Table of contents
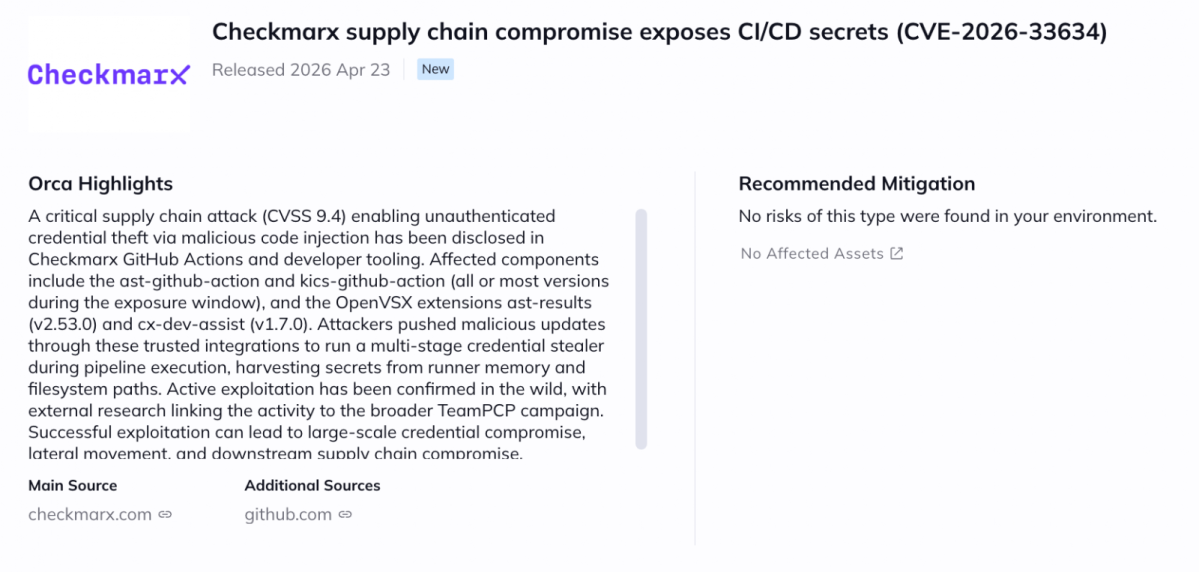
A critical supply chain vulnerability (CVE-2026-33634, CVSS 9.4) was disclosed affecting Checkmarx GitHub Actions and developer tooling, allowing attackers to steal sensitive credentials from CI/CD environments via poisoned workflows and malicious extensions. Due to the potential for large-scale credential compromise and lateral movement across pipelines, immediate remediation is required.
What is the Checkmarx Supply Chain Compromise?
The issue originates from compromised CI/CD workflows and developer artifacts, where attackers leveraged stolen credentials and malicious code injection to execute a multi-stage credential stealer during pipeline execution. By sending malicious updates through trusted GitHub Actions and OpenVSX extensions, attackers can harvest secrets from runner memory and filesystem paths, potentially enabling downstream supply chain compromise and further propagation across repositories and environments. No authentication is required to exploit this issue in affected pipelines.
The following components are affected: Checkmarx ast-github-action and kics-github-action (all or most versions during the exposure window), along with OpenVSX extensions ast-results v2.53.0 and cx-dev-assist v1.7.0. These components are widely used in CI/CD pipelines and developer environments, including GitHub-based workflows, particularly when automated security scanning is enabled. Other frameworks and services relying on these integrations may also be impacted.
Impact of the TeamPCP Campaign: Credential Theft and Lateral Movement
At the time of writing, proof-of-concept exploitation is publicly available as part of broader research into the TeamPCP campaign, and active exploitation has been confirmed in the wild across multiple ecosystems. Regardless, the severity and ease of exploitation make this vulnerability high risk, especially in internet-facing CI/CD environments.
Successful exploitation could allow attackers to exfiltrate cloud credentials and tokens, move laterally across repositories and infrastructure, and potentially gain full control over build pipelines and production environments, leading to service disruption, data exposure, or full infrastructure compromise.
Mitigation Recommendations
Users should immediately:
- Upgrade to safe versions and remove malicious artifacts
- Ensure only trusted releases are used and credentials are rotated.
Environments that previously applied partial mitigations should still upgrade and rotate secrets, as earlier remediation efforts may not fully address the compromise scope.
How can Orca help?
Orca enables customers to quickly identify assets running vulnerable versions, understand their exposure in context—including internet accessibility, runtime reachability, and asset criticality—and prioritize remediation based on real risk rather than CVSS alone. Orca’s platform highlights affected assets directly in the newItem view, helping security teams focus on the most critical remediation paths first.