Orca Security named a 2021 Gartner Cool Vendor in Cloud Security Posture Management (CSPM)
Abstract: We’re simplifying cloud security and compliance operations for AWS, Azure, and GCP by unifying the core capabilities of CSPM, CWPP, and CIEM in a single SaaS-based platform.
We’re thrilled to announce that Gartner recognized Orca Security as a 2021 Cool Vendor in Cloud Security Posture Management (CSPM). We believe one of our key differentiators is extending our reach beyond the control plane deep into the workloads themselves. Combining core CSPM with agentless Cloud Workload Protection Platform (CWPP) capabilities has been a game-changer for our customers, delivering instant time-to-value and allowing them to prioritize what matters most.
According to Gartner:
“traditional CSPM tools identify simple control plane misconfigurations that result in limited insight into overall workload risk posture. Conversely, hyper-scale cloud workload protection platforms (CWPPs) have developed feature-rich tool suites, requiring agents to enforce comprehensive visibility and protection capabilities. This often results in unused functionality, complex management procedures, and prohibitive price points.”
Siloed CSPMs and CWPPs Haven’t Kept Pace with Enterprise Business Requirements
For the past few decades, there have been two methods for delivering cybersecurity: endpoint-based and network-based. Then cloud computing came along – and we, as an industry, simply lifted and shifted to the cloud, augmenting those methods with cloud security posture managers (CSPMs), which looked at only the cloud configuration.
This patchwork of CSPMs and agent-based tools (now known as CWPPs) has two main flaws. First and foremost, agents do not work for the cloud. They have a high TCO, and they create a lot of friction within the organization. Worse, ephemeral workloads may last only a few minutes before an agent can wake up and start working. The second problem with this siloed approach is that each security tool only sees its piece of the puzzle, presenting a considerable burden to already overburdened security practitioners trying to put everything together themselves – which never works.
Gartner advises organizations to:
“Maximize the use of one third-party vendor across cloud security capability areas to reduce tool complexity. However, be cautious: many third-party vendor “suites” consist of independent acquisitions and may not actually provide coherent control from one single administration point. Set expectations accordingly and assess the reality of integration claims.”
– Gartner, Inc., How to Protect Your Clouds with CSPM, CWPP, CNAPP, and CASB, 2021, Richard Bartley
May 6, 2021
I’m reminded of one vendor who really tried to hide the fact that their CSPM + CWPP suite is an inconsistent patchwork of point solutions.
Orca delivers a single SaaS-based platform for workload and data protection, cloud security posture management, vulnerability management, and compliance management
In response to the shortcomings of agents and network scanners, Orca developed a revolutionary new technology called SideScanning™ that dives deep into the workload without the constraints and operational costs of these legacy tools. It instead collects data directly from the cloud provider’s API – as a CSPM – and from the workload’s runtime block storage out-of-band. As a result, we don’t have to run any code or send a single packet in your environment with this approach.
After a quick and easy one-time deployment, Orca surfaces the most critical risks such as vulnerabilities, malware, misconfigurations, weak and leaked passwords, lateral movement risk, misplaced PII, and more for both the workload and the cloud configuration itself, all while guaranteeing 100% coverage. Before Orca, this was simply not feasible.
According to Gartner, “Security and risk management leaders managing cloud infrastructure security should: Protect against compromise by deploying lightweight CSPM technologies that provide read-only, least-privilege automation from outside the workload (using agentless techniques such as API integration and log monitoring).”
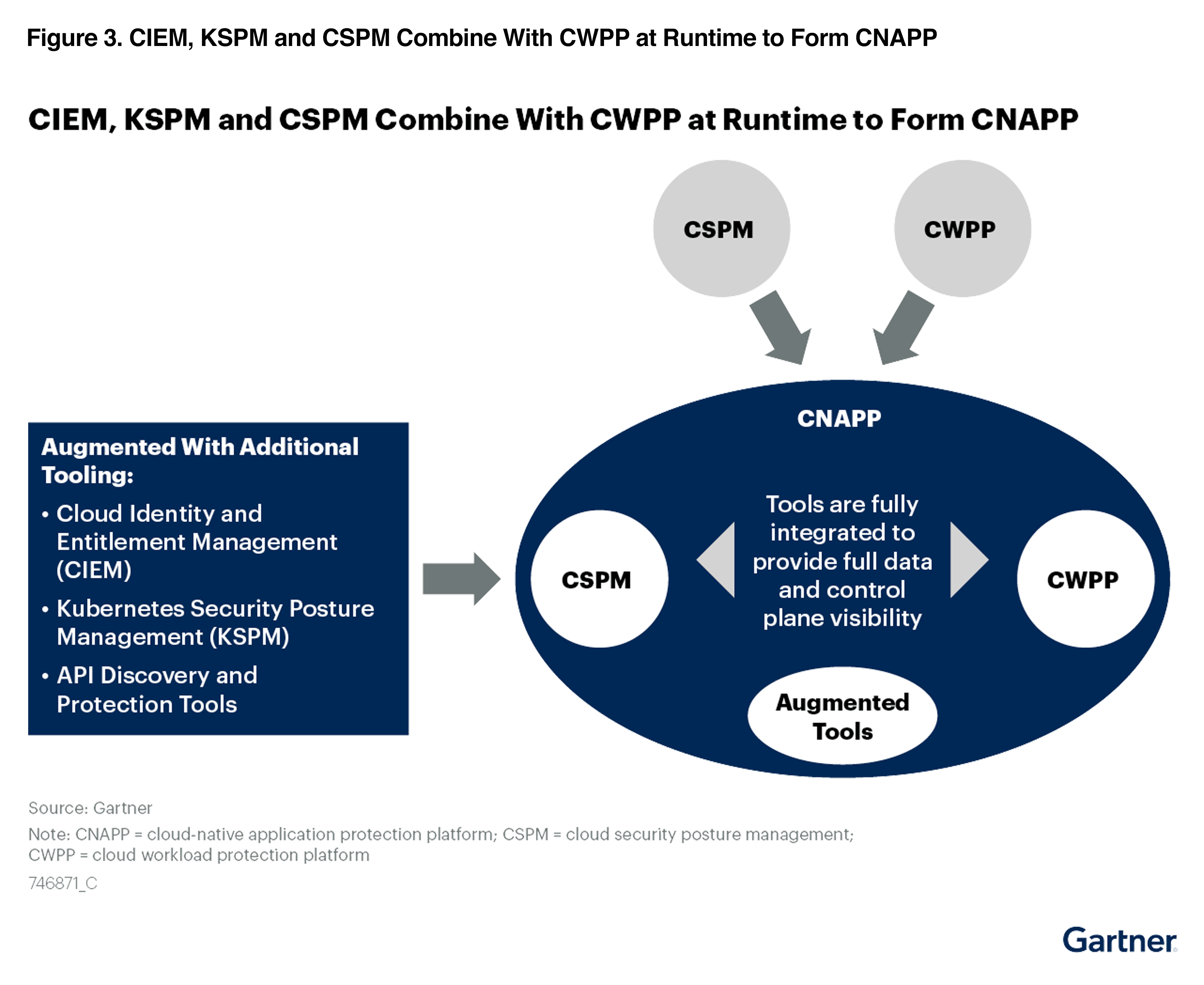
Cool Category: Cloud-Native Application Protection Platform (CNAPP)
As mentioned in the Cool Vendor report, “CSPM tools are increasingly driving the evolution of cloud workload protection platforms toward cloud native application protection platforms (CNAPP).”
It is incredibly gratifying to see Gartner establish a new and emerging category called Cloud-Native Application Protection Platform (CNAPP) that validates Orca Security’s original vision of combining the best of CSPM, CWPP, and CIEM.
CVSS Scores are Useless without Context
Unlike other solutions, Orca recognizes that risk is much more than just the severity score of the underlying security issue. In reality, it also depends on the accessibility and business impact of the at-risk asset. By building a graph encompassing all your cloud assets, software, connectivity, and trust relationships, Orca can prioritize risk based on all of these factors.
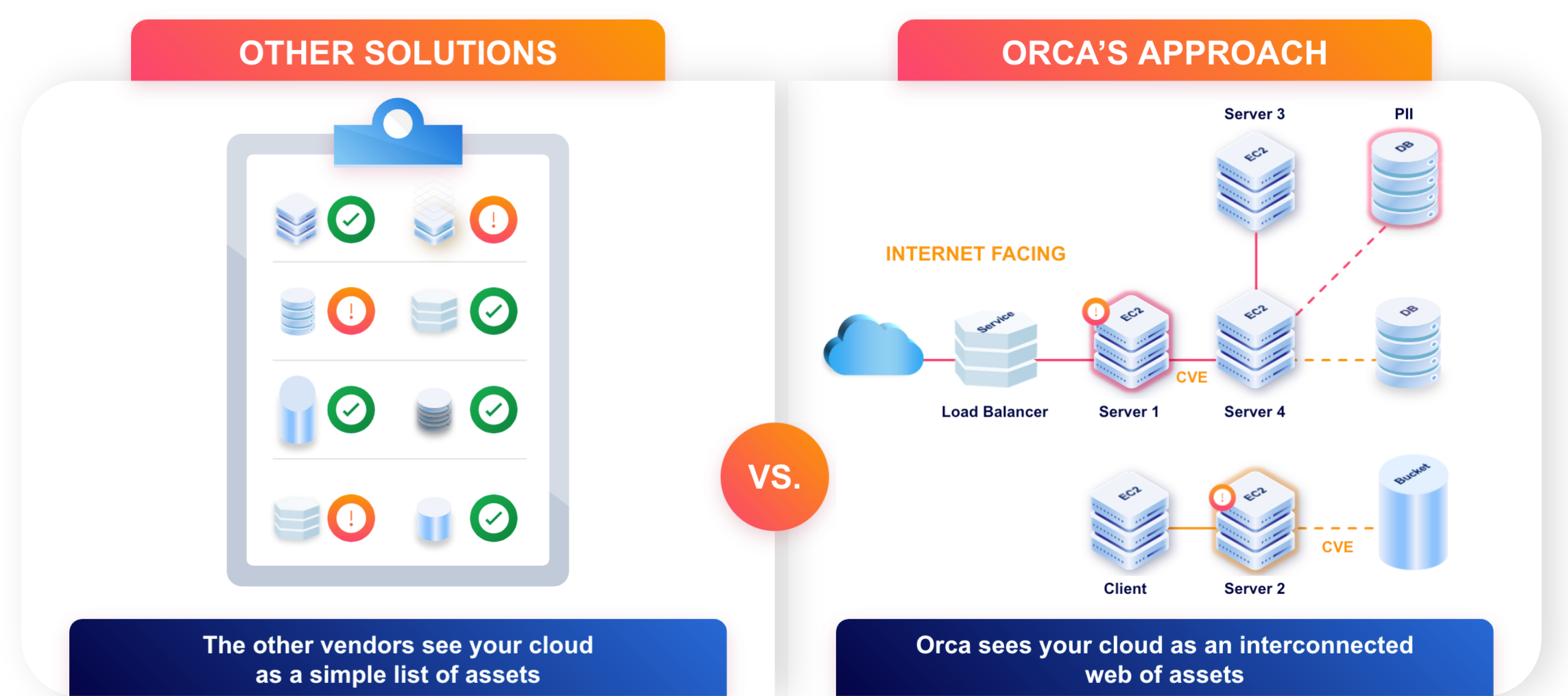
As a result of Orca’s approach to risk, we can separate the 1% of alerts that require immediate action from the 99% that do not. This helps security teams avoid alert fatigue and fix the truly critical security issues before attackers can exploit them.
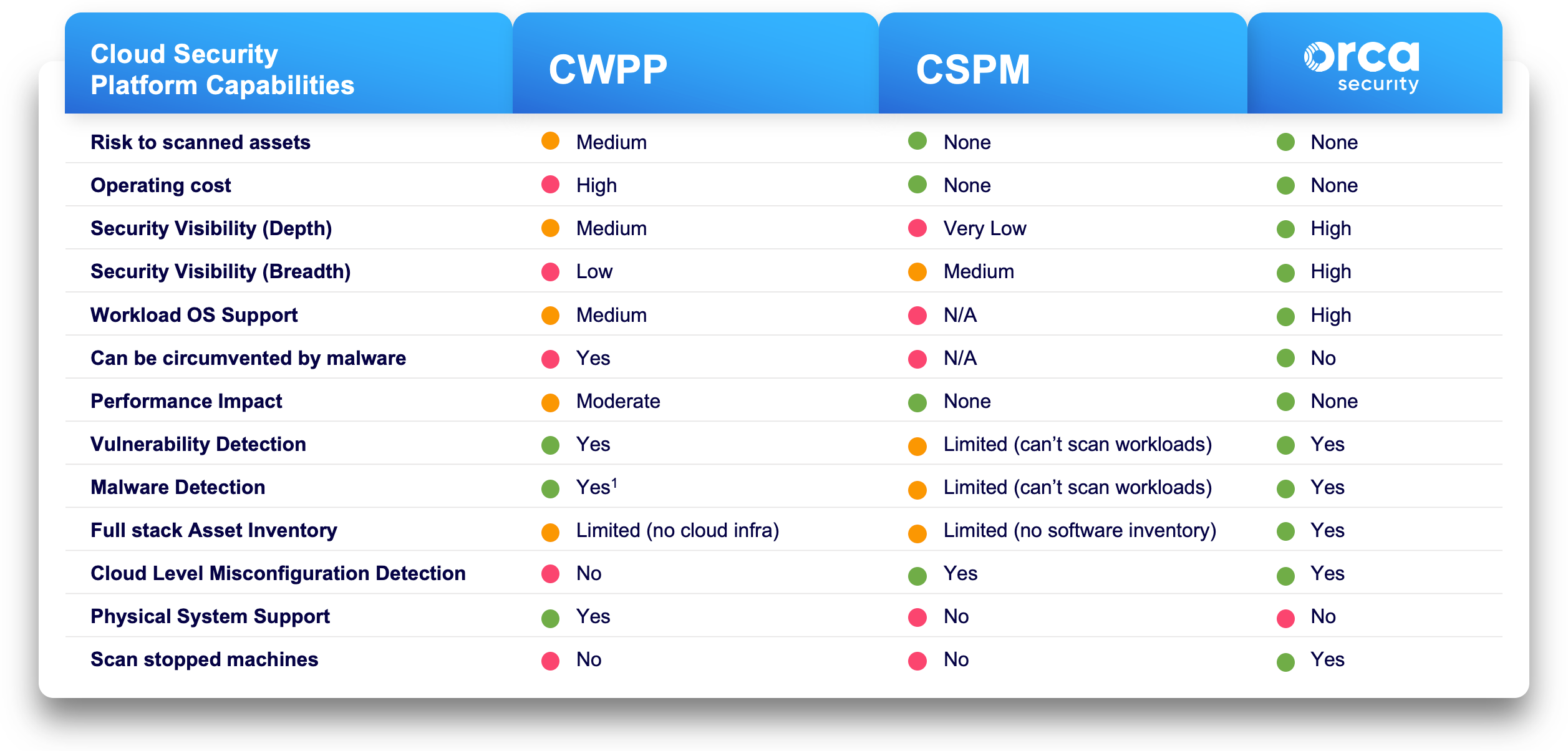
Orca Brings Together the Best of CSPM and CWPP without the Drawbacks of Either
As public cloud offerings evolve, protecting the cloud environment grows increasingly challenging for enterprises. We can’t depend on friction-inducing technologies from the ’90s anymore that frankly didn’t work back then and certainly don’t work today. The existing cloud security solution categories–vulnerability management, cloud security posture management (CSPM), and cloud workload protection platforms (CWPP)–add to the challenge as they fall short of delivering a complete solution.
Securing your public cloud estate requires full-stack visibility based on a unified data model that spans cloud infrastructure, as well as application and data layers. At Orca, we’ve put in the effort to rethink cloud security to provide a platform that meets enterprise security needs by design rather than through acquisitions and integrations.
The table below demonstrates how Orca’s ability to combine core CSPM with agentless Cloud Workload Protection Platform (CWPP) capabilities can provide visibility and operational efficiency not possible with siloed solutions.
“Cloud-native application protection platform (CNAPP) provides more than CWPP-CSPM convergence: There are two important drivers for CNAPP. Firstly, CWPP vendors are looking to posture to provide workload context. Secondly, CSPMs are challenged to provide more and more visibility while “drilling down” into the workload. CNAPP integrates CSPM and CWPP to offer both, and potentially augments them with additional cloud security capabilities.”
– Gartner, Inc., How to Protect Your Clouds with CSPM, CWPP, CNAPP, and CASB, 2021, Richard Bartley, May 6, 2021
Cool Customers: Trusted by Innovative Enterprises Across the Globe
Call us whatever acronym you like, our customers choose Orca Security to:
- Avoid the cost and complexity of multiple cloud security tools
- Realize instant time-to-value
- Focus on the 1% of alerts that matter most
- Simplify security and compliance operations
- Deny threat actors any foothold in their public cloud estate
- Give even junior team members cloud security superpowers
“This is top-notch and pure magic.”Calib Sima VP of Information Security, Databricks
“I’ve never seen adoption like this.”Jack Roehrig CISO, Turnitin
“SideScanning doesn’t impact anything our developers are doing.”Thomas Hill CISO, Live Oak Bank
“I’ve never seen anything like Orca before. This product is a gem.” Morey Haber CTO | CISO, BeyondTrust
“We now have a single tool that does it all.” Shahar Maor CISO, Fiverr
“Actionable results—without having to sift through the noise.” Aaron Brown Senior Cloud Security Engineer, Sisense
We’re excited to be recognized as a 2021 Gartner Cool Vendor and invite you to download their recent research on the emerging CNAPP category: “Innovation Insight for Cloud-Native Application Platforms.”
Learn More About Orca Security
Orca Security provides instant-on security and compliance for AWS, Azure, and GCP - without the gaps in coverage, alert fatigue, and operational costs of agents or sidecars. View the Orca demo to find out more.
[1]Gartner, Inc., Cool Vendors in Cloud Security Posture Management, Tom Croll, Neil MacDonald, Mark Wah, Prateek Bhajanka, June 9, 2021
Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose. GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.
The GARTNER COOL VENDOR badge is a trademark and service mark of Gartner, Inc. and/or its affiliates and is used herein with permission. All rights reserved. Gartner does not endorse any vendor, product or service depicted in its research publications and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s Research & Advisory organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.
This graphic was published by Gartner, Inc. as part of a larger research document and should be evaluated in the context of the entire document. The Gartner document is available upon request from Orca Security