Potentially Personal Identifying Information found – Email Addresses
Hazardous (3)
Non-platform specific
HITRUST, NIST 800-53, SOC 2
About Personal Identifiable Information
Personal identifiable information (PII) is any data that can be used to uniquely identify a person. PII examples include name, Social Security number, telephone number, retina scans, and MAC addresses (or device IDs).
PII is often the most sensitive and valuable data stored by an entity and therefore a prime target for threat actors. Securing it—both at rest and in transit—is critical, especially in the cloud. If PII gets into the hands of malicious actors, it can cause significant harm to the exposed persons as well as your organization. Possible consequences include identity theft, data breach, reputational damage, and regulatory fines.
Cloud Risk Description
Protecting PII in the cloud can be challenging given the size of the attack surface. Therefore, it’s important to never store it as plain text or in the same tables, schemas, or databases as other data. In addition, do not store plain text PII (e.g., email addresses) on cloud assets like VMs or containers.
How Can Orca Help?
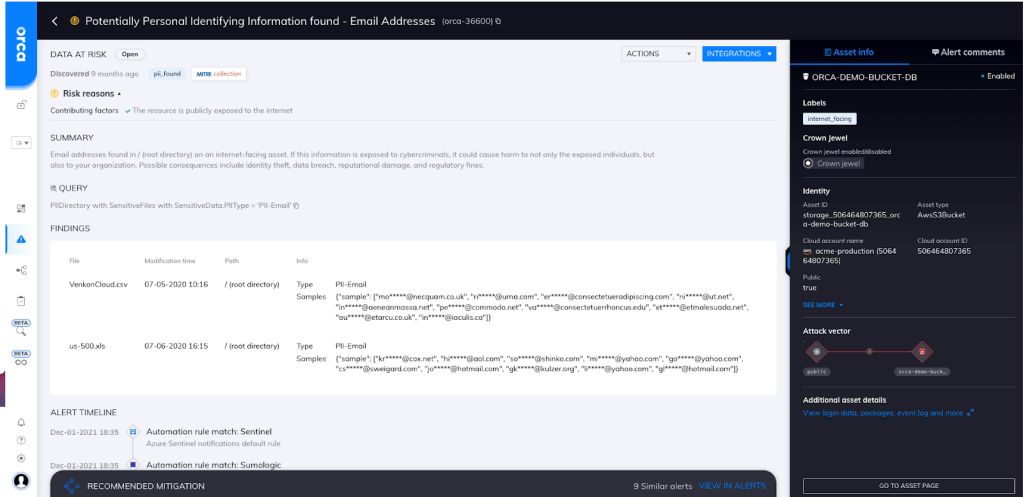
Orca detects sensitive data at risk across both the workload and control plane and, if found, dispatches an alert along with remediation steps and exact data location (see screenshot). Since leakage of such confidential data is also subject to security compliance regulations (and large fines), the alert is prioritized so that security teams will know to immediately remediate the issue.
Recommended Mitigation Strategies
-
Store PII in purpose-built, secure databases.
-
Use cryptographically strong encryption algorithms to encrypt PII, both at rest and in transit.
-
Never store sensitive information on a file system or hardcode it within source code.
-
Use tools such as AWS Comprehend to detect the presence of PII; remove or encrypt it accordingly.
-
Follow the principle of least privilege (PoLP) when granting access to PII data stores.
Useful Links
- The Challenge of Keeping PII Secure in the Cloud: https://community.idera.com/database-tools/blog/b/community_blog/posts/the-challenge-of-keeping-pii-secure-in-the-cloud
- Detecting PII entities – AWS: https://docs.aws.amazon.com/comprehend/latest/dg/how-pii.html
- How to Secure Personally Identifiable Information against Loss or Compromise: https://digitalguardian.com/blog/how-secure-personally-identifiable-information-against-loss-or-compromise
- How to protect PII under GDPR: https://www.csoonline.com/article/3215864/how-to-protect-pii-under-gdpr.html
Orca Security, the cloud security innovation leader, provides cloud-wide, workload-deep security and compliance for AWS, Azure, and GCP - without the gaps in coverage, alert fatigue, and operational costs of agents.
