Weak Host Password
Hazardous (3)
Orca Best Practices
About Weak Host Passwords
Many authentication mechanisms rely on passwords to verify the identity of a user. A password is supposed to be private information, a secret that only you and the system know.
25% of all cyber-breaches are caused by compromised credentials
Passwords have become more prone to compromise than ever before. People are naturally inclined to use personal information in their passwords, like nicknames, names of their partners, children, and pets, birthdays, etc. Since a lot of this information is obtainable through social engineering, it makes the password-hacking process a lot easier and faster.
It’s critical to choose passwords that abide by the recommended complexity and uniqueness requirements, especially when talking about passwords of user accounts on servers and other internal resources.
Cloud Risk Description
Weak passwords of local user accounts of an operating system are highly susceptible to cyberattacks. A compromise could lead to system takeover and data loss.
Brute-force attacks can enable malicious actors to acquire passwords and then gain unauthorized access. During a brute-force attack, a malicious actor repeatedly tries different password combinations, until they find the right one.
Modern computing power allows trying thousands of alphanumeric combinations per second, which often means that if a brute-force attempt runs long enough, the cybercriminal may eventually get a match. If it is a commonly used or default password, they may get a hit much sooner.
How Does Orca help?
Orca employs multiple methods to identify poor password hygiene, including commonly used passwords, complex passwords that are reused across multiple applications and services, and highly secure passwords that have been leaked. Orca ensures password policy settings in your cloud meet industry guidelines around the use of MFA, minimum password length, use of special characters, password age, password reuse, and more.
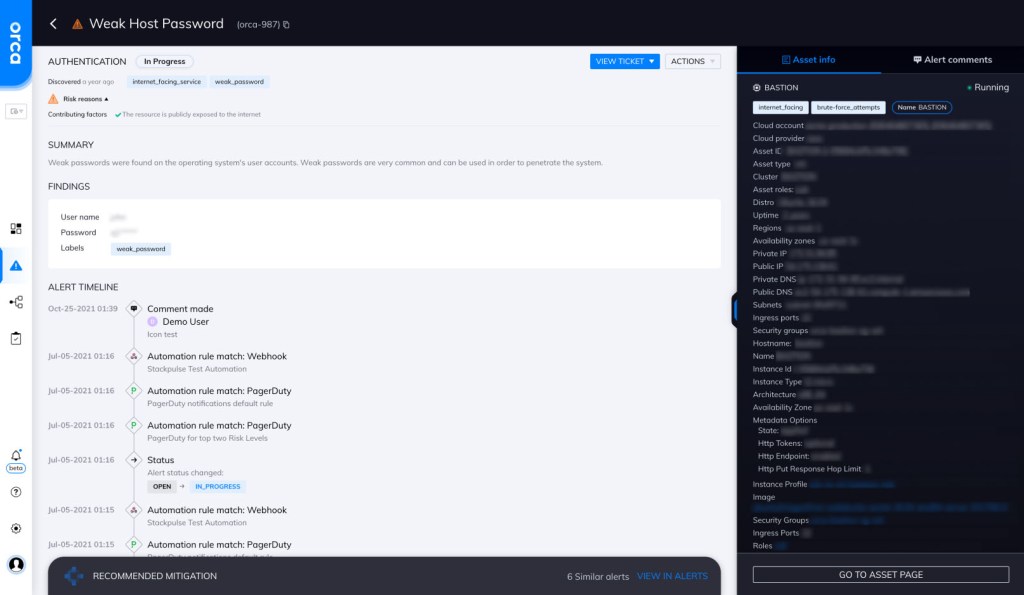
Orca looks for weak host passwords and will alert on this type of issue as shown in the screenshot above.
Recommended Mitigation Strategies
-
Use unique passwords
Encourage employees to use unique passwords for each of their accounts.
-
Set password reset policies
Set a periodic password reset policy that prevents users from reusing older passwords.
-
Limit unsuccessful login attempts
Limit unsuccessful login attempts; i.e., if a user fails to provide the correct password after X attempts, block any subsequent requests from that device/IP/account.
-
Use MFA
Use multi-factor authentication, which can provide an additional layer of security.
-
Enforce password policies
Enforce a strict password selection policy that adheres to the recommended complexity, length, and uniqueness standards.
-
No password sharing
Prohibit employees from sharing passwords.
Useful Links
- Creating a strong password: https://support.google.com/accounts/answer/32040?hl=en
- Password policies: https://blog.devolutions.net/2018/02/top-10-password-policies-and-best-practices-for-system-administrators
- Password encryption: https://www.ibm.com/docs/ssw_ibm_i_73/rzahy/rzahypwdencrypt.htm
- Password hashing: https://www.wired.com/2016/06/hacker-lexicon-password-hashing/
- Storing passwords cheat sheet: https://cheatsheetseries.owasp.org/cheatsheets/Password_Storage_Cheat_Sheet.html
Orca Security, the cloud security innovation leader, provides cloud-wide, workload-deep security and compliance for AWS, Azure, and GCP - without the gaps in coverage, alert fatigue, and operational costs of agents.
