This post was originally published on The New Stack.
Organizations want to move to the cloud to drive innovation and increase the speed at which they can adapt to ever-changing customer desires. That’s also a major reason why they are ultimately successful in adopting cloud technologies. With the increased focus on innovating at higher velocities, the rest of the organization has to drastically change how they do things just to keep up. They have to adhere to requirements ranging from identity management to regulations to committed service-level agreements. Innovation is amazing, but if it is not done in a sustainable way, it can cause more problems than it solves.
Visibility in the Cloud
An organization adopting cloud technologies requires full visibility into the cloud platforms and services that it uses. Cloud visibility involves access to all available telemetry data, including logs, policies, metrics, and trace data generated by the platform and services.
Achieving true cloud visibility is vital to ensuring that the organization is running a stable and secure environment that will keep customers happy. Not only will this encourage them to stick around, but it can even inspire them to refer new customers to the organization.
Secure Innovation in the Cloud
There are many ways that cloud visibility will help an organization. We’ll discuss four of the most common benefits below.
Embracing Flexibility
The cloud is often sold as the best way to give organizations more flexibility to adapt to market changes faster. They offer the ability to apply changes to services on the fly without requiring downtime for the change to take effect. However, this same benefit can be a huge drawback if someone applies a change to the wrong place or with the wrong criteria.
This flexibility can also expose the organization to risk in real time. Attackers are continually scanning cloud providers and large organizations to look for weaknesses. They can find even the most innocent mistake, such as when a vendor wants access to an internal-facing development system to help diagnose a problem, and someone opens up the system to the internet because it’s the fastest way to help. I mean, it’s only development; what can go wrong? If you have visibility into your cloud network policies, a change like this will become known immediately. This enables options like automated remediation and notification so that the proper team is alerted about the change.
Regulatory Compliance
Regardless of your chosen industry, there seems to be a constant flow of regulations that you’re expected to adhere to, from FDIC guidelines to the GDPR. If you don’t fully comply with them, it can result in fines and lost customer trust.
Some regulations and other government guidelines require that you take specific steps to ensure separation of duties between certain groups of employees in addition to requiring that you follow best practices like the principle of least privilege. As part of your organizational setup, there should be well-defined roles that follow these rules. Monitoring these roles to ensure that they adhere to the proper policies will not only reduce compliance risks, but also help identify potential attacks in progress if someone in the quality testing group is suddenly given access to production databases.
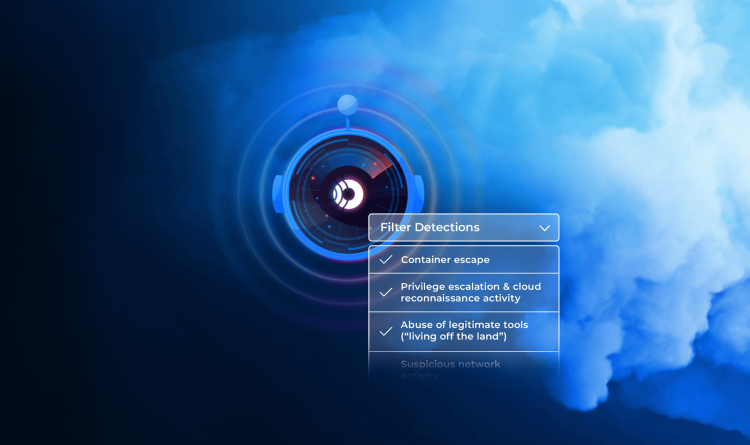
Vulnerability Detection and Management
Every year, it seems like new vulnerabilities are discovered in a growing number of products and services. Since developers now have the ability to dynamically deploy new applications without having to go through the formal (and traditionally manual) review process, it is vital that they have the capability to detect – and react to – newly discovered vulnerabilities across an ever-increasing number of applications.
Organizations usually empower their developers in this way through their DevOps practices and the use of agile methodologies. Typically, they use CI/CD pipelines in which they can embed scanning tools that will hopefully find vulnerabilities and block application deployments if anything critical is found. In addition, cloud security tools often contain products that are capable of detecting new applications running in an environment and continually scanning them for anomalies while they’re running. They can also detect whether newly discovered CVEs are applicable.
Data Management and Privacy
There are two sides to data management and privacy. The first is simply following the rules as outlined in laws like the EU’s General Data Protection Regulation (GDPR), Canada’s Personal Information Protection and Electronic Documents Act (PIPEDA) and the California Consumer Privacy Act (CPRA). The second side is preventing accidental disclosures – not to mention malicious ones.
If you can’t see the issue, you’ll never find it – or fix it. As Supreme Court Justice Louis Brandeis once said, “Sunshine is the best disinfectant.”
Conclusion: Leveraging Cloud Visibility for Maximum Innovation
As we have outlined in this post, there are several reasons why cloud visibility is vital to the success of your organization’s cloud journey. Innovation necessitates the ability to move fast. But just because you move fast doesn’t mean you can’t do things safely and securely. Ensuring that your chosen cloud platform continues to follow best practices and operate under the parameters you’ve specified is key to achieving an environment that will earn and keep your customers’ trust. Deploying a platform that’s capable of providing multicloud visibility – like the one offered by Orca Security – is a great place to start if you want to gain the cloud visibility and security you need to be successful.
Further Reading