Table of contents
We are excited to announce Orca now integrates with Drata, an Agentic Trust Management Platform, to offer comprehensive vulnerability assessments to identify compliance risks across your digital estate. Orca’s integration empowers Drata with Vulnerability Management findings from your Orca Security platform. The combination of Orca’s deep technical telemetry with Drata’s governance framework ensures cloud assets are discovered, monitored, and satisfy compliance requirements.
In today’s cloud-centric reality, reactive remediation is not enough for security teams to address the two-front war of unknown and dangerously known exploits that leave your organization vulnerable to threat actors. Since its creation in 2021, CISA’s catalog of Known Exploited Vulnerabilities (KEV) has jumped from 287 to over 1,500 in less than 5 years. Security teams simply do not have the ability to be everywhere all at once and need the right solution to aid the discovery, enumeration, and reporting of compliance gaps.
How the Drata Integration Automates Your Vulnerability Surface Monitoring
Closing these gaps requires an integrated system where Compliance Management and Vulnerability Management act as the strategy and the engine of your defense. This partnership ensures that the risk-reduction workflow is established and governed by a plan that aligns security actions with organizational objectives. This plan can then be operationalized through the deployment of Vulnerability Scanning–an automated technique used to proactively identify cloud-native assets, ephemeral infrastructure, and associated vulnerabilities.
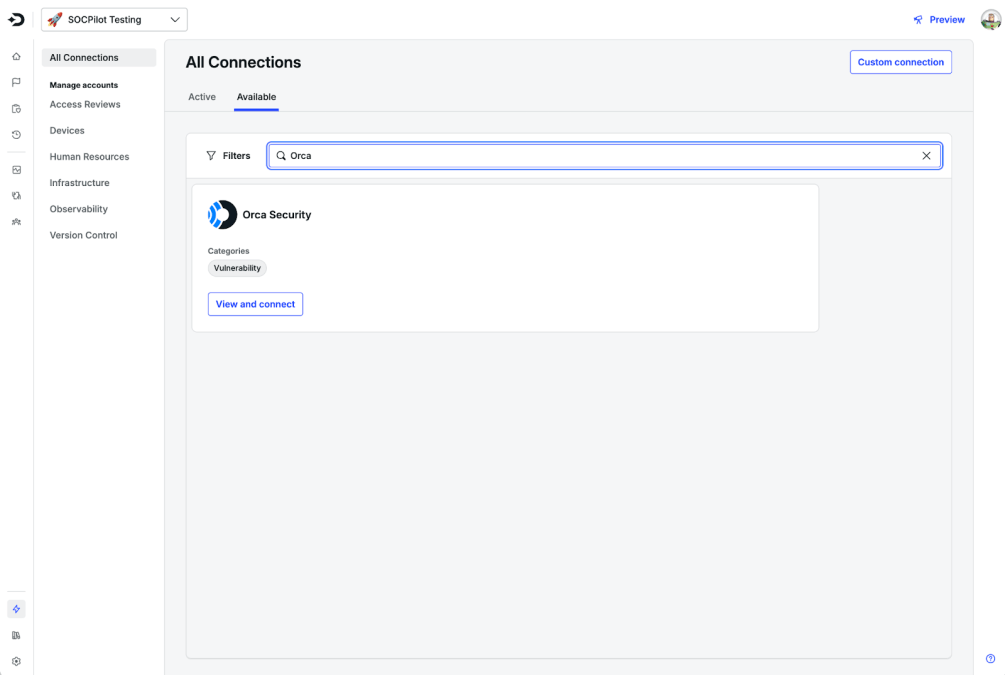
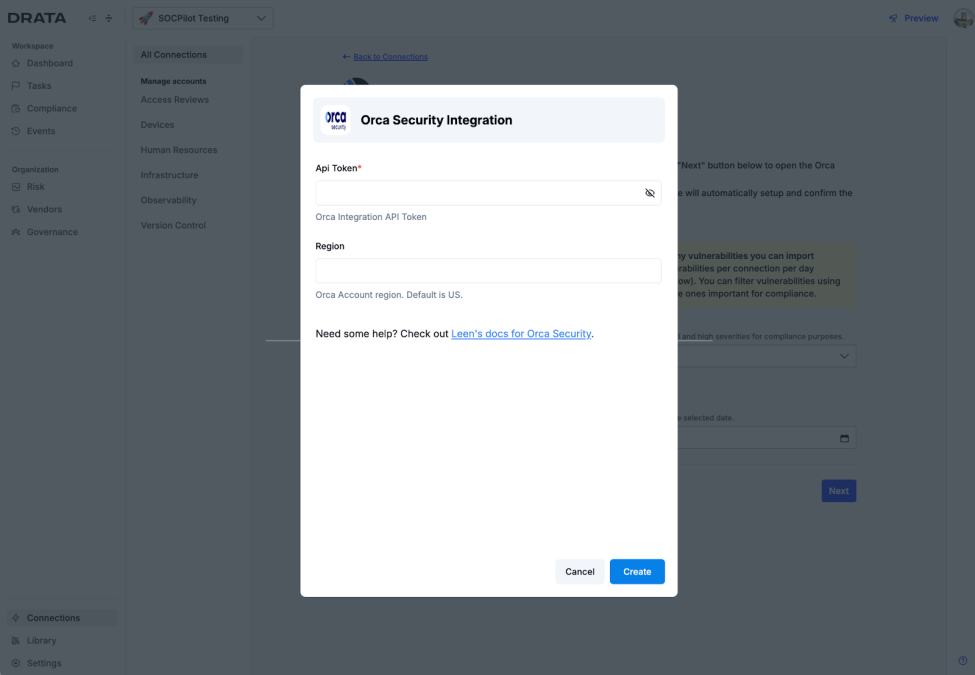
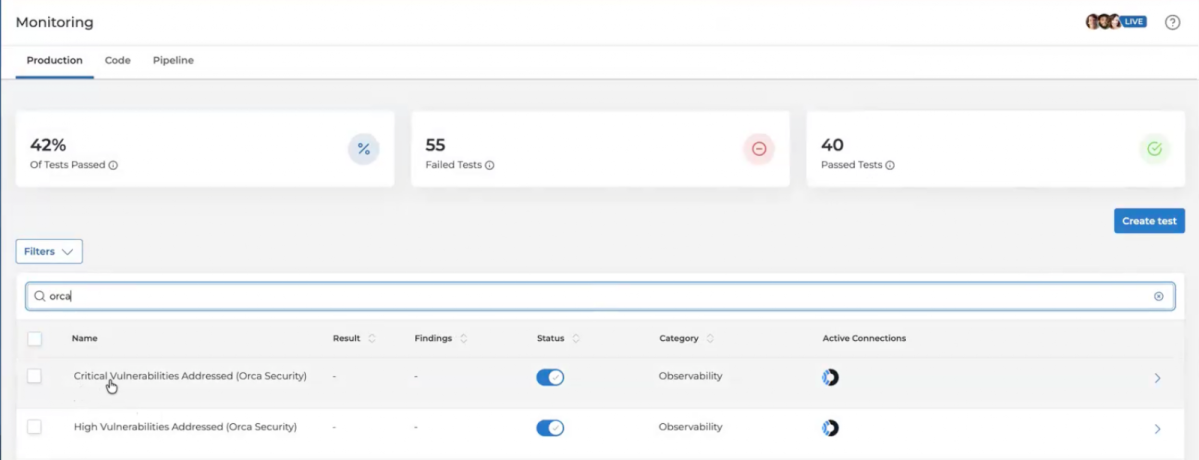
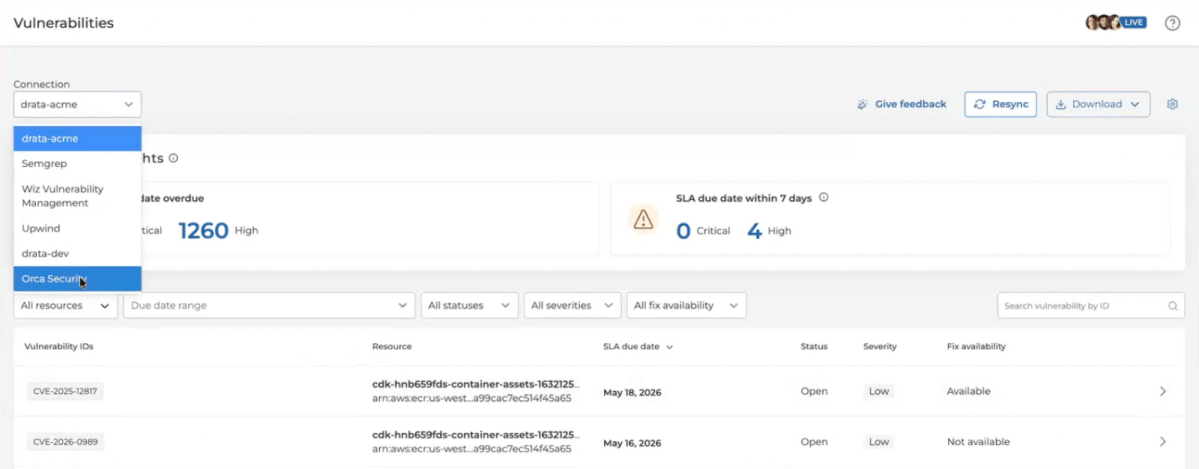
The integration of Orca’s Vulnerability Management and scanning capabilities with Drata’s Compliance Management automation transforms mandatory regulatory compliance into a repeatable, audit-ready cycle of risk reduction. By connecting with Orca, you easily and automatically satisfy automated vulnerability monitoring test requirements within Drata. To get started, search for Orca Security in Drata under Available Connections.
Mapping Findings to Evidence via the Orca and Drata Integration
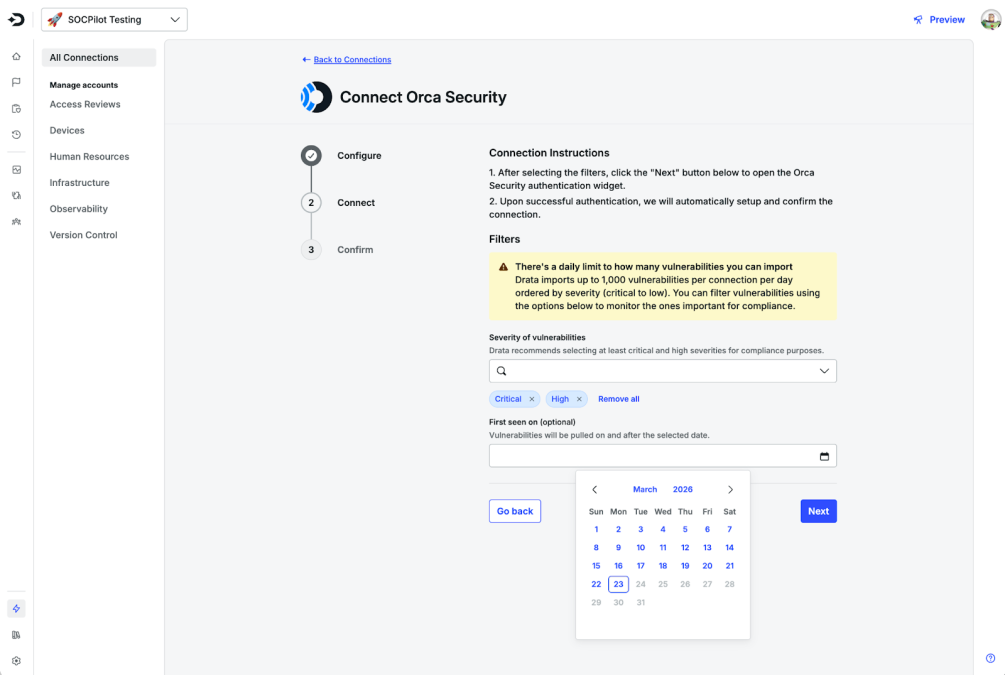
Once you have connected and configured your vulnerability severity scope, Drata automatically maps evidence from Orca’s vulnerability data to the Drata Control Framework (DCF). The DCF is Drata’s centralized, proprietary set of controls to address scanning requirements across common industry regulations, standards, and frameworks (such as SOC 2, ISO 27001, and PCI DSS).
Drata periodically pulls vulnerability data from Orca to verify that scans are being performed according to your internal policies. Thus eliminating the need for screenshots of scan reports by streamlining compliance reporting with automated evidence collection.
By integrating Orca with Drata, security findings automatically map to your organization’s compliance strategy, making it easier than ever to identify compliance gaps, gather the necessary evidence to take remediation action, and ensure full audit readiness.
Next Steps: Scale Your Compliance Program with Orca + DrataLearn more
Interested in discovering the benefits of the Orca Platform and how it can be integrated with tools like Drata? Schedule a personalized 1:1 demo, and we’ll show how you can use Orca to identify, prioritize, and remediate risks in your cloud environment. If you already use both Orca and Drata, follow the steps in the documentation to set up the integration.
Command Your Cloud With Orca
Orca offers a unified and comprehensive cloud security platform that identifies, prioritizes, and remediates security risks and compliance issues across AWS, Azure, Google Cloud, Oracle Cloud, Alibaba Cloud, Tencent Cloud and Kubernetes. The Orca Cloud Security Platform leverages Orca’s patented SideScanning™ technology to provide complete coverage and comprehensive risk detection.