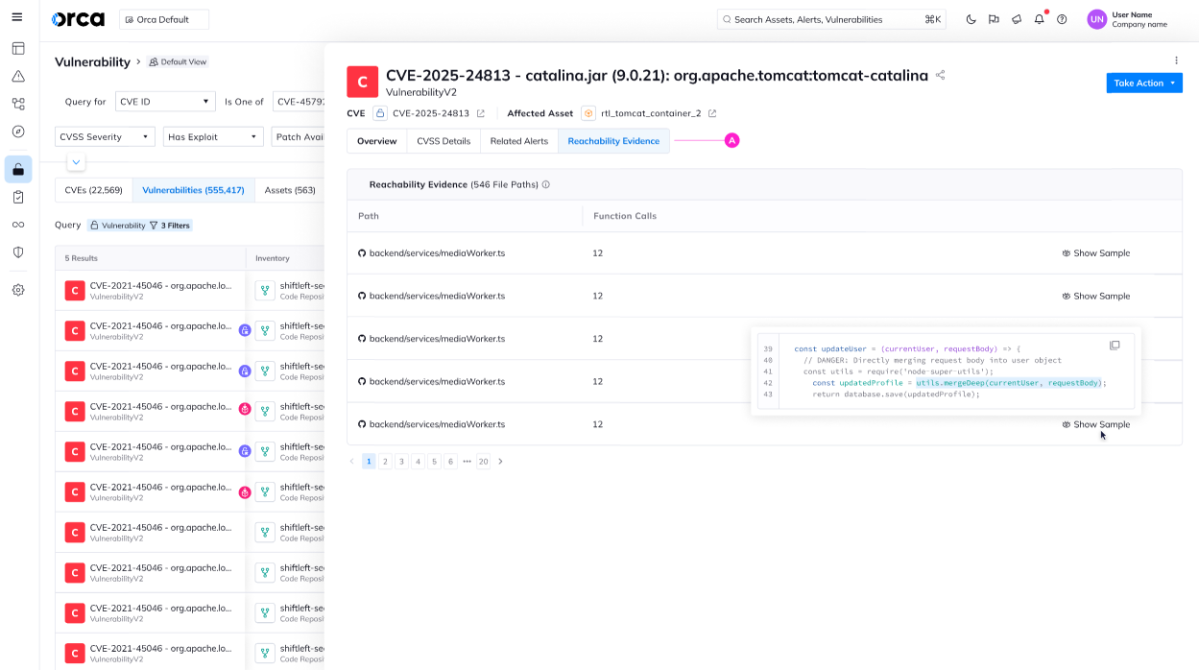
By taking a code analysis approach, the Orca Platform now provides 360-degree reachability analysis for vulnerabilities. Last year, Orca announced Agentless Reachability Analysis, taking a cloud approach to determine if attackers could reach vulnerable packages in running workloads. We expanded this analysis with Orca Sensor to deliver Dynamic Reachability Analysis, verifying our agentless findings and enhancing prioritization. Today, we’re introducing Code Reachability Analysis. This full spectrum of reachability analysis ensures vulnerability management teams focus their efforts on the most important issues that are reachable, exploitable, and fixable.
Command Your Cloud with Orca
Orca delivers a unified, comprehensive cloud security platform that identifies, prioritizes, and remediates security risks and compliance issues across AWS, Azure, Google Cloud, Oracle Cloud, Alibaba Cloud, Tencent Cloud, and Kubernetes. Built as a Cloud Native Application Protection Platform (CNAPP), the Orca Platform provides comprehensive visibility and contextualized risk insights that enable security, development, and operations teams to secure what they build and run in the cloud.
Learn More
Interested in seeing how the Orca Platform can help you command your cloud? Schedule a personalized 1:1 demo.