For security teams, the benefits of integrating security scanning and policy enforcement into CI/CD pipelines is obvious. The more we can solve vulnerabilities and misconfigurations early, the more we free security analysts to focus on complex and emergent threats. But, for all the obvious advantages, there are a lot of organizations that haven’t implemented comprehensive shift-left integration.
While the security benefits of a shift-left approach are clear, implementation has traditionally been more of a problem. Command line tools have to be manually inserted into pipelines, requiring unnecessary coordination between security and DevOps teams as well as making it difficult to ensure complete coverage. This also creates separation of duties concerns – security teams should have the control over where policy is enforced and DevOps teams may prefer not to invest in operationalizing security.
The Orca Cloud Security Platform is delivering a better approach, available today. The Orca GitHub App lets security teams centrally deploy and manage shift-left integration of scanning GitHub repositories for vulnerabilities, misconfigurations, and secrets in both application source code and Infrastructure-as-Code (IaC).
Providing a Seamless GitHub Integration
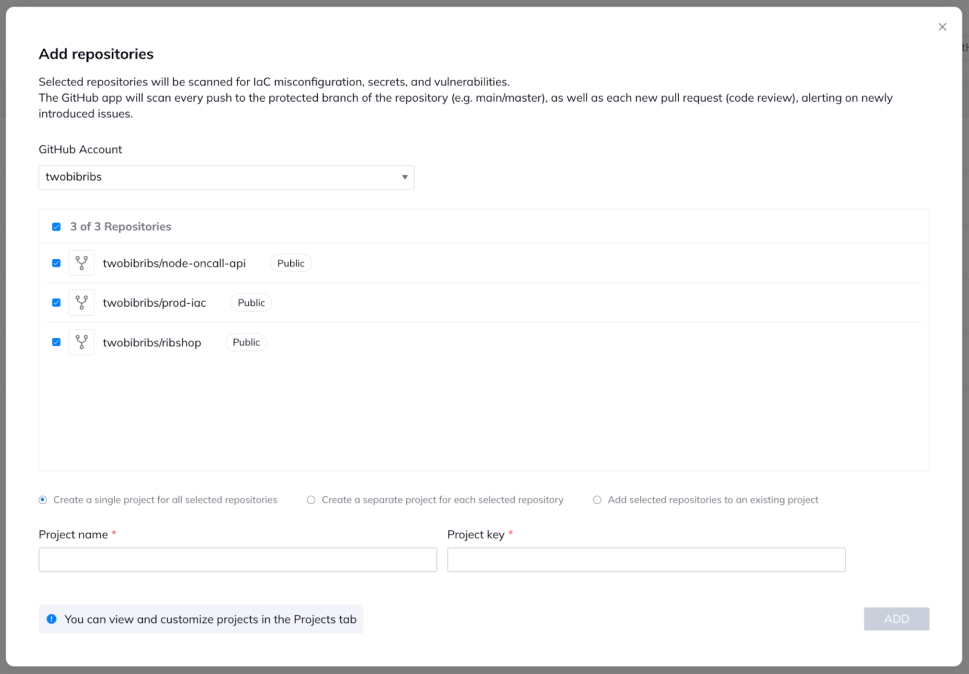
With the GitHub App, administrators of Orca can connect to GitHub organizations and accounts, enumerating all repositories and integrating Orca’s scanning into them. They can also tailor policy to the repos, centrally managing what needs to be scanned for and what security issues will result in an enforcement action.
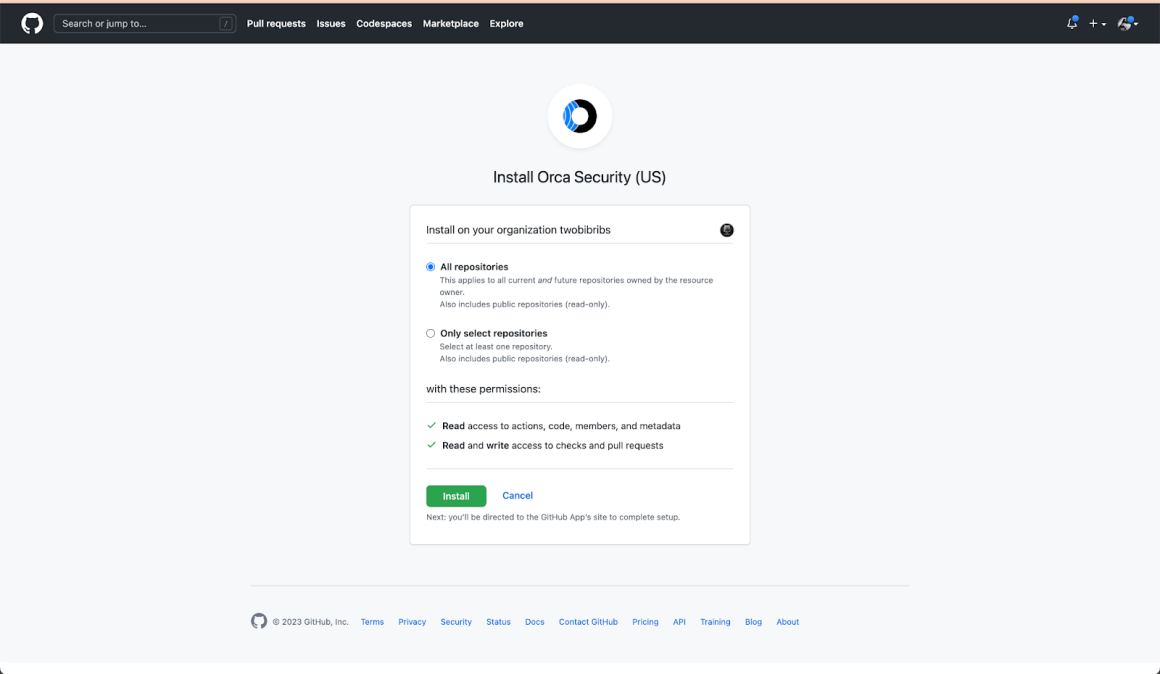
Once the organization/account is onboarded, administrators can easily onboard individual repositories or all of them at once. As new repositories are added, administrators are able to onboard them without additional authentication or friction. Additionally, repositories are onboarded with separation of duties maintained, with security teams lacking the access to make changes.
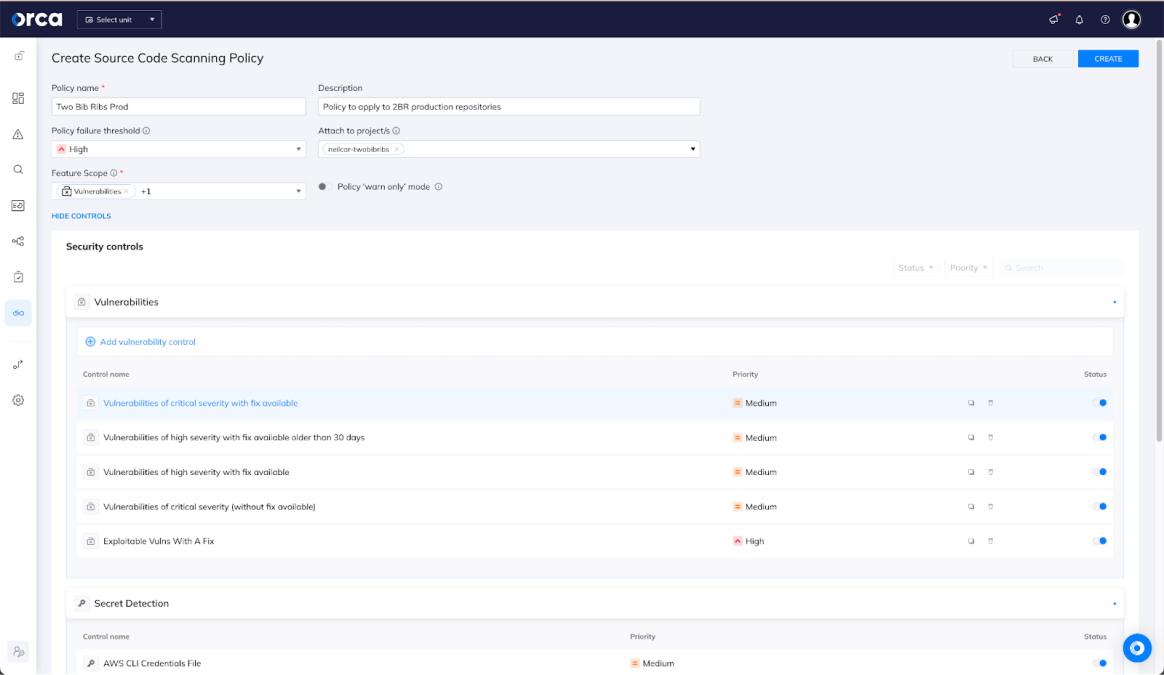
Centralized, Powerful Controls for Security Teams
Once the repository is onboard, security teams can easily create policies to find the problems they’re concerned about and, if desired, when to enforce the policy in order to block a problematic pull request. You can apply policies per-repo, across groups of repos, or across all of the repos in the organization easily. In this example, we’re taking a conservative approach of only failing an operation if a vulnerability has a public exploit available; however, we’re still giving our developers a 15-day window from the discovery of the vulnerability to address it. Security teams have complete control over security policy applied in shift-left integration.
Developer Experience
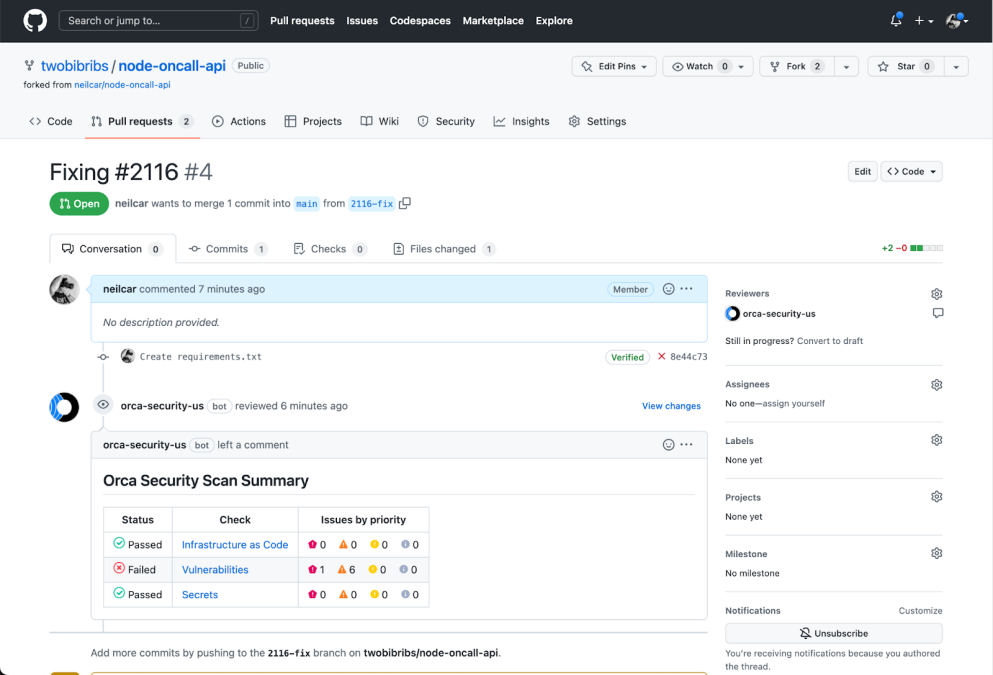
With our integration and policies in place, code will begin to be scanned automatically whenever a pull request is submitted to make a change to the codebase. When a repository is onboarded, Orca creates a baseline of the state of the code so that only the changes will be scanned on future pushes and pull requests, ensuring that the results are clear and actionable in the context of the pull request. For example, if we accidentally introduce a new vulnerability older than 15 days with an exploit available while fixing an issue, our pull request will be caught by Orca’s vulnerability scan and blocked until we resolve the issue.
This is familiar territory for modern developers – just as failures in other automated unit, integration, and performance tests may result in errors that have to be remediated before shipping, now security tests show up in the same way.
Conclusion: Centralize Deploying and Managing Shift-Left Scanning
By centralizing the integration and configuration of scanning repositories for adherence to security policy, Orca helps our customers realize the promise of shift-left security. Security teams can easily apply controls early in the application lifecycle while DevOps teams gain security insight without having to manage the integration themselves.
This is only the beginning, though – we have big plans to keep extending what security and DevOps teams can accomplish with Orca Security.
To gain more insights into evolving a shift-left culture within your organization and how your teams can leverage the functionality available from the Orca Platform, download Orca’s “5 Requirements to Shift Security Left” ebook. You can also sign up for a free trial and walk through a demo of how the Orca Cloud Security Platform can support your organization’s security and risk-mitigation objectives.