What is PCI? What are the difficulties in achieving PCI compliance? What are the repercussions of not attaining PCI?
The Payment Card Industry Data Security Standard (PCI-DSS) is a proprietary standard mandated by Visa, MasterCard, American Express, Discover, and JCB. Any organization or merchant handling credit, debit, or prepaid cards branded by one of these companies is subject to its regulation. PCI compliance is not easy—even for companies having the best of intentions. According to Verizon’s 2015 PCI Compliance Report, 80 percent of organizations attempting to achieve certification fail their interim PCI compliance assessment. Even when they’re able to achieve it, only 29 percent manage to remain fully compliant for an entire year afterward.
When non-compliant organizations suffer a data breach, credit card companies and banks often impose heavy-handed contractual requirements upon them. These often include a mandatory investigation by a forensic investigator employed by the credit card companies, along with noncompliance fees that often begin at $100,000 or more.
What do I need to show to attain PCI compliance in the cloud?
Overall, there are 12 requirements for PCI-DSS and while the cloud mandates a shared-responsibility model with your cloud service provider, the burden of proving compliance to auditors still falls on the organization.
The following are the most essential requirements:
Requirement 1 – Installing and maintaining a firewall
PCI requires a firewall to protect cardholder data. It must be configured in such a way to restrict connections from untrusted networks and prohibit direct public access from the internet.
In the on-prem world the only way to solve this was to check firewall appliances for each network. But in the cloud, this can be done using cloud vendor supplied access control limits, such as security groups that can be shown to auditors using the native management console or third-party tools
Requirement 2 – Do not use vendor-supplied defaults for system passwords and other security parameters
PCI requires changing vendor-supplied defaults and removing or disabling unnecessary default accounts before installing a system on the network.
To do this, one must access each and every resource to manually check if defaults are still configured. There are some agents that offer this capability, but they require manual installation and often don’t support all resources.
Requirement 3 – Protect stored cardholder data
PCI mandates not storing sensitive authentication data after authorization (even if the data is encrypted). However, it is permissible for issuers and companies that support issuing services to store sensitive authentication data if 1) there is a business justification, and 2) the data is stored securely.
To confirm sensitive information is securely stored you must check every system where PCI data might reside. This usually relies on intrinsic staff knowledge of all possible locations where PCI data lives. That said, it’s all too easy to miss such an insecurely stored file, especially if you have no knowledge of its creation to begin with.
Requirement 5 – Use and regularly update anti-virus software or programs
PCI requires daily malware scanning using up-to-date signatures. Malware scanners must be configured in a way that they cannot be disabled or altered by a user. (PCI 5.1–5.3)
In the on-prem world, the typical (and only) way to handle this is to deploy an antivirus agent on each and every machine. In the cloud, these legacy tools simply performed a “lift and shift;” that is, you are still required to deploy an antivirus agent on each and every machine in your cloud environment.
Requirement 6 – Develop and maintain secure systems and applications
PCI requires continuous vulnerability management and scanning to be performed across all resources. You must establish a process to identify security vulnerabilities, using reputable outside sources for vulnerability information, and assign a risk ranking (e.g., high, medium, or low) to newly discovered security vulnerabilities. (PCI 6.1)
In the on-prem world, the typical (and only) way to handle this is to deploy a vulnerability management agent and/or scanner on each and every machine. The same tedious and error-prone process exists for the cloud.
Requirement 10 – Track and monitor all access to network resources and cardholder data
PCI requires ensuring that security policies and operational procedures for monitoring all access to network resources and cardholder data are documented, in use, and known to all affected parties.
In the on-prem world, this is performed by analyzing and sniffing network traffic. In the cloud this is possible by examining flow and audit logs.
Requirement 11 – Regularly test security systems and processes along with file-integrity monitoring
PCI requires continuous vulnerability scans to assess all systems for risks or threats. It calls for deploying a change-detection mechanism (e.g., file-integrity monitoring tools) that alerts personnel to unauthorized modifications (including changes, additions, and deletions) of critical system files, configuration files, or content files. Such detection software is to be configured to perform critical file comparisons at least weekly. (PCI 11.5)
In the on-prem world, this is only possible through file integrity monitoring (FIM) agents that sometimes come bundled with vulnerability management agent solutions. In the cloud, some providers natively offer this ability, although it’s often limited regarding which assets they can cover.
There is a better way—you can get it ALL in an agentless fashion in minutes
Extensive requirements
PCI DSS requirements are extensive, as you can see. To reach them, organizations must rely on deploying agents on every workload. This is because they must have the following capabilities: vulnerability management, anti-malware, and file integrity monitoring.
At least that’s the way it was before Orca was invented.
From a tooling perspective, before Orca you required at least two tools to achieve PCI compliance—a vulnerability management agent and an anti-malware agent. The downside is that agents result in non-trivial performance degradation and extremely high cost of ownership. And they’re a management nightmare associated with ensuring that workload agents are universally installed across your entire cloud estate. In the public cloud, this is how workloads go unnoticed and become subsequently unmanaged over time.
Assures total, verifiable coverage the easy way
Orca is a next-generation, comprehensive solution for providing full stack, context-aware visibility for cloud assets. Unlike agents that require painstaking, per-asset integration, Orca is agentless—it requires no individual installation or “calls to home,” and it never misses an asset.
Orca’s deep cloud asset inspection—afforded by its patent-pending SideScanning™—identifies vulnerabilities, malware, misconfigurations, secret keys, weak passwords, lateral movement risk, and high-risk data such as PII. Orca’s SideScanning guarantees our customers full coverage and eliminates the undesired consequences of missed assets.
Non-workload requirements
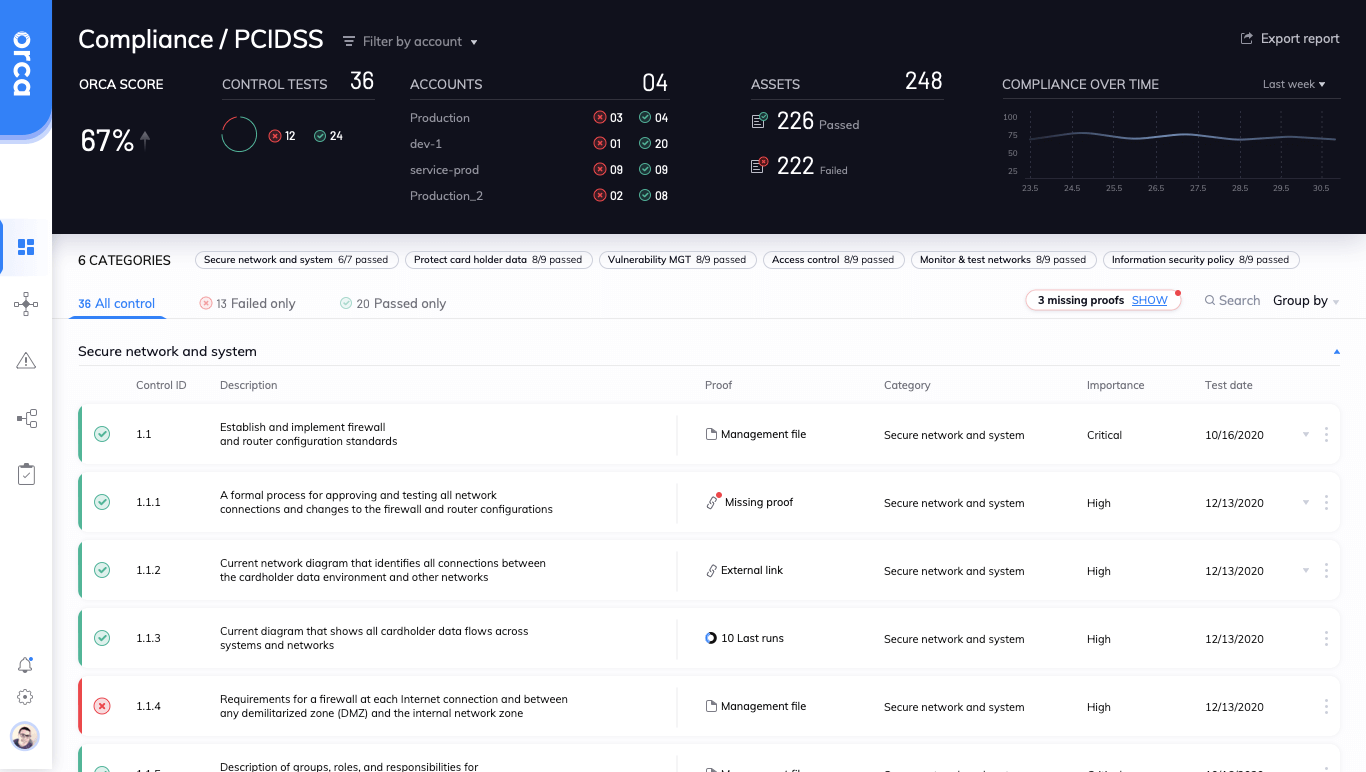
At this point you may be wondering why we haven’t touched on PCI non-workload requirements. These are optional, as no tools are required. Yet from its console, Orca helps demonstrate that you’re compliant with requisite cloud configurations. This is possible because Orca scans both the cloud control and workload plane of your cloud environment. In this way it provides full-stack cloud security visibility along with full coverage for critical compliance frameworks such as PCI. This set of compliance tests Orca provides relate to cloud provider features such as logging, password policy, MFA, encryption key rotation, and more.
For example:
PCI DSS Section 10.2: Implement automated audit trails for all system components
to reconstruct all actions taken by any individual with root or administrative privileges.
PCI DSS Section 8.2.3: Passwords/phrases must meet the following:
- Require a minimum length of at least seven characters.
- Contain both numeric and alphabetic characters.
Single tool does it all
As you can see, Orca covers all PCI requirements, providing coverage for all of your cloud resources, storage, and databases with a purely cloud-native, agentless approach—and all through a single tool. The benefits of choosing Orca vs. a legacy solution are immense, but to summarize:
- 100% coverage across your entire cloud infrastructure without agents
- Takes but a few minutes to set up
- Has zero performance impact on workloads
- Maps to critical compliance frameworks, such as CIS, PCI, and more
If you’re in the market for a security platform that offers end-to-end coverage of your public cloud infrastructure and are governed by data security standards such as PCI, Orca is a match for you.




