Table of contents
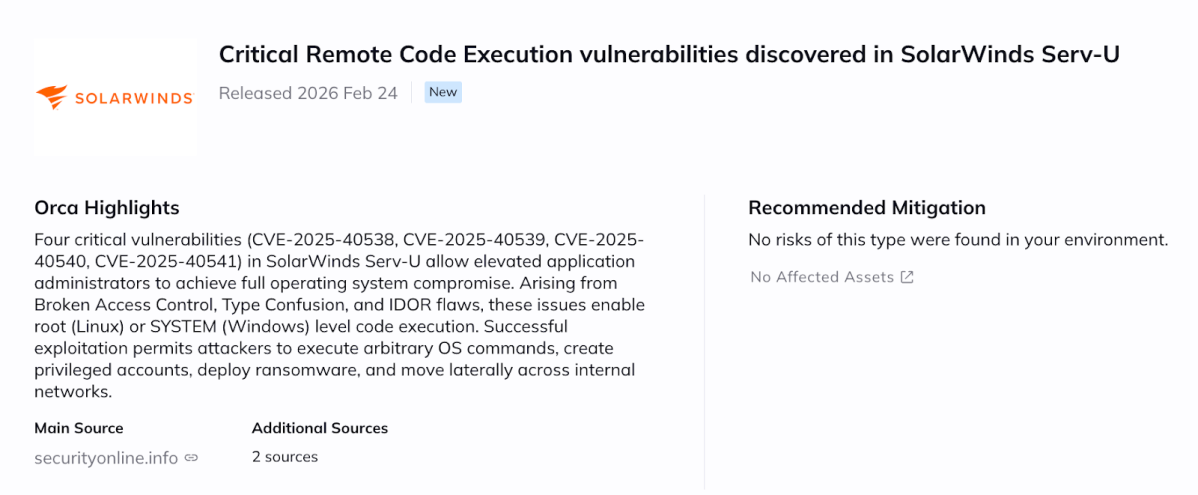
SolarWinds has released Serv-U 15.5.4 to address four critical vulnerabilities — CVE-2025-40538, CVE-2025-40539, CVE-2025-40540, and CVE-2025-40541 (CVSS 9.1) — that can allow attackers to execute arbitrary code with root (Linux) or SYSTEM (Windows) privileges. Organizations running Serv-U should update immediately.
These vulnerabilities impact SolarWinds Serv-U Managed File Transfer, a platform frequently deployed as an internet-facing FTP/FTPS/SFTP gateway or as an internal file exchange service handling sensitive data.
Technical Details
The four vulnerabilities differ in root cause but share a common outcome: operating system-level code execution.
- CVE-2025-40538 — Broken Access Control → RCE
A broken access control condition may allow an attacker with elevated Serv-U privileges (such as domain admin or group admin) to create a system administrator account and ultimately execute arbitrary code as root.
- CVE-2025-40539 & CVE-2025-40540 — Type Confusion → Native Code Execution
Two distinct type confusion flaws in Serv-U’s internal logic can result in arbitrary native code execution with root privileges. Type confusion vulnerabilities occur when memory objects are misinterpreted, potentially enabling control flow manipulation.
- CVE-2025-40541 — IDOR → RCE
An insecure direct object reference (IDOR) vulnerability may allow improper invocation of internal functionality, leading to native code execution as root.
While exploitation requires elevated Serv-U privileges, the critical issue is privilege boundary crossing: these flaws convert application-level administrative access into full operating system compromise.
Why This Matters
Serv-U commonly operates in high-value roles, including:
- Internet-facing managed file transfer gateways
- External B2B file exchange systems
- Internal file distribution services
Because Serv-U often runs with elevated operating system privileges, successful exploitation enables:
- Arbitrary OS command execution
- Creation of new privileged system accounts
- Deployment of ransomware or persistence mechanisms
- Lateral movement within internal networks
These vulnerabilities do not provide anonymous initial access. However, in real-world scenarios where administrative credentials are compromised — through phishing, password reuse, or credential spraying — they significantly increase the impact of that compromise.
Affected Components and Versions
The vulnerabilities are addressed in:
- SolarWinds Serv-U 15.5.4
Organizations running earlier versions should assume exposure and upgrade without delay.
Mitigation and Patching Guidance
Organizations should immediately upgrade to:
- SolarWinds Serv-U 15.5.4
Additional security measures include:
- Restricting exposure of the Serv-U administrative interface
- Enforcing strong password policies and multi-factor authentication
- Rotating administrative credentials
- Reviewing administrative activity logs for anomalies
- Ensuring Serv-U servers are properly segmented from critical infrastructure
Why Is a 2025 CVE Emerging Now?
Although the identifiers are labeled 2025, CVE IDs are often reserved in advance and publicly disclosed once patches are released. In this case, the vulnerabilities were assigned 2025 identifiers and published alongside the 15.5.4 update.
How can Orca help?
Orca enables organizations to quickly identify Serv-U deployments and determine which assets are running versions prior to 15.5.4. By correlating asset exposure, internet accessibility, and runtime context, Orca helps security teams prioritize remediation based on real operational risk.
Beyond version visibility, Orca provides contextual insight into exposed services and workload behavior, helping teams focus on assets where exploitation would have the highest impact.