The prevalence of migration to the cloud highlights the catch-22 of cybersecurity: the security vs. convenience tradeoff. But it doesn’t have to be this way.
“Houston, We Have an Unmanaged Cloud Problem”
With cloud applications there is no need to worry about planning ahead or setting up servers, networks, and physical infrastructure. Instances are spun up and down in seconds. This very ease of use has led to the unmanaged cloud explosion, where security protocols are often ignored, and IT and security teams have no way of knowing what is going on in their cloud environment, including how many tools are running on how many instances.
Traditional security procedures and safeguards are simply leapfrogged and are no longer effective. This is largely due to the fact that processes are not in tune with the agility and advantages of working on the cloud and therefore end-users inevitably gravitate towards convenience over security.
According to the Ponemon Institute, 47% of lines of business respondents admit they select and use cloud applications without permission from IT. And because business users don’t require IT involvement to spin up new applications, often, they forget to notify the technical personnel of new cloud apps they are using.
Shared responsibility model: read the fine print
As a user of public cloud, it is easy to get used to the fact that everything is taken care of.
You don’t need to worry about power, cooling, physical storage, or setting up network infrastructures. It is easy to get complacent and assume that the cloud service provider is responsible for your asset security too.
But the cloud is built on a “shared responsibility model,” which means that the cloud service providers only protect their platforms and infrastructure, not your data. Major cloud platforms, including AWS, stress that the users are responsible for security in the cloud, including their data. Cloud Service Provider, or CSP, is responsible for protecting the infrastructure that includes the hardware, software, networking, and facilities that run its cloud services.
This means that both providers and customers are sharing the responsibility for security, and there are relatively few places where that responsibility overlaps. A large number of cloud security problems sprout from a misunderstanding of where the users’ responsibility lies, and where the providers’ begins.
CSP is only responsible for securing its own applications, but if you are running your own apps in the cloud, you are responsible for their security. Because an application’s vulnerabilities are independent of the infrastructure it runs on, those vulnerabilities cannot be “configured away” in the cloud, rather you’ll have to conduct application security testing on your cloud apps.
For example, Amazon EC2 is categorized as IaaS, and requires the customer to manage the end-to-end security of the guest OS. That includes updates and patching, configuring firewalls, as well as the responsibility to secure all the apps and utilities installed.
For other services, such as Amazon S3 and Amazon DynamoDB, where AWS operates the infrastructure layer, the operating system, and platforms, while customers access the endpoints to store and retrieve data, the responsibility shifts somewhat. This means that Amazon is responsible for securing the infrastructure, the OS and the platforms, while the customers are responsible for managing their data (including encryption options), classifying their assets, and using IAM tools to apply the appropriate permissions.
All in all, it’s up to you to secure your business. The brunt of responsibility for your data, applications and operating system, lies with you, not the cloud service provider. Here’s how you can play an active role in your cloud deployment, making sure that your CSP’s security controls are configured properly, and take charge of your security to ensure your data stays protected:
4 Tips to Manage your Cloud Sprawl
1. Set up approval protocols
Bringing back ‘some’ control to the IT security team means ensuring that business users are getting approval to select and use cloud applications. This will need to be a quick and painless process to succeed and keep up with the agility of the cloud.
However, establishing and maintaining approval and reviewing protocols is an essential first step in reigning in the out-of-control cloud deployments.
2. Conduct internal audits
According to Ponemon, only 30% of organizations conduct regular security audits for cloud apps before actual deployment, and in many cases, audits don’t happen at all.
Security audits should be a compulsory first step for all cloud deployments organization-wide. Security teams must be strict to ensure these procedures are carried out without exception.
As we’ve already established, security and IT teams are often left in the dark. The one department that has full visibility into what is going on in your cloud is the accounting team. Handling your organization’s bills means that they have detailed access to corporate credit cards and accounts. That is why security audits are made easier by regularly exchanging information with your accounting department.
3. Implement 2FA and MFA to secure apps and data
99% of cloud misconfigurations remain undetected, making cloud services an easy and lucrative target for cybercriminals. Today, no password is safe, including the ones your employees are using to access their cloud accounts.
With breaches, data theft, malware, phishing, and account takeover on the rise, you can no longer rely on passwords alone to protect your cloud applications. Setting up 2FA and MFA is best practice for a reason. Make sure to enable it on all of your organization’s apps.
4. Incorporate Full Stack Visibility into your Cloud Security initiative
Only 23% of the 1,670 IT security practitioners surveyed by Ponemon claimed to have 360-degree visibility into their cloud environments.
At the same time, 69% rate the level of risk associated with a lack of visibility into cloud applications and platforms as very high. Limited visibility is the number one culprit of poor security in cloud environments. It’s the assets that you don’t see that are likely to be responsible for your next breach.
That is why gaining visibility into cloud environments is the first and necessary step for protecting them. To achieve a 360-degree view, make sure you have the right tools in your toolkit.
Bringing Full-Stack Visibility into the Cloud
The agility, scalability, and convenience benefits of the cloud far exceed its drawbacks. But like most things in life, the cloud also needs to be managed well. When left to their own devices, your employees will always choose convenience, leaving your IT and security teams out of the loop.
Implement these four tips into your everyday security plan to conquer the side effects of the unmanaged cloud explosion.
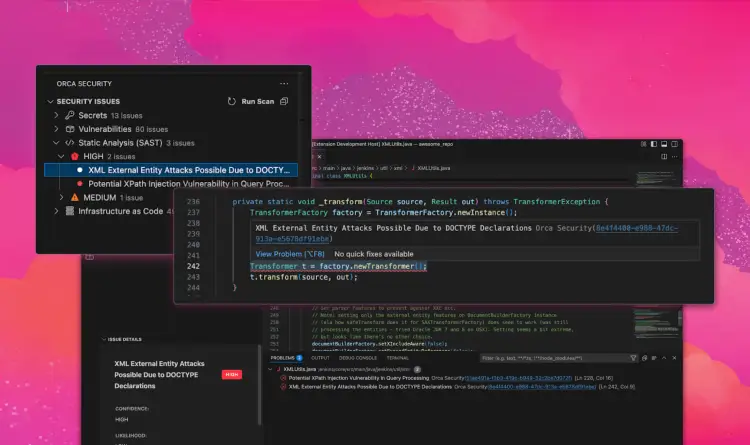
Ready for comprehensive full-stack visibility into your entire cloud infrastructure and assets in a fraction of the time and cost? See Orca in action.