Database with Potentially Personal Identifying Information found – Social Security Numbers
Hazardous (3)
Non-platform specific
About Personally Identifiable Information
Any data that can be used to uniquely identify a person is known as personally identifiable information (PII). Examples include first and last names, credit card numbers, retina scans, and Social Security numbers.
Virtually every organization stores PII, be it belonging to its customers, employees, partners, or vendors. Regardless of whose it is, protecting PII should be at the top of every organization’s security checklist.
Among all PII types, Social Security numbers (SSNs) pose the greatest privacy risk. Nothing can uniquely identify a person across disparate applications and systems more effectively. Exposure of a person’s SSN can potentially allow malicious actors to access their bank accounts, insurance information, driving records, and tax-related data.
The first step to protecting PII is to identify all the places that it exists. SSNs might exist in dedicated database tables, as well as other places in a system. For example, an application might write SSNs of active users to a log file. Similar log files could exist on multiple servers across your infrastructure. Or you might add SSNs to a database table that maps transactions with the users who made them.
It’s important to know exactly how and where security-critical information is used across your infrastructure. PII data should be segregated from all other data and stored in dedicated, secure data stores. It should never be stored as plaintext or directly in cloud assets such asVMs or containers.
Cloud Risk Description
Unencrypted Social Security numbers were found in a cloud asset. If exposed to cybercriminals, this could lead to identity theft and various kinds of fraud.
How Can Orca Help?
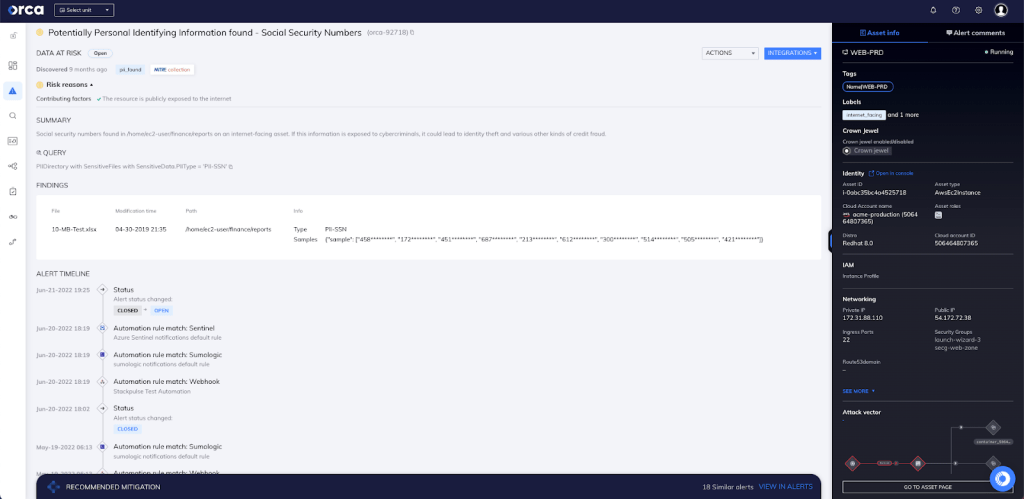
Orca detects sensitive data at risk across both the workload and control plane and, if found, dispatches an alert along with remediation steps and exact data location (see screenshot). Since leakage of such confidential data is also subject to security compliance regulations (and large fines), the alert is prioritized so that security teams will know to immediately remediate the issue.
Recommended Mitigation Strategies
-
Never store SSNs in cloud assets—especially not as plaintext.
-
Use cryptographically strong encryption algorithms to encrypt Social Security numbers, at rest and in transit.
-
Store SSNs in purpose-built, secure data stores.
-
Follow the principle of least privilege when granting access to data stores containing SSNs or other PII.
-
Use tools like AWS Comprehend to detect the presence of SSNs, thenremove or encrypt the data accordingly.
-
Never hardcode any Social Security numbers in applications source code or commit them to a GIT repository.
Useful Links
- Avoid Identity Theft: Protect Social Security Numbers: https://www.ssa.gov/phila/ProtectingSSNs.htm
- The Challenge of Keeping PII Secure in the Cloud: https://community.idera.com/database-tools/blog/b/community_blog/posts/the-challenge-of-keeping-pii-secure-in-the-cloud
- Detecting PII entities – AWS: https://docs.aws.amazon.com/comprehend/latest/dg/how-pii.html
- How to Secure Personally Identifiable Information against Loss or Compromise: https://digitalguardian.com/blog/how-secure-personally-identifiable-information-against-loss-or-compromise
- How to protect PII under GDPR: https://www.csoonline.com/article/3215864/how-to-protect-pii-under-gdpr.html
Orca Security, the cloud security innovation leader, provides cloud-wide, workload-deep security and compliance for AWS, Azure, and GCP - without the gaps in coverage, alert fatigue, and operational costs of agents.
