Database with Potentially Personal Identifying Information found – Personal Information
Hazardous (3)
Non-platform specific
About Personally Identifiable Information
Personally identifiable information (PII) is any piece of data that can be used to identify an individual such as first and last names, passport numbers, credit card numbers, patient identification numbers, and MAC addresses (or device IDs).
PII is often the most security-critical data possessed by an organization. Specialized measures must be taken to protect it, both at rest and in transit. The stakes are considerably higher if your infrastructure is built in the cloud.
Protecting PII in the cloud can be challenging. One misconfiguration can make PII stored in an S3 bucket susceptible to unauthorized access, and one unpatched system can put your entire infrastructure at risk of compromise. The attack surface on the cloud is exponentially larger than on premises.
With that said, if you have the right security controls in place, you can stay relatively safe. You must keep up with the changing cloud security dynamics and regularly patch your applications and systems for any discovered vulnerabilities.
You must also follow best practices for storing, processing, and transmitting personal information. For example, never store personal information as plaintext or in the same tables, schemas, or databases as other data. You must also never have any plaintext personal information, like email addresses, usernames, or mobile numbers, accessible on cloud assets like VMs or containers.
Cloud Risk Description
Personal information is found on a cloud asset. If this information is exposed to cybercriminals, it can lead to identity theft, data breaches, reputational damage, and regulatory penalties.
How Can Orca Help?
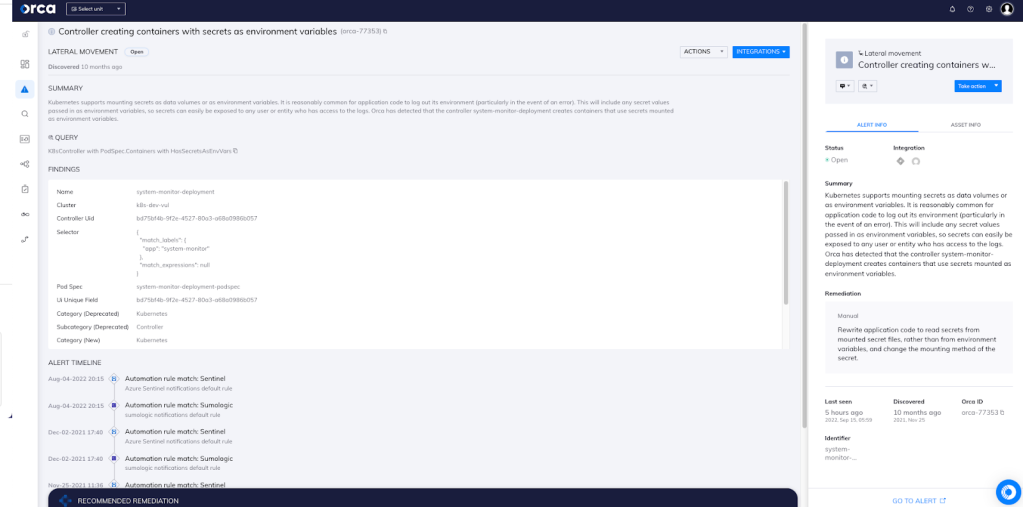
Orca detects sensitive data at risk across both the workload and control plane and, if found, dispatches an alert along with remediation steps and exact data location (see screenshot). Since leakage of such confidential data is also subject to security compliance regulations (and large fines), the alert is prioritized so that security teams will know to immediately remediate the issue.
Recommended Mitigation Strategies
-
Store personal information in purpose-built, secure databases.
-
Use cryptographically strong encryption algorithms to encrypt personal information, both at rest and in transit.
-
Never store any sensitive information on the file system or GIT repository, or hardcode it in source code.
-
Use tools like AWS Comprehend to detect the presence of personal information and remove or encrypt it accordingly.
-
Follow the principle of least privilege when granting access to data stores that contain personal information.
Useful Links
- https://docs.aws.amazon.com/comprehend/latest/dg/how-pii.html https://docs.aws.amazon.com/comprehend/latest/dg/how-pii.html
- Securing PII: https://digitalguardian.com/blog/how-secure-personally-identifiable-information-against-loss-or-compromise
- Protecting PII under GDPR: https://www.csoonline.com/article/3215864/how-to-protect-pii-under-gdpr.html
Orca Security, the cloud security innovation leader, provides cloud-wide, workload-deep security and compliance for AWS, Azure, and GCP - without the gaps in coverage, alert fatigue, and operational costs of agents.
