We are excited to announce that the Orca Cloud Security Platform has been recognized as a Trust Award finalist in the Best Cloud Workload Protection Platform (CWPP) and Best Cloud Security Posture Management (CSPM) categories for the 2022 SC Media Awards. Now in its 25th year, the SC Awards are cybersecurity’s most prestigious and competitive program. Finalists are recognized for outstanding solutions, organizations, and people driving innovation and success in information security.
The 2022 SC Awards were the most competitive to date, with a record 800 entries received across 38 categories – a 21% increase over 2021. Entries for the SC Awards were judged by a world-class panel of industry leaders, from sectors including healthcare, financial services, manufacturing, consulting, and education, among others.
“Orca Security and other Trust award finalists reflect astonishing levels of innovation across the information security industry, and underscore vendor resilience and responsiveness to a rapidly evolving threat landscape,” said Jill Aitoro, Senior Vice President of Content Strategy at CyberRisk Alliance. “We are so proud to recognize leading products, people and companies through a trusted program that continues to attract both new entrants and industry mainstays that come back year after year.”
Unifying CSPM and CWPP in one platform
We are especially honored to be named as a finalist in both categories, since we believe that what truly sets Orca Security apart is the fact that the Orca Cloud Security Platform unifies CSPM and CWPP capabilities in a single, agentless platform.
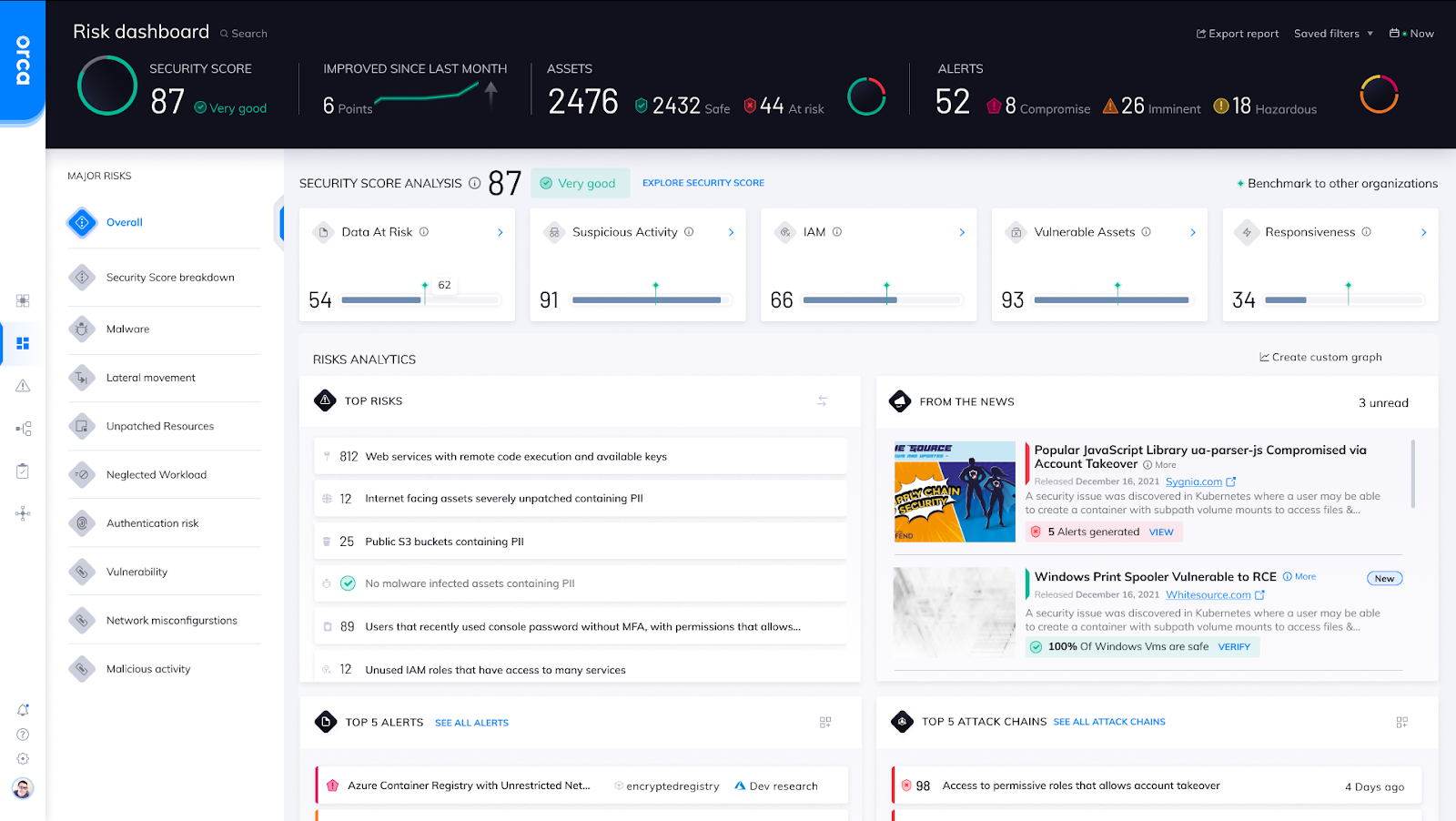
Instead of using agents, Orca’s SideScanningTM technology reads the workloads’ runtime block storage to obtain deep insight into workloads with 100% visibility across all assets. Combining this with configuration data pulled from cloud provider APIs, Orca is able to detect vulnerabilities, malware, misconfigurations, sensitive data at risk, IAM risk, lateral movement risk in cloud assets as well as in IaC templates and container images.
“Orca was built from the ground up with a unified data model, consolidating cloud workload, configuration, entitlement security, and sensitive data discovery in one platform,” said Avi Shua, CEO of Orca Security. “This model enables Orca to understand the full context of risks to accurately determine risk priority and recognize when seemingly unrelated issues can be combined to create dangerous attack paths.”
Benefits of agentless cloud security
Orca’s agentless Cloud Security Platform provides the following significant benefits:
- Fast time to value: Orca deploys in minutes – surfacing the most critical risks without the performance impact, organizational friction, coverage gaps and operational costs of agent-based solutions.
- 100% coverage with zero blindspots: Orca covers all of your cloud assets and automatically includes new assets as they are added, whether VMs, containers, Kubernetes, or serverless. Orca even discovers and monitors idle, paused, and stopped workloads, orphaned systems, and devices that don’t support agents.
- Reduced alert fatigue: Because Orca collects all the workload and configuration data in a single platform, it is able to understand the full context of risks and see which risk combinations create dangerous attack paths to the organization’s most critical assets.
- Lower cost and IT burden: Orca lowers TCO by eliminating countless IT hours spent installing and maintaining agents and sifting through thousands of low risk security alerts.
Orca customers
Orca Security is trusted by global innovators, including Databricks, NCR, Autodesk, Lemonade, and Gannett. Here is what some of our customers say:
“After years of dealing with agents, then seeing how easy it is to install and use Orca, I knew that its agentless approach was both a major innovation and a game changer.”
– Jeremy Turner, Senior Cloud Security Engineer, Paidy
“With Orca, we have our AWS configuration under control. We have over 12,000 assets. Currently – right at this moment – only three of them are listed as a priority to fix. That’s fantastic, particularly when you consider how frequently cloud environments change.” –
Jonathan Jaffe, CISO, Lemonade
Learn more
Interested in learning more about the Orca Cloud Security Platform? Download our Orca platform overview or watch a 10-minute demo. If you are ready to get more hands on, sign up for our free, no obligation 30-day risk assessment and see how we can simplify cloud security for your team.