After raising $550M this year from top investors such as Temasek, CapitalG (Alphabet’s VC arm), RedPoint, GGV, Iconiq Capital, Lone Pine, Stripes, Adams Street, Redpoint Ventures, Harmony, Splunk, SAIC, and more, at this point I should probably be writing about how Orca Security is providing a single ‘AI-powered, military grade’ cyber gimmick that solves all cybersecurity problems. That’s the standard claim-to-fame of other cyber offerings – to provide solutions so smart that they solve cybersecurity for you.
- Unpatched server facing the internet? No problem – buy an IPS so smart it’s able in real-time and with 0% false positives to distinguish exploits from your legitimate traffic and keep you safe.
- Administrative user with a password of 123456 and no MFA? No sweat – buy a CASB so intelligent it’ll deduce an attack is underway by its location data.
- An attacker managed to already infiltrate your systems? Don’t worry, buy an AI-powered EDR solution to detect it in real-time and block it from moving laterally.
The cyber security industry made billions selling these kinds of gimmicks. But there is a slight problem – they work mostly in Hollywood movies.
There are many reasons why there are no easy fixes. The risk of false positives and their impact on business continuity is a major one. I wouldn’t want to travel on a plane with an AI-based cyber tool with a ‘block’ policy enabled on its critical systems bus. Many times, these are overpriced signature matching devices that can be evaded in a few minutes’ work.
As an example, we recently showed that the runtime protection mechanisms of Palo Alto Networks Prisma Cloud – one of the world’s largest cybersecurity players – can be evaded using extremely basic techniques:
- Cryptominer detection stops working if you change the ‘cryptominer’ name to ‘trustworthyapplication’
- Lateral movement detection stops working if the hacker renames netcat from ‘nc’ to ‘notnc’
- Exploit and malware detection misses most of the attacks
Don’t take my word for it – watch for yourself. This isn’t just an issue with Palo Alto Networks – it’s a common theme for most of these gimmicks. They might tell you they have a gazillion indicators of compromise (IoCs) in their DB but fail to mention that all attackers need to do to evade detection is to change their ransom message from ‘Your environment is encrypted’ to ‘We’ve encrypted your data’.
Orca is on a mission to help you solve the things that matter
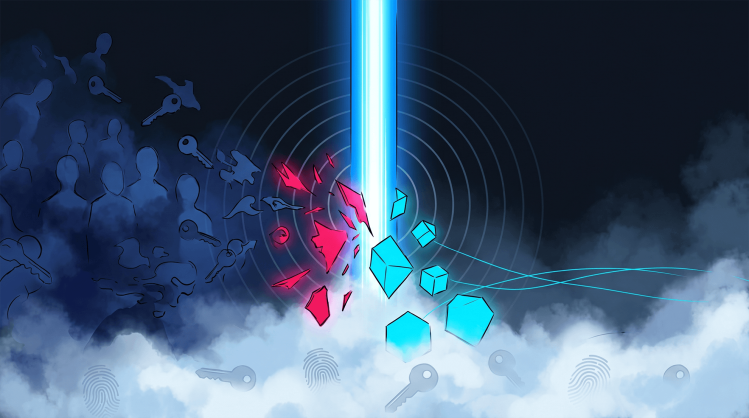
Any veteran cybersecurity professional knows that the highest reduction in risk comes from maintaining good IT hygiene vs. investing in these gimmicks. Patching an environment prevents an exploit with dramatically higher efficacy than IPS. Maintaining MFA reduces authentication risk far more than CASB. Employing the least privilege principle reduces the risk of lateral movement far greater than does any AI-powered gimmick.
Shifting-left for the cyber security industry is the best approach to reduce the risk.
But this used to be very hard. You had to install dozens of tools to merely find the risks – vulnerabilities, cloud misconfiguration, overly permissive roles, exposed sensitive data. There are at least a dozen risk categories you should be on the lookout for. Just getting a business to deploy the requisite tools could take years, and once installed, practitioners were faced with the daunting task of finding needles in the haystacks of millions of uncontextualized alerts. With such a dismal outlook, it isn’t surprising so many practitioners reverted to cybersecurity gimmickry.
Full coverage, comprehensive security, contextual prioritization
To tear away the security façade provided by the gimmicks, Orca Security invented a technology to find these issues at scale – in a way that actually works. Our patent-pending SideScanning™ technology enables Orca to cover your entire environment in minutes – guaranteeing thorough organizational coverage and no overlooked resources. And I’m talking in minutes instead of months (or even years).
We’re providing the worlds’ most comprehensive cloud security solution – detecting risks that normally would require half a dozen tools to handle. Most importantly, we don’t hand practitioners a list of a million ‘critical’ alerts and tell them to ‘go figure.’ Rather, Orca uses an innovative, graph-first contextual approach to prioritize the 0.1% of risks that really matter – freeing your security teams to spend their precious time on the truly critical attack vectors that can actually be exploited.
Sound too good to be true? Don’t take my word for it. Try it for yourself in minutes or read what our customers say about Orca.
This is the reason that all of these great investors invested $550M in Orca this year. It’s the reason Gartner named Orca a Cool Vendor, and why future-thinking organizations such as Robinhood, Databricks, Autodesk, Newscorp, NCR, and many others rely on Orca Security for their cloud security.
This is the time to mature your cyber posture beyond cyber gimmicks. Connect your first cloud account in minutes and see for yourself at orca.security/demo
Orca specializes in AWS Cloud Security, Google Cloud Platform Security, and Microsoft Azure Cloud Security.