‘Our product understands threats and knows how malicious behavior looks, both on the host and in the network. Our automated analysis systems detonate and monitor millions of threats every day. Using that threat behavior information, our machine learning system can automatically build powerful classifiers that identify—with very high accuracy—those network anomalies that characterize lateral movement, leaving behind benign network anomalies that otherwise generate false positives.’
Claim made from a vendor brochure
After an attacker gains a foothold in an organization’s network, they can move laterally to gain deeper access—and subsequently get the data they’re after. The most common ways to perform lateral movement are:
- Reusing privileges of assets they already have a foothold on, such as secrets and credentials that were unwittingly stored on a poorly protected machine. Private keys and passwords (in scripts or in the system’s bash history) are prime examples of things attackers will use.
- Making use of vulnerabilities on internal hosts that are usually maintained far less rigorously than internet-facing ones.
Lateral movement detection vendors boast they can distinguish between legitimate traffic and lateral movements—to a level where they can automatically block such illicit activity. They’ll use terms such as machine learning and AI to make their product sound smart.
Not all lateral movement detection is the same
The reality is that such capabilities are limited. The product might block well-known malware that performs the exact same sequence in any invocation and hence was ‘signed’ by them—making such products glorified, network-based, signature-matching systems. But because AI and machine learning are based on training over some duration, such lateral movement detection can’t distinguish between legitimate traffic and lateral movement at an accuracy level that fully supports run-time prevention.
Moreover, no one knows how such an application works in all scenarios—they haven’t previously seen them in the wild. Are you willing to block traffic just because it hasn’t been witnessed before?
A privileged connection to a server with which an application never communicates could be lateral movement by an attacker. But it could also be a server sending metadata to another during a very infrequent workflow. For the vast majority of such cases, your security team wouldn’t be able to categorize it without doing some research and conferring with DevOps; the vendor-supplied AI tool definitely wouldn’t be able to do this.
Risk of lateral movement is much more straightforward
Managing lateral movement risk is definitely possible by 1) analyzing stored secrets and privileges associated with any given asset and 2) assessing whether they’re overly permissive.
The Orca Security platform scans your environment for secrets and credentials that can be used for lateral movement. This process can be completed prior to an attacker gaining access, thus giving your security team time to analyze and remove such secrets (provided they’re not required in their respective locations)—without relying on some silver bullet to dodge an attacker who has already discovered them.
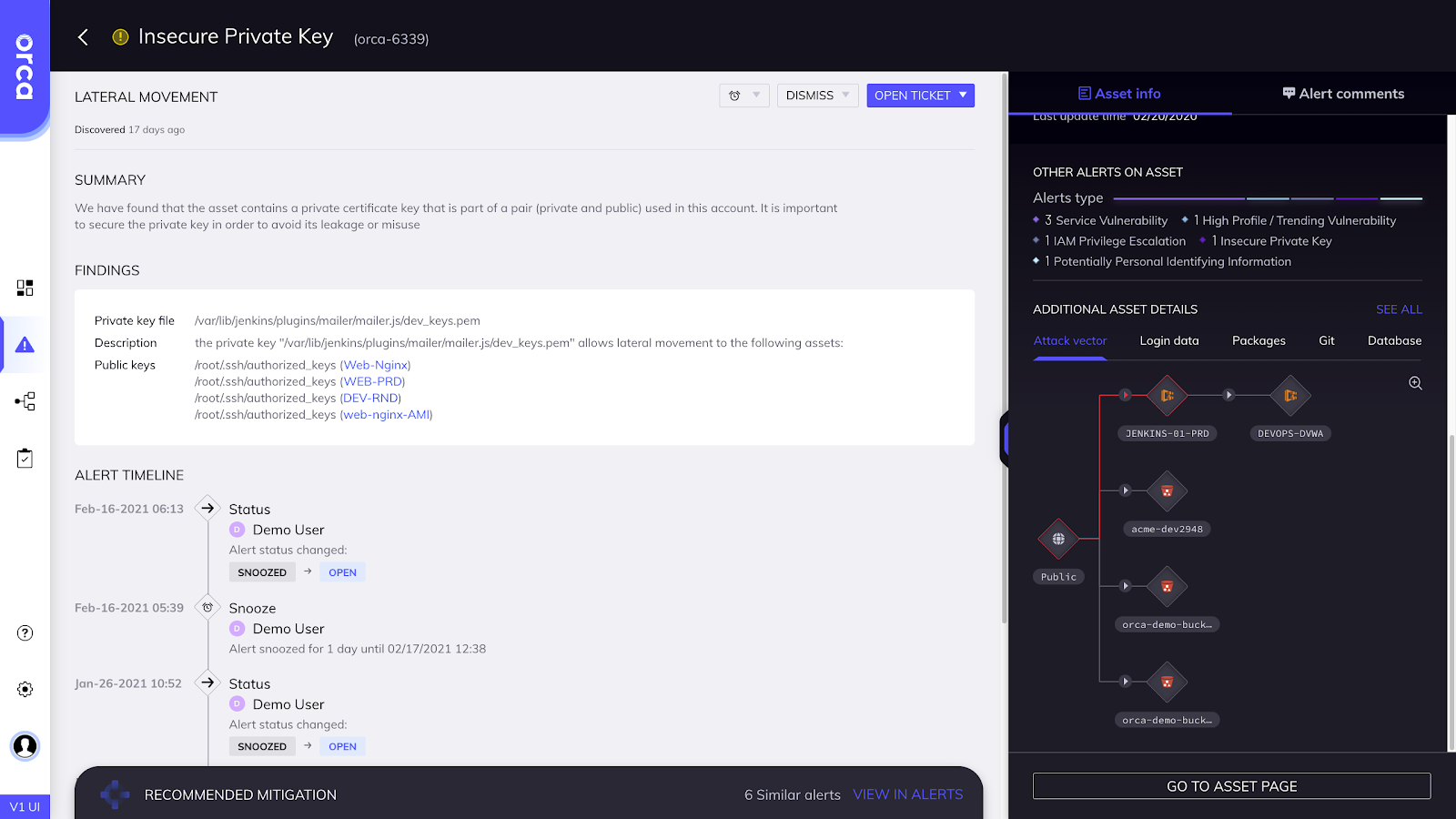
When we look across our customers’ cloud estates, we often find several assets that offer almost unlimited access throughout the organization—a jackpot for potential attackers. It could be a monitoring server, bastion server, or an experiment DevOps is running. Almost always the risk can be dramatically reduced by tightening access—no AI needed.
Orca specializes in AWS Cloud Security, Google Cloud Platform Security, and Microsoft Azure Cloud Security.