Table of contents
The gap between security data and security decisions has never been smaller.
Cloud security teams are drowning in the right data. They have asset inventories, vulnerability feeds, compliance scores, CloudTrail logs, attack paths. The problem isn’t data availability. It’s the distance between raw findings and the analysis a practitioner actually needs to act.
That gap is what today’s announcement is designed to close.
Orca Security’s AI Skills Hub is now live and compatible with Claude, Codex, and Cursor. These cloud security skills let security engineers, developers, SOC analysts, and security leaders query, investigate, and operationalize Orca data. Customers never have to learn another query language, write a single line of code, or leave their existing tools. Just use natural language to understand what matters most and drive action.
Orca’s Unified Data Model Drives Reliable AI Workflows
When a model doesn’t have access to ground truth, it fills the gaps with inference, leading to AI hallucinations. That’s reasonable behavior in a general-purpose assistant. It’s an unacceptable one when the output is a triage verdict, a remediation recommendation, or an incident investigation.
Most security AI integrations expose a slice of the data: alerts from one source, asset metadata from another, compliance scores pulled separately. The model reasons across disconnected fragments and the seams show: contradictory conclusions, missing context, recommendations that don’t account for the actual environment.
Orca’s Unified Data Model was built to eliminate those seams. Every asset, alert, identity, data finding, attack path, and CDR event is ingested into a single continuously updated graph that is correlated, normalized, and queryable as a coherent whole. A vulnerability on an EC2 instance is understood in relation to the instance’s network exposure, the IAM role attached to it, the attack paths that pass through it, and the compliance frameworks that govern it. Not as four separate facts in four separate systems, but as one connected picture.
Orca’s structural coherence is what makes AI workflows reliable at scale. When Claude queries Orca through the MCP Server, it’s not assembling a response from 8 different systems with partial signals. It’s reasoning against a complete, authoritative representation of your cloud environment. AI output is only as trustworthy as the data underneath it. Orca’s Unified Data Model is why the output is trustworthy.
What Connecting the Orca MCP Server Does
Connecting Orca with Claude is like giving a doctor your full medical history to diagnose and treat your health concerns. Claude gets direct access to your Orca environment data through Orca’s MCP Server.
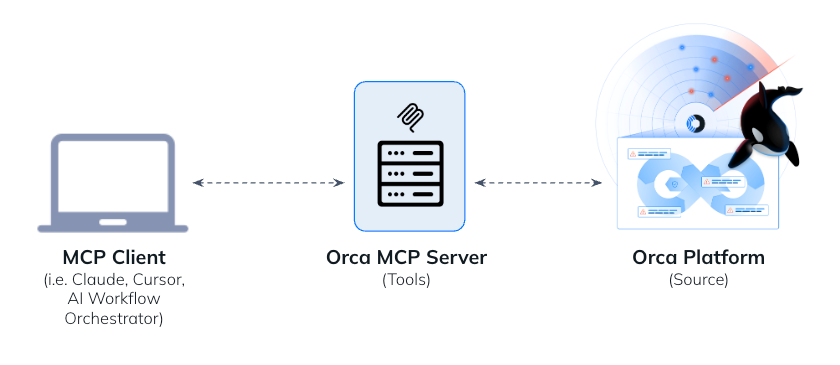
When you ask a question, Claude queries your actual asset inventory, your open alerts, your compliance frameworks, your CloudTrail logs.
The result is a conversation with AI that actually knows what it’s talking about.
Ask “what’s exposed to the internet right now?” and Claude pulls your live exposure map including internet-facing assets ranked by exploitability, public storage buckets, exposed management interfaces, and outside-in attack paths.
Ask “who created this misconfiguration?” and Claude traces the resource back through CloudTrail audit logs, IaC source code, and git blame data to identify the exact deployment that introduced the issue and who owns the fix.
Agent Skills to Operationalize Orca Data
If connecting AI to Orca’s MCP Server is like giving the doctor your medical history, agent skills are like specialist consultations. The MCP Server provides context, the skills deliver expertise to know what to look for and how to interpret what they find. The result is AI output you can act on immediately, not a starting point for more investigation.
Skills are purpose-built, role-specific workflows that codify specialized security logic, like the kind of investigation sequence a senior analyst runs, but automated and repeatable. Each skill is triggered by natural language and follows a consistent pattern: gather relevant Orca data, apply expert-level analysis logic, deliver a verdict-first output with drill-down options.
Orca’s AI Skills Hub starts with 11 out-of-the-box skills covering the most common and most time-intensive cloud security workflows:
- orca-morning-briefing answers “what happened while I was away?” It scans the last 24–72 hours for new critical alerts, escalated findings, compliance drift, CDR anomalies, crown jewel risks, and aging unactioned findings. Then it delivers a scannable dashboard with progressive drill-down by keyword.
- orca-alert-triage answers “what is this alert and should I care?” It produces verdict-first summaries with confidence scoring, behavioral timelines, blast radius calculations, and Orca-first automated investigation before suggesting any manual steps. Remediation code is written directly to a file in the format you specify— Terraform, CloudFormation, ARM/Bicep, Pulumi, CLI, or step-by-step instructions.
- orca-impact-analysis answers “if I fix this, what else closes and what breaks?” Before a fix is applied, this skill maps all alerts sharing the same root cause, identifies attack paths that break, calculates compliance score improvements per framework, and surfaces production dependencies that might be disrupted. Teams can use this to make informed fix-or-defer decisions.
- orca-config-origin answers “who did this, and what introduced the issue?” It traces any alert back through CDR audit logs and Orca CodeOrigins / Shift Left data to identify the specific deployment, the IaC source file and line number, the git commit author, and the full timeline from code commit to alert detection.
- orca-identity-review answers “is this identity overprivileged, and what’s the blast radius?” It compares effective permissions against 30-day CloudTrail usage, identifies dangerous permissions never exercised, maps lateral movement potential, and generates a least-privilege policy recommendation with a safe deployment checklist.
- orca-investigate answers “what happened, who did it, and how far did they get?” It runs CDR-powered incident investigation, clustering events into sessions, mapping actions to MITRE ATT&CK techniques, assessing blast radius, extracting IOCs in copy-paste format for SOC tools, and delivering a verdict with confidence scoring.
The remaining skills—orca-asset-profile, orca-compliance-gap, orca-data-exposure, orca-exposure-map, and orca-cloud-cost-optimizer—cover the full range of daily security operations: asset 360 views, compliance gap analysis with phased remediation plans, DSPM-style sensitive data discovery, external attack surface mapping, and cloud cost optimization across compute, storage, and networking.
Skills ship with the logic already written. An analyst doesn’t configure a workflow, define a query schema, or map data fields. They type a question like “triage alert orca-9012345” or “what’s our PCI compliance gap?” and the skill handles everything from data retrieval to output formatting. See an example of how easy it is to ask Claude to provide a daily briefing and then an impact analysis of one of the action items:
The experience is just as easy in Claude Code:
Outputs are designed for immediate use. Triage results include verdicts, confidence scores, and timeline analysis in a format readable in under 30 seconds. Remediation outputs are written to files in the IaC format the team already uses. Compliance gap analyses include projected score improvements per fix, phased over days, weeks, and months.
Skills are also extensible. Orca’s Skills Library is open-source and available at github.com/orcasecurity/orca-skills. Every skill includes its full implementation, natural language trigger patterns, and automated test suites. Teams can fork, modify, and extend skills to fit their specific workflows. Pull requests are welcome.
This isn’t a locked capability behind an enterprise tier. It’s a foundation the security community can build on.
The gap between security data and security decisions closes today.
About the Orca Cloud Security Platform
The Orca Platform delivers a unified cloud security experience that helps organizations identify, prioritize, and remediate risk across their cloud environments, applications, and AI. To get started with Orca’s MCP Server, check out our documentation.
Interested in seeing how we help you command your cloud? Schedule a personalized 1:1 demo.