Modern enterprises are robust and complex, with many distributed teams responsible for configuring cloud environments, building and deploying applications, and managing risk.
While security leadership wants to ensure they have a global view into their entire cloud footprint, individual teams or business units have their own goals, responsibilities, and metrics.
Cloud security tools need to assist security teams, and their leadership, with the right segmentation and reporting, which we aim to address at Orca Security.
Cloud Security Involves Multiple Teams Across an Organization
There are many teams involved with building cloud environments and bringing applications to market. Importantly, they all share a diverse set of responsibilities.
In the report Cloud Security is a Team Sport by 451 Research, the author explains the various roles across platform architecture, development, DevOps and application delivery, security, and compliance.
Each team member and overall group has their own distinct goals. Meanwhile, these teams also play critical roles to support the security posture, vulnerability status, and compliance requirements of their organization’s environments.
Importantly, organizations have specific risks to manage and prioritize when it comes to cloud security.
When surveyed, security leaders reported their top three cloud security concerns as 1) loss of control of sensitive data, 2) auditability, and 3) compliance-related issues, as shown below.
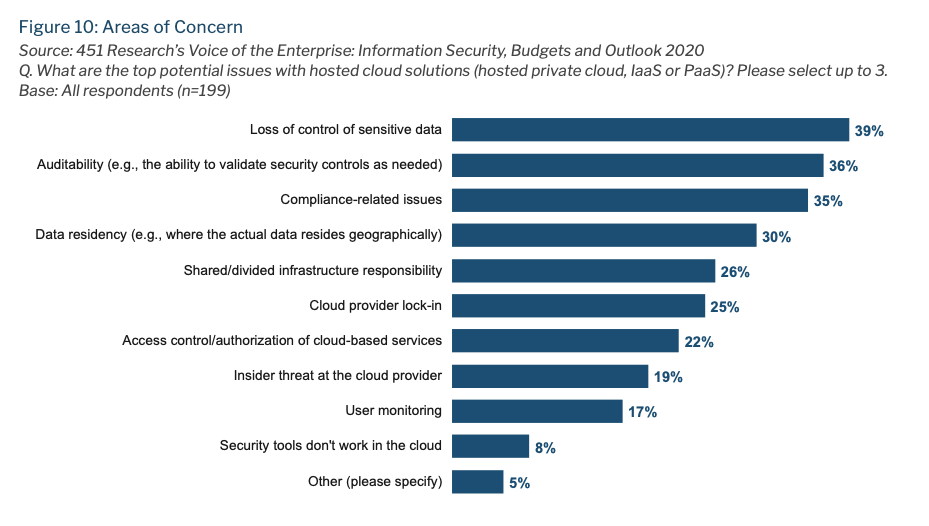
451 Research: Cloud Security is a Team Sport data on Areas of Concern in the Cloud
Cloud Security Reporting Can Help Teams Measure Progress
Cybersecurity risk management in the cloud requires a proactive approach from security leaders today.
Cloud security requires the right experts, technology, and governance to be in place, as the cloud security landscape and development lifecycles are evolving at a clip that is unprecedented – leading to more security breaches.
One of the best ways to manage cybersecurity risk is to prioritize business critical risks by the organization’s preferred risk tolerance.
A proactive cloud security program should involve the relevant stakeholders that manage internet-connected applications, data, and users in the public cloud by business unit, along with compliance, technology, and executive stakeholders.
In order to help organizations segment findings and view security results, the Orca Cloud Security Platform features an Organization Dashboard that allows teams to segment risks, gauge metrics, and report findings based on Cloud Vendor, Business Unit, or Accounts.
This ensures that teams have both comprehensive visibility in place to work with cross-functional teams, and cloud security metrics reporting to audit risks and compliance.
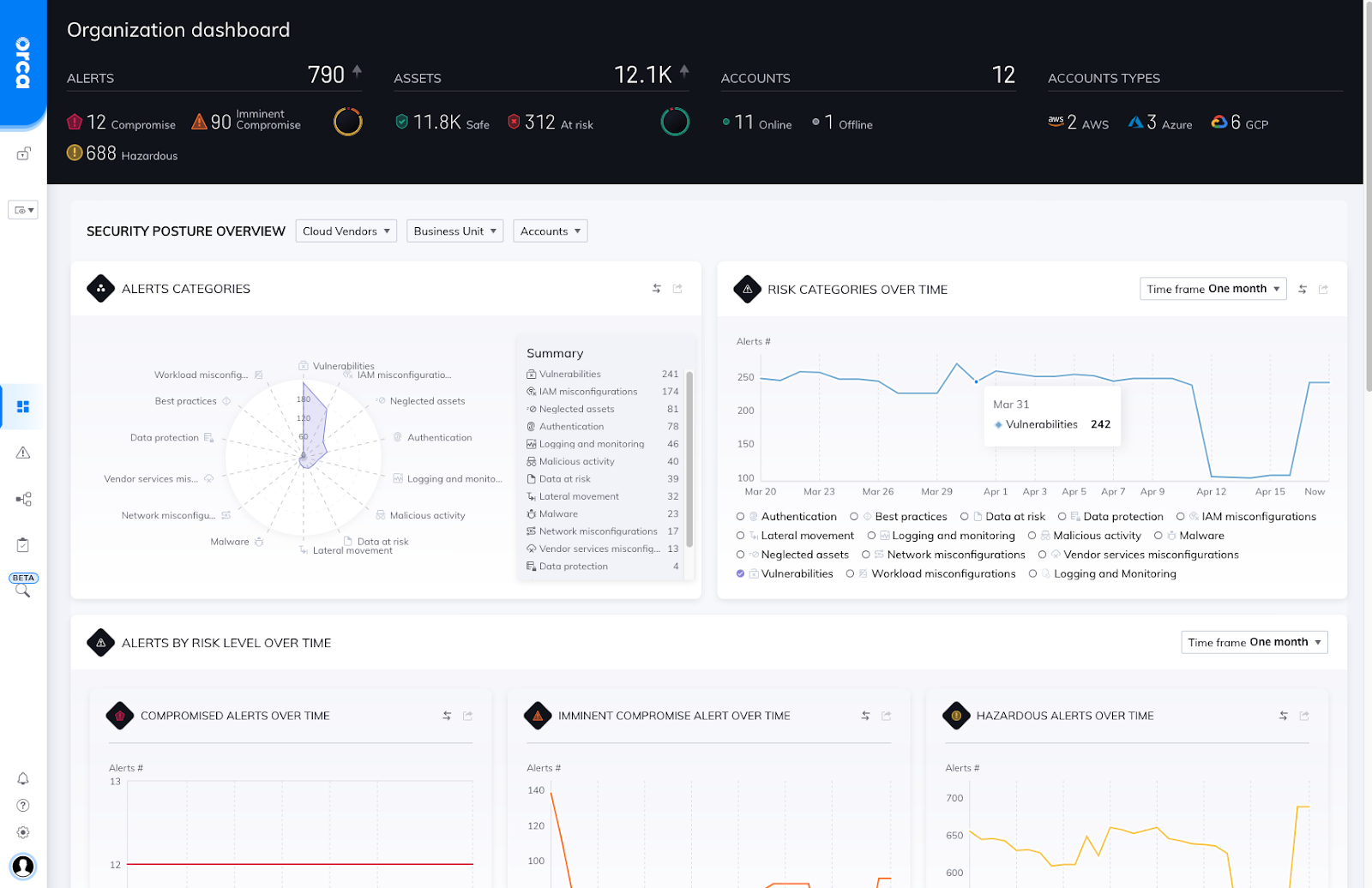
Orca Organization Dashboard showing global findings
The Organization Dashboard is highly configurable, showing findings across Alert Categories, Risks over time, Alerts over time, Compliance findings, and more.
For example, users can quickly understand how a specific Cloud, Business Unit or set of Accounts is meeting PCI compliance policies or how quickly a development group is remediating risks over time.
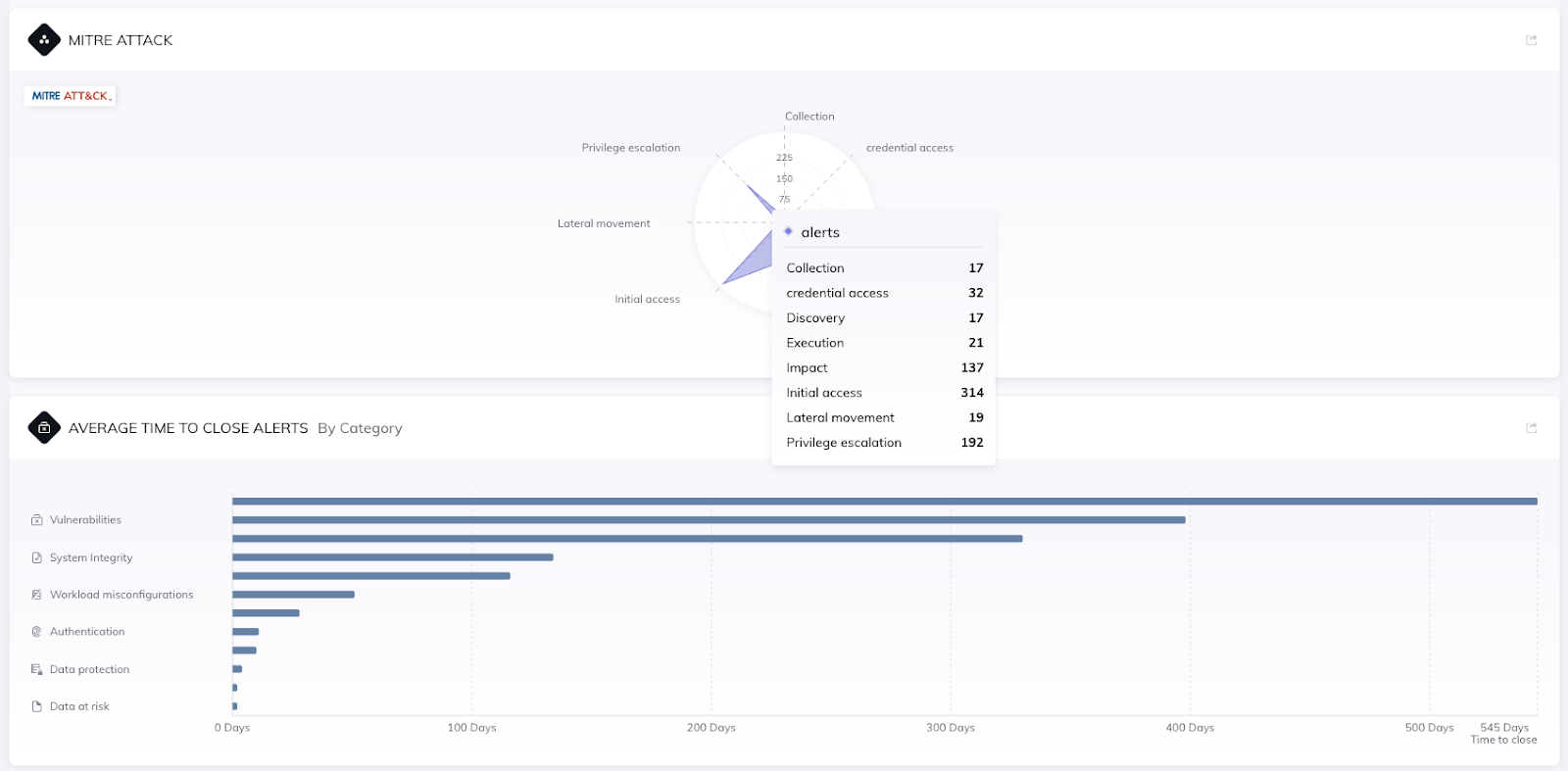
Orca UI highlighting MITRE framework and average time to close alerts
All of the data and the dashboards are configurable to support any organization with their unique cloud security requirements.
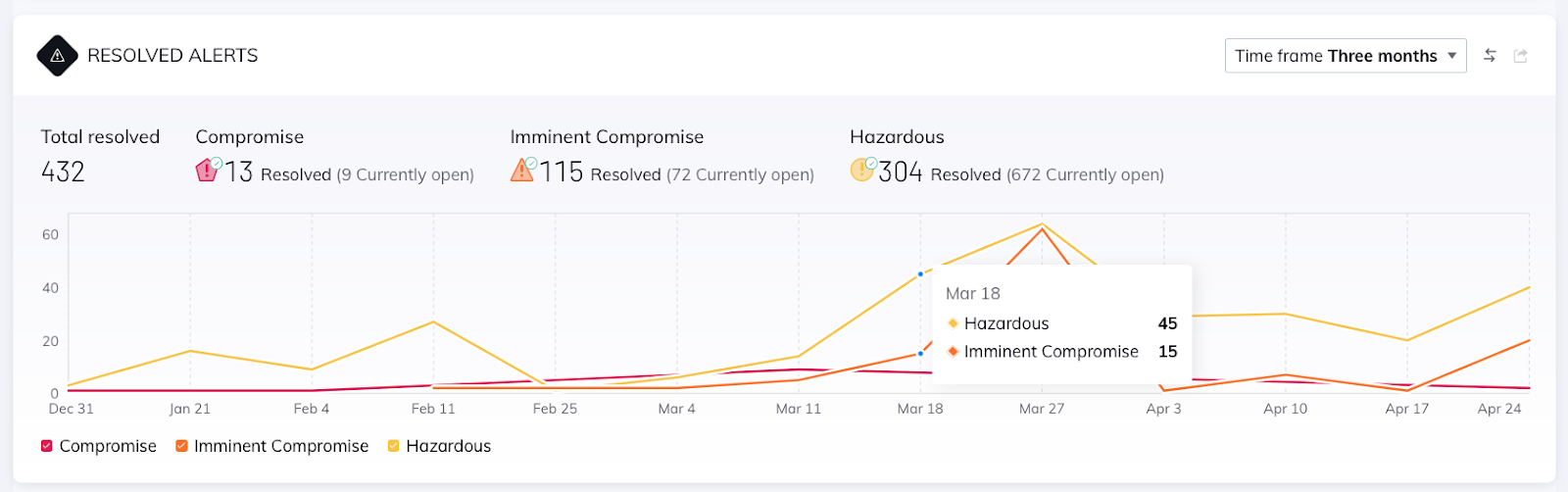
Orca UI covering Resolved Alert data
As we work with customers across verticals, we find that they have an overall goal to improve their cloud security outcomes – but they want to measure risk, compliance, and other data in unique ways. The organizational dashboard supports flexibility to support a customer’s unique requirements.
4 Scenarios for Segmenting Cloud Security Metrics
Below, I’ve highlighted several scenarios that are common for our users when employing important cloud security metrics.
Scenario 1: Measuring Cloud Security Findings Across Multi-Cloud Environments
According to 451 Research, 72% of organizations use two or more cloud providers. In these multi-cloud environments, security teams ultimately want a comprehensive view of their risks across all of their cloud environments with a unified set of policies and reporting. At the same time, many at the organization focus exclusively on only one of the clouds.
For this scenario, companies want a simple, straightforward way to view findings and manage policies mapped to a single cloud provider.
In this case, users can quickly use Orca’s Cloud filter to sort results and findings based on the specific cloud that is important to them and their related teams.
Scenario 2: Viewing Cloud Security by Compliance Requirement
Organizations may have anywhere between dozens to hundreds to thousands of workloads and applications.
This proliferation is especially notable for applications that are built using microservices architectures.
Importantly, not all workloads, applications, or environments are created equal from a compliance point-of-view. Some may need to meet PCI compliance standards, while others may need to meet CSP-specific requirements or other CIS Benchmarks.
In these scenarios, security teams, in partnership with compliance teams, want to segment Clouds, Accounts, or Business Units based on a specific compliance requirement.
By providing this capability in the Orca Security Organization Dashboard, users can save time and effort in configuring and tracking this data manually.
Scenario 3: Segmenting Risks Separately Between Development Versus Production Teams
While teams want to achieve a high level of security across all of their environments and applications, they may have different standards between a development sandbox and a production environment.
For example, in a production runtime environment, security teams may have a larger number of security policies or a goal to remediate alerts quickly to avoid risk.
Here, the ability to filter findings and results allows security teams to map security to meet the needs of business and strengthen their remediation efforts.
Scenario 4: Sorting Findings and Cloud Security Metrics by Business Unit
Similar to the scenarios above, security teams want to report on cloud security metrics deeply aligned to specific business units.
In this way, company leadership can understand present risks, compliance status, and remediation status mapped by each business group.
Additionally, business units get security findings and data mapped to team responsibilities, goals, and KPIs.
Improve Cloud Security with Business-wide and Team-based Results
Being able to manage both global cloud security findings as well as department-level results and cloud security metrics allows companies to deeply understand the cloud security function at their organization.
Most importantly, security leaders that can share out relevant data, findings, and reports for in-house teams are able to succinctly address risks quickly and effectively, and ultimately save time and costs.
To see the Orca Cloud Security Platform in action, sign up for a free cloud risk assessment.




