Table of contents
Key Findings
- The volume of disclosed vulnerabilities continues to accelerate, with more than 48,000 new CVEs published in 2025, making prioritization and remediation the primary AppSec challenge.
- High false-positive rates and duplicate findings slow remediation and erode developer trust, reinforcing the need for context-driven validation.
- Orca launches new Code Reachability, enabling teams to identify which vulnerable functions are actually executed by the application and prioritize remediation on real risk.
- Orca launches AppSec Triage Agent, which uses code context to verify whether high- and critical-priority SAST findings are true positives or false positives.
- Orca introduces new AppSec Dashboard that helps organizations track application security program performance, prioritize high-impact risks across the SDLC, and identify systemic development issues driving recurring exposure.
- Together, these capabilities give organizations complete visibility into their application security program, reduce backlog, and accelerate time to remediation, allowing teams to measure risk reduction based on what is eliminated in production.
Introduction
Application security teams are managing more vulnerabilities than they can realistically remediate. In 2025 alone, more than 48,000 new CVEs were published, the highest annual total on record, and most organizations now track thousands of findings across code repositories and containers. A large majority of critical vulnerabilities remain open, not because they are unknown, but because teams lack the context needed to prioritize and act.
Modern applications are built on layers of open source dependencies, automated pipelines, and distributed services, and the rapid adoption of AI is accelerating this growth. Static analysis, software composition analysis, and secrets scanning have dramatically increased visibility into application risk, but they have also produced a volume of findings that far exceeds what teams can address within normal development cycles.
The challenge in AppSec is no longer detection. It is deciding what matters and fixing it before it is exploited.
Why Traditional AppSec Approaches Break Down
CVSS severity is a common way to understand the potential impact of a vulnerability, and while it is a good starting point, alone it does not show whether vulnerable code is actually executed by the application or used within real code paths. In modern environments, severity alone cannot distinguish between theoretical risk and issues that can be exercised in practice.
Without proper context and ownership mapping, teams are forced into one of two ineffective approaches:
- Fix everything, which causes remediation efforts to stall under the volume of findings
- Defer remediation, which leaves exploitable risk unresolved and introduces unknown exposure
Prioritization also breaks down at the workflow level. Findings are generated across multiple tools and repositories without being mapped to the code that invokes the vulnerable function or to the team responsible for fixing it. Security teams must manually correlate results, triage issues, and create tickets, while developers often receive findings that lack the context needed to validate risk or take action on.
Even when remediation workflows improve, many organizations still lack a centralized way to understand how application risk trends over time, where risk is repeatedly being introduced, or whether remediation targets are being met.
This is why remediation, not discovery, has become the primary bottleneck in many application security programs.
Focusing on What Actually Runs (Code Reachability)
Orca’s Code Reachability identifies which vulnerable functions are actually executed by your application, so teams can focus remediation on real, actionable risk.
Code reachability addresses one of the most persistent sources of noise in application security: vulnerabilities in code that is never executed. By analyzing application call paths and dependency usage, code reachability determines whether a vulnerable function is actually invoked by the application, filtering out unused libraries, parts of the program that are never executed with the application runs, and purely theoretical exposure.
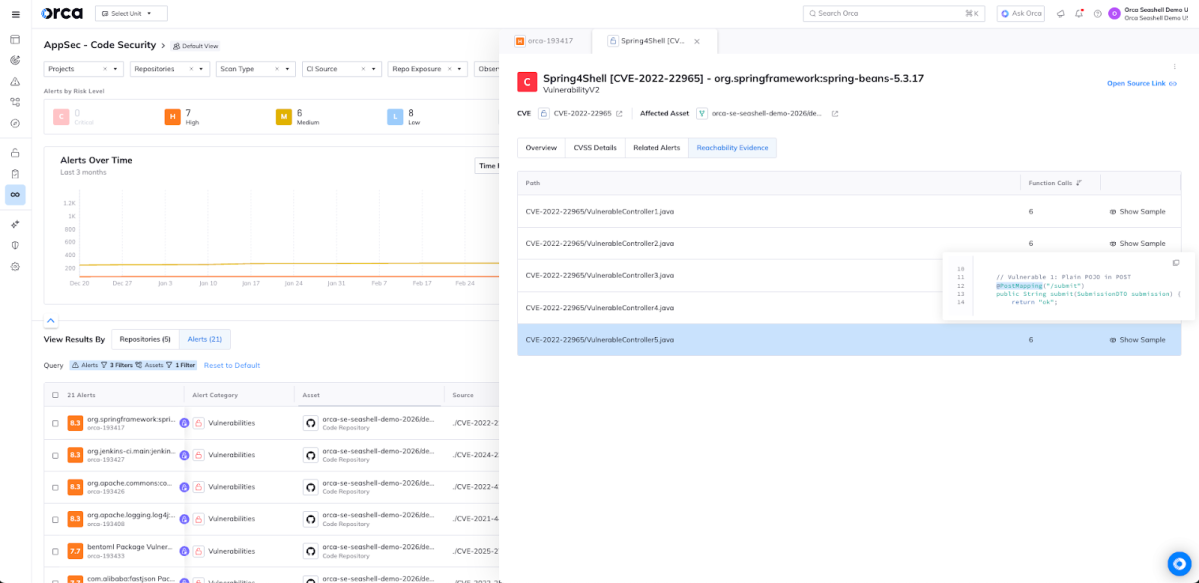
This reduces the vulnerability set to what can realistically be exercised in production, turning SBOM data into an exploitability signal and giving teams a defensible, behavior-based scope for remediation that reflects how their applications truly run rather than where vulnerable packages happen to exist.
Code reachability is presented as a clear link between vulnerable functions in third-party packages and the first-party code that invokes them. Orca identifies the specific call paths where application code executes a vulnerable method and provides the exact source lines that trigger that execution. This evidence-based approach allows teams to see not just that a vulnerable package exists, but where it is actively used in their codebase, giving developers the precise context needed to validate risk and remediate with confidence.
Orca’s new code reachability is surfaced directly within the Orca platform and developer workflows, including vulnerability views, risk scoring, policies, CLI output, IDE integrations, and pull request experiences. Findings are labeled as ‘Reachable’ when a call to a vulnerable method is detected, or ‘Inconclusive’ when no execution path exists.
Turning Findings into Action (AppSec Triage Agent)
Orca’s AppSec Triage Agent uses code context to validate SAST findings, determining whether they represent true exploitable risk or likely false positives.
Even after reducing the scope, remediation can stall when findings require manual validation, lack clear prioritization, and do not provide enough context to determine impact and next steps. The Orca AppSec Triage Agent addresses this gap by analyzing code context, data flow, and sanitization patterns to verify whether a finding is a true positive or false positive.
Based on this verdict, the platform boosts the risk score of validated true positives and reduces the risk score of likely false positives, helping teams focus attention where it matters most. As a result, security teams move from reviewing fragmented findings to executing clear, workflow-aligned fixes, reducing friction and accelerating time to remediation.
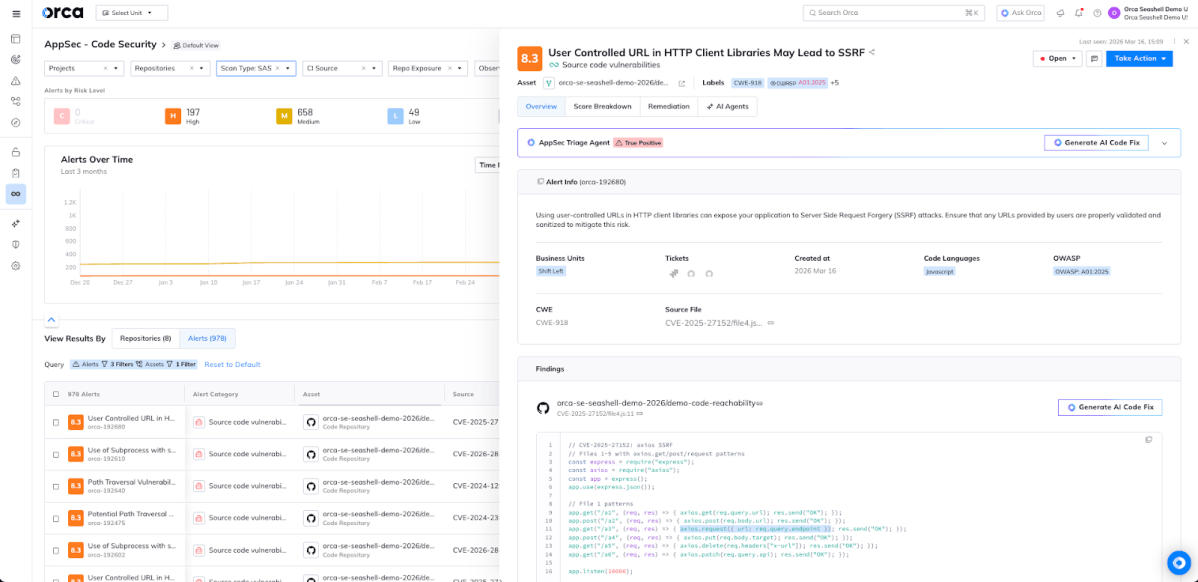
Traditional SAST workflows often create alert fatigue, forcing teams to manually review large volumes of findings to separate true risk from noise. The Orca AppSec Triage Agent applies AI-driven analysis to validate SAST findings by analyzing data flow, sanitization patterns, and code context to help teams quickly distinguish likely false positives from true risk.
By surfacing confidence levels, providing explainable reasoning, and adjusting risk priority based on validation, the platform allows teams to focus their attention on high-confidence issues while reducing unnecessary triage effort.
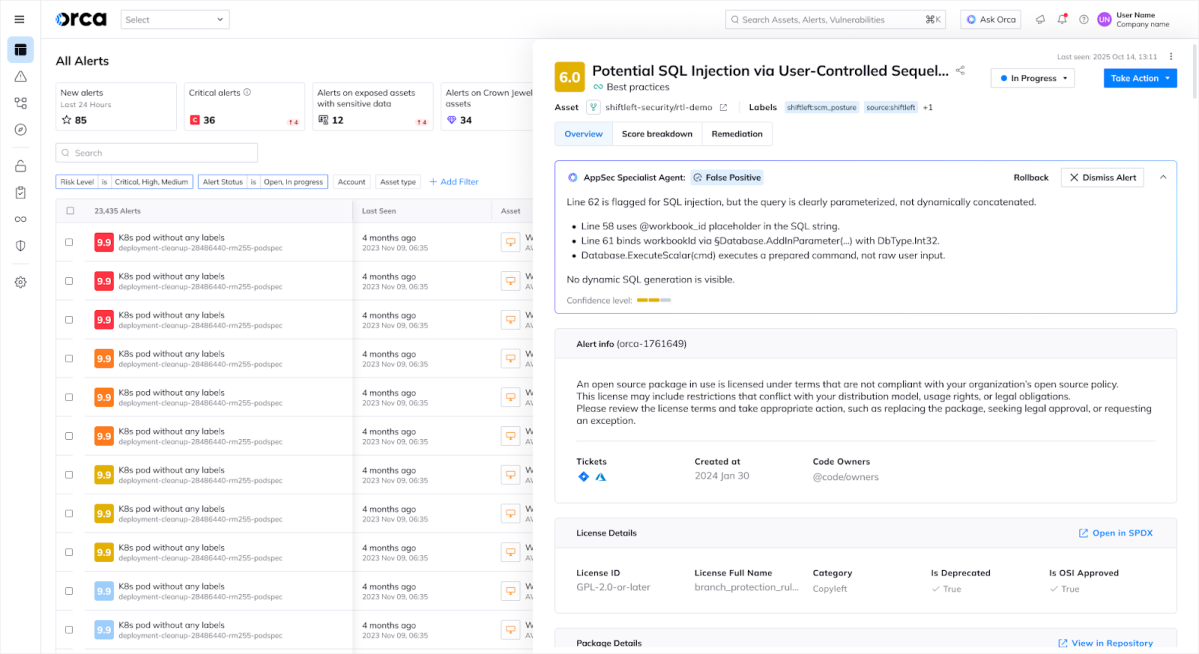
Users retain full control and can review the AI reasoning, override the agent’s verdict, or roll back an automatic dismissal if they disagree with the conclusion, ensuring transparency while streamlining remediation.
Visualizing Application Risk (AppSec Dashboard)
Even with better prioritization and validation, application security programs still struggle to understand how risk evolves across repositories, teams, and development cycles. Security leaders often lack a centralized way to track remediation progress, identify recurring development issues, and ensure teams are focusing on the risks that matter most.
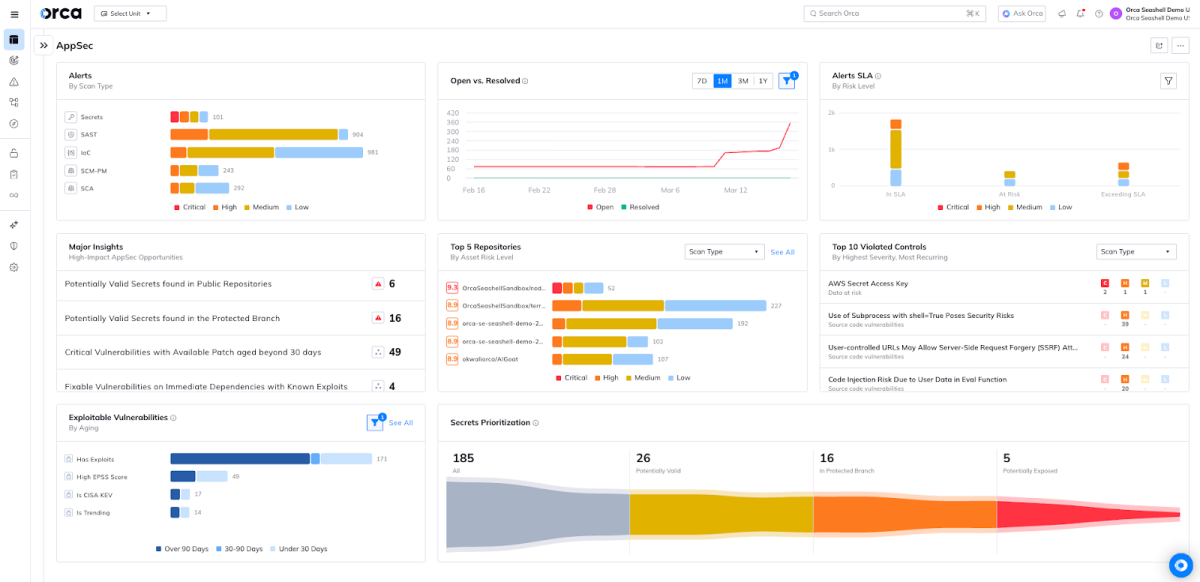
The Orca AppSec Dashboard provides a centralized view of application security posture across the software delivery lifecycle, helping organizations track program performance, prioritize high-impact risks, and identify systemic issues driving exposure.
Customizable widgets allow teams to build dashboards around the metrics that matter most to their program, such as remediation SLAs, vulnerability trends, and security KPIs, giving security and development teams a view tailored to how they work. This improves operational efficiency and helps teams measure progress against their security goals.
The dashboard also surfaces high-impact risks across the SDLC, such as exposed valid secrets or aging dependency vulnerabilities tied to known exploited vulnerabilities, ensuring the issues most likely to introduce real risk are immediately visible and prioritized.
Finally, insights such as Top Violated Controls and Top Risky Repositories help organizations identify recurring development patterns that introduce exposure, allowing teams to address systemic issues at the source rather than repeatedly triaging individual findings.
Reducing Risk at Scale
By combining code reachability with AI-driven triage, organizations can move from vulnerability discovery to a prioritized view of executable risk. Vulnerable components are first identified across code and dependencies, and code reachability determines which vulnerable functions are actually executed by the application, helping teams focus on third-party vulnerabilities that represent real runtime exposure.
In parallel, Orca’s AppSec Triage Agent analyzes SAST findings using code context to determine whether they are true positives or likely false positives. Based on this verdict, the platform automatically boosts the risk score of validated true positives and lowers the risk score of likely false positives, helping teams focus on the issues that require action while reducing unnecessary investigation.
Together, these capabilities enable organizations to cut through noise across both dependency and code-level findings, allowing security and development teams to focus remediation on the vulnerabilities that are most likely to introduce risk in production.
The AppSec Dashboard brings these insights together into a unified operational view, allowing organizations to track remediation performance, identify systemic weaknesses across repositories, and continuously measure progress in reducing exploitable risk.
Application security programs succeed when teams can consistently reduce real risk, not simply generate more findings. As AI accelerates code production and vulnerability growth, organizations need a remediation model that cuts through noise and directs teams toward the risks that actually matter.
With validated findings, reachability context, and centralized AppSec insights, organizations can reduce vulnerability backlogs, accelerate remediation, and measure progress based on risk that is truly eliminated from production.
Command Your Cloud with Orca
Orca offers a unified and comprehensive cloud security platform that identifies, prioritizes, and remediates security risks and compliance issues across AWS, Azure, Google Cloud, Oracle Cloud, Alibaba Cloud, and Kubernetes. The Orca Cloud Security Platform leverages Orca’s patented SideScanning™ technology to provide complete coverage and comprehensive risk detection.
Learn More
Interested in seeing how the Orca Platform can help you command your cloud? Schedule a personalized 1:1 demo.