All articles by The Orca Security Team
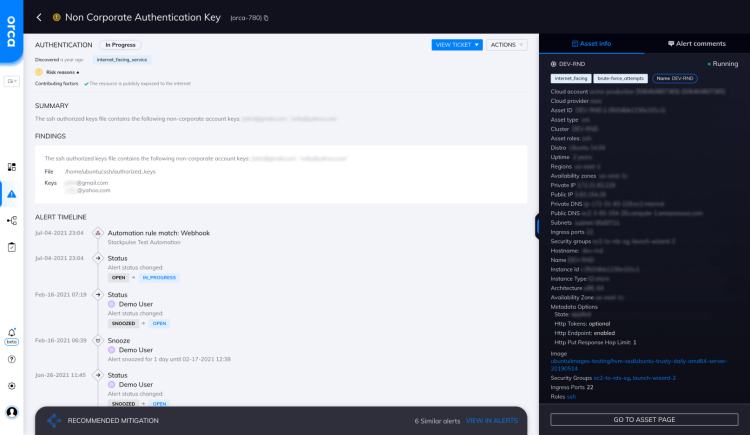
Non-Corporate Authentication Key
The SSH authorized_keys file contains the following non-corporate account keys: 'xxx@gmail.com', 'xxx@yahoo.com'. Illegitimately added keys usually have non-corporate usernames and...
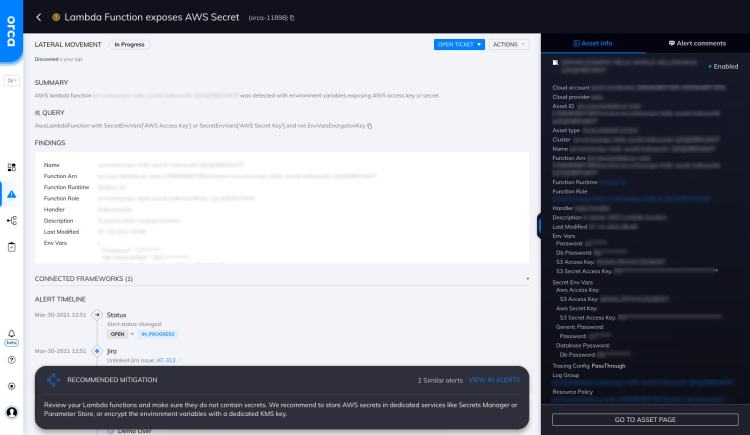
Lambda Function Exposes AWS Secret
AWS lambda function {AwsLambdaFunction} was detected with environment variables exposing AWS access key or secret.
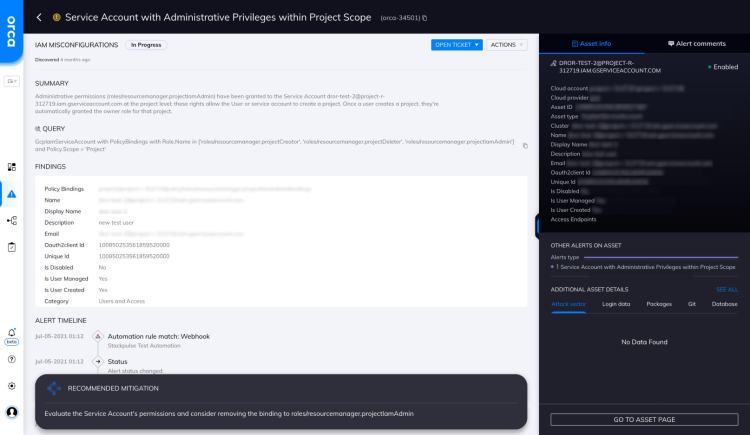
Service Account with Administrative Privileges within Project Scope
Administrative permissions ({PolicyBindings.Role}) have been granted to the Service Account {GcpIamServiceAccount} at the project level; these rights allow the User...
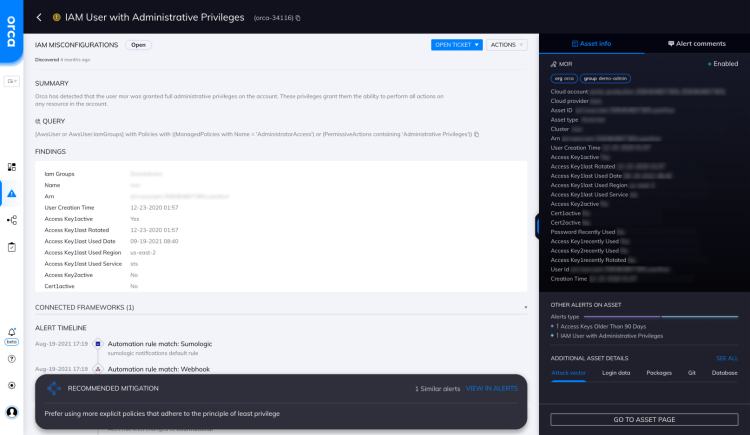
IAM User with Administrative Privileges
Orca has detected that the user {AwsUser} was granted full administrative privileges on the account. These privileges grant them the...