Users with Console Access do not have MFA Enabled
Hazardous (3)
AWS CIS, AWS Foundational Security Best Practices Controls, CCPA, CSA CCM, FedRAMP, GDPR, HIPAA, ISO/IEC 27001, New Zealand Information Security Manual, NIST 800-53, NIST-CSF, Orca Best Practices, PCI DSS, SOC 2
About AWS Management Console
AWS Management Console is a web application that gives users all the controls they need to manage their AWS resources. All AWS services are accessible, including compute, storage, governance, security, and analytical services.
Before you can access the AWS console, you have to log in to your AWS account.
Cloud Risk Description
If only a username and password are required to log in to the AWS console, brute force attacks can potentially enable malicious actors to acquire such credentials and gain unauthorized access. During a brute force attack, a malicious actor repeatedly tries different password combinations until they find the right one.
Since the console provides direct access to critical resources and services, it’s important to secure its login procedure using multi-factor authentication (MFA). MFA adds an extra layer of authentication assurance beyond traditional credentials, reducing the risk of unauthorized access.
When a user logs in with MFA enabled, they’re prompted for their username and password—as well as an authentication code from their physical or virtual MFA token. It’s recommended MFA be enabled for all accounts having a console password.
How Can Orca Help?
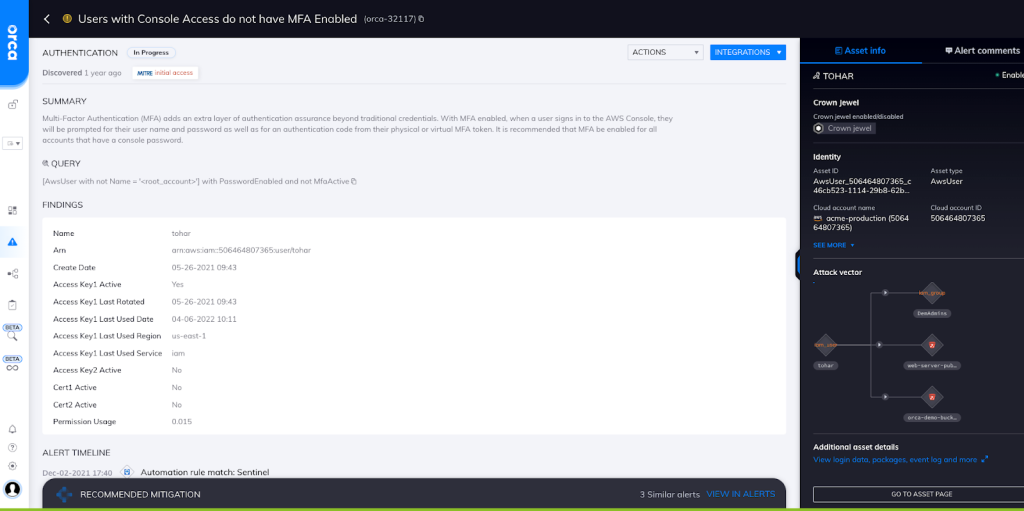
Orca detects cloud IAM risks and generates an alert if a console user does not have the requisite MFA (see screenshot).
Orca ensures that cloud password policy settings meet industry guidelines pertaining to MFA use, minimum password length, use of special characters, password age, password reuse, and more.
Recommended Mitigation Strategies
-
Turn on MFA for any users having console access.
-
Only provide console access to people who need it.
-
Follow the principle of least privilege (PoLP).
-
If a user assumes a new role and no longer requires console access, immediately revoke their access.
Useful Links
- Controlling user access to the AWS Management Console: https://docs.aws.amazon.com/IAM/latest/UserGuide/console_controlling-access.html
- Using multi-factor authentication (MFA) in AWS: https://docs.aws.amazon.com/IAM/latest/UserGuide/id_credentials_mfa.html
- AWS Management Console: https://aws.amazon.com/console/
- Security best practices and use cases in AWS Identity and Access Management: https://docs.aws.amazon.com/IAM/latest/UserGuide/IAMBestPracticesAndUseCases.html
- Policies and permissions in IAM: https://docs.aws.amazon.com/IAM/latest/UserGuide/access_policies.html
Orca Security, the cloud security innovation leader, provides cloud-wide, workload-deep security and compliance for AWS, Azure, and GCP - without the gaps in coverage, alert fatigue, and operational costs of agents.
