Abstract: For this Cloud Security Punch-Out we evaluated PAN Prisma Cloud Enterprise Edition as of August 20, 2021. In addition to a full-fledged, updated Prisma Cloud Punch-Out match, we also tested Palo Alto Networks’ claim that one of their main differentiators against Orca Security is their runtime protection. The results were shocking. Bypassing Palo Alto’s runtime protection was as easy as changing file names.
Our Cloud Security Punch-Out series features abbreviated comparisons between Orca Security and some of the world’s largest cloud security solutions. In this match, we go toe-to-toe with Palo Alto Networks (PAN) Prisma Cloud Enterprise Edition. We first compared Orca Security and PAN Prisma Cloud back in September 2020. At that time Palo Alto Networks sent Orca a cease and desist letter. In this current match and as in all Punch-Out comparisons we squared up with regard to ease of deployment, coverage, and the practical ability of alert findings to reduce our overall risk.
Orca Security CEO and co-founder Avi Shua published a blog focused on transparency as a response to PAN’s legal threat. Palo Alto Networks responded by publishing their own blog post (Original removed; linked to archived version) focused on downplaying Orca Security’s agentless strategy and espousing Prisma Cloud’s agent-based runtime protection capabilities. We tested their runtime protection claims and sent our findings to Palo Alto Networks in June of this year. Palo Alto Networks wrote us back dismissing those claims, and Avi responded. We then decided to re-test with a current release of Prisma Cloud Enterprise Edition and publish our findings so you can draw your own conclusions.
Evading Palo Alto Networks Runtime Protections Was as Easy as Changing File Names
As you’ll see in the video above, all we had to do to evade Palo Alto Networks’ runtime protections against crypto miners and tools that enable lateral movement was to rename the files. Malware, exploit, and tor node detection didn’t need to be evaded, because they simply didn’t work in our testing.
We Tested Both Prisma Cloud (Redlock CSPM) and Prisma Cloud Compute (Twistlock CWPP)
PAN Prisma Cloud Enterprise Edition has both a workload and a cloud protection component as part of their offering, and we tested both as part of this match. Prisma Cloud is the cloud security posture manager (CSPM) side of the suite and is an acquisition from Redlock in 2018, while Prisma Cloud Compute is the workload/container security module acquired from Twistlock in 2019.
The Cloud Security Punch-Out Lab Environment
Our test lab was created to model a real-world cloud computing environment only smaller. It’s a single AWS account with a mixture of Linux and Microsoft Windows EC2-based instances, containers, load balancers, and S3 storage buckets. It contains a single VPC having both public and private subnets and an internet gateway provisioned to permit inbound network traffic.
Palo Alto Prisma Cloud Improved Their Visibility for S3 Bucket Misconfigurations, but Missed Larger Risks
The winner was obvious. We saw improvements in PAN Prisma Cloud Enterprise Edition such as more visibility around the public exposure of our S3 storage bucket configurations. But we were once again underwhelmed with the product’s ability to identify the largest risks in our environment. Many alerts that were categorized as high-severity risks seemed less important than others that were categorized as lower risks.
Several Old and Risky Workloads Could Not Support Palo Alto Networks Defender Agents
We had to make significant changes in our network to accommodate Prisma Cloud’s agent-based design, only to discover that the agents did not support several of our workloads.
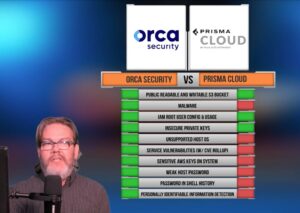
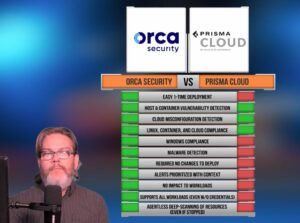
Comparison Table of Palo Alto Networks vs Orca Security
As shown in the video above, Orca beat out Prisma Cloud in a number of areas.
Original Evidence We Sent to Palo Alto Networks
The video above is shortened to make it consumable. In the interests of transparency you can watch the full videos we shared with Palo Alto and correspondence below.
Correspondence
- June 24th letter in which we disclosed to Palo Alto Networks serious vulnerabilities in their runtime protection capabilities
- July 9th letter where Palo Alto Networks initially refutes the claims
- July 13th letter where we responded point by point to Palo Alto Networks’ dismissals
- July 21 in which Palo Alto Networks further dismisses those claims
Full-Length Original Videos
- PAN Prisma Cloud Malware Detection
- PAN Prisma Cloud Lateral Movement Detection
- PAN Prisma Cloud Crypto Miner Detection
- PAN Prisma Cloud Tor Node Communication Detection
- PAN Prisma Cloud Exploit Detection