As cloud adoption continues to soar, so does the emergence of more cloud service providers, each offering unique value and services to organizations. According to the Orca Security Research Report, 55% of organizations reported using 3 or more cloud service providers. This diverse public cloud approach brings many challenges to security teams responsible for protecting such complex, multi-cloud environments. With each cloud provider having their own set of individual services, understanding how to manage the attack service and configurations of each can be a daunting task, and leave organizations with unforeseen risks.
Delivering a Seamless Cloud Security Platform Experience for Oracle Cloud
Today, we are proud to announce that Orca Security has expanded coverage for Oracle Cloud. The Orca Cloud Security Platform connects to your Oracle Cloud Infrastructure (OCI) environments in minutes with our agentless SideScanning technology to provide you and your teams with complete coverage across all cloud risks – spanning misconfigurations, vulnerabilities, identity risks, data security, and advanced threats. All of this data is populated into our unified data model, which automatically prioritizes the very few attack paths that put the organization in real risk, empowering teams to focus on what actually matters.
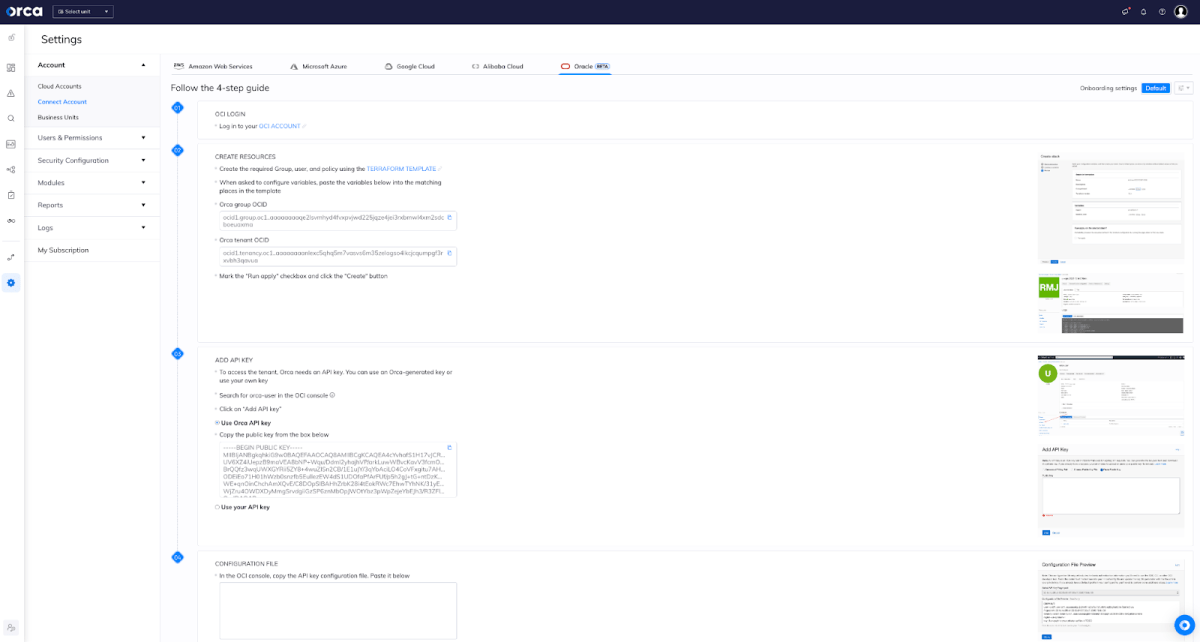
While organizations are faced with the difficulties of managing complex, multi-cloud environments, Orca enables security teams to enforce consistent security practices across AWS, Azure, Google Cloud, Kubernetes, Alibaba Cloud, and now Oracle Cloud from one centralized tool:
- Reducing the organizational friction of managing multiple cloud security tools
- Eliminating alert fatigue
- And make every security practitioner an active defender of the cloud estate.
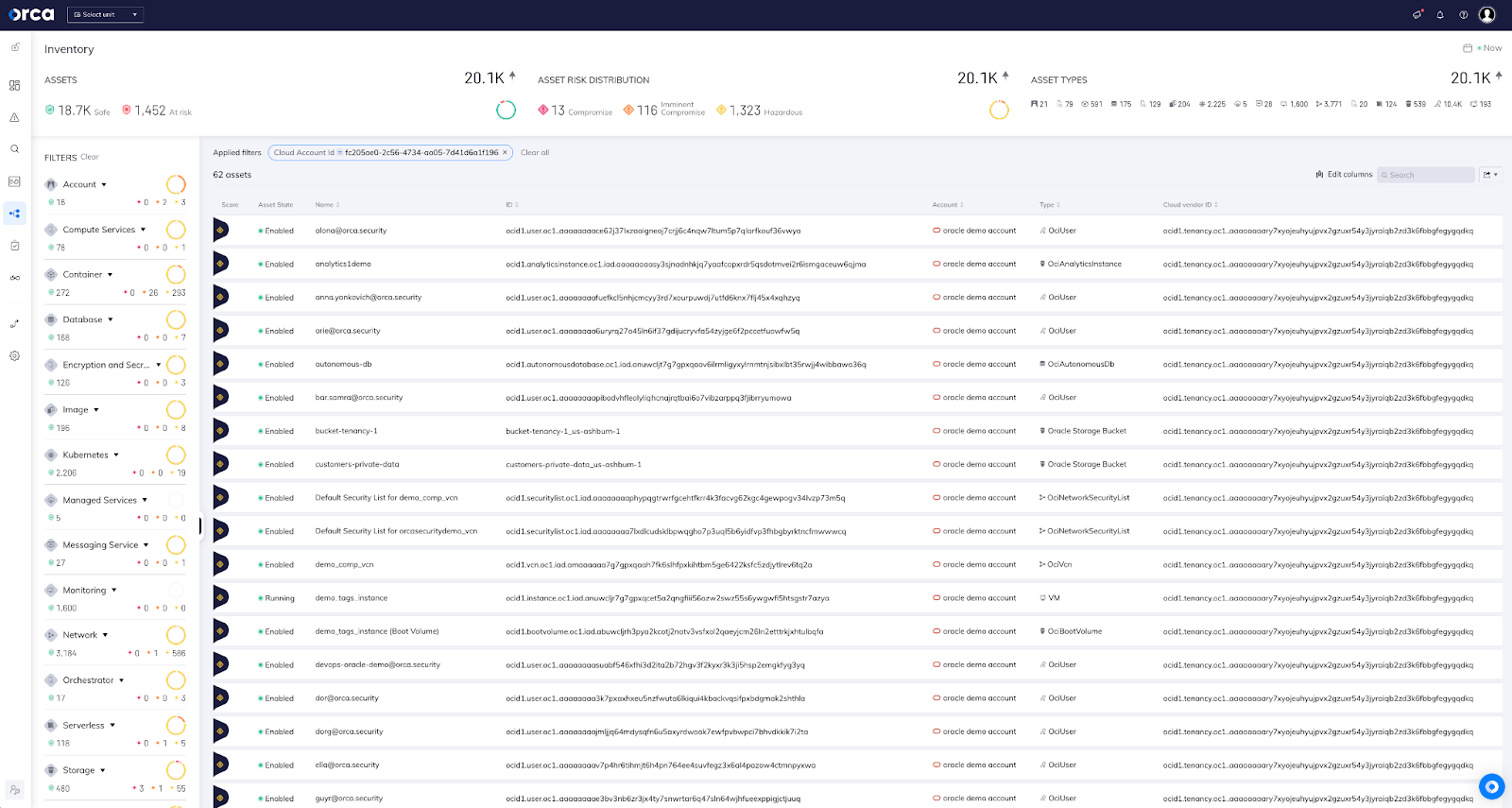
With the support for Oracle Cloud, users can understand their cloud configuration risks and achieve compliance from a centralized Platform. Below, users can seamlessly view all assets on Oracle Cloud, such as compute instances, users, keys, databases, and more alongside their other cloud resources.
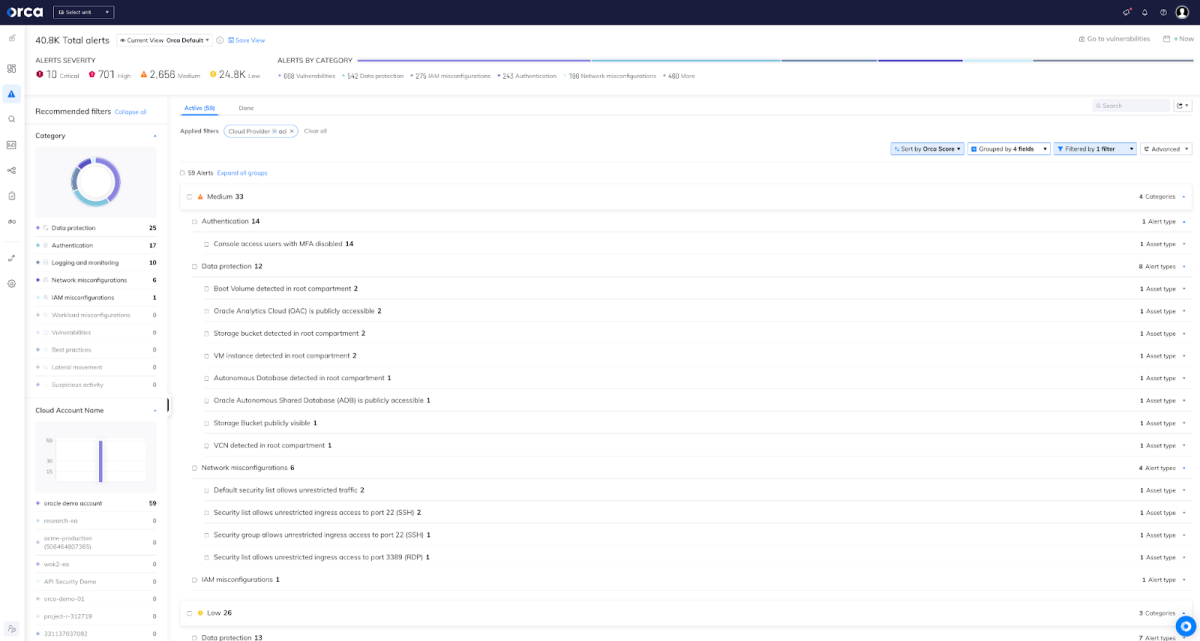
From those discovered assets, the Orca Cloud Security Platform automatically identifies risks affecting those assets, and prioritizes them based on the impact they potentially have on the organization. Orca groups these risks into 3 primary categories (Compromised – highest, Imminent Compromise, and Hazardous – lowest). These risks can be further classified into sub-categories related to Authentication, Data Protection, Network and IAM user Misconfigurations, and more.
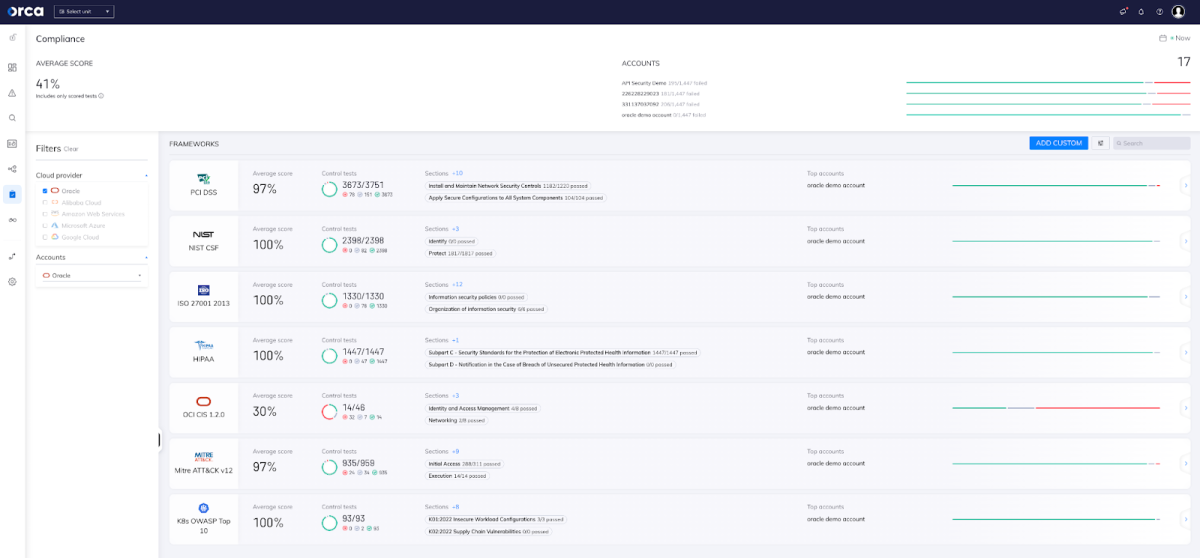
Additionally, all Oracle Cloud data is seamlessly available in the Compliance dashboard of the Orca Platform. This ensures that global organizations can quickly segment data and manage compliance for their cloud estate on Oracle Cloud without manually creating rules or applying policies.
Ensure Your Oracle Cloud Infrastructure is Secure with Orca
Want to learn more about our support for Oracle Cloud? Visit our official Oracle Cloud webpage to learn more.
Want to get more hands on? Sign up for a Free Risk Assessment to see how quickly and easily the Orca Security Platform can help you identify and address risks across your entire cloud estate.





